API Threat Prevention
The Wallarm API Threat Prevention module, delivered on the Wallarm API Security Platform, provides comprehensive real-time API threat protection, allowing you to:
- Detect and mitigate advanced API threats which jeopardize your internal and end-user operations.
- Prevent API-focused abuse from bots and DDoS attacks which disrupt critical business services.

Do You Need API Threat Prevention?
As you adopt an API-first approach to support customers, partners and internal operations, you need API-focused protection of your growing API portfolio from these security challenges.

Growing Attack Surface
The explosive growth in API use, both internal and public-facing, is leading to a rapidly changing API portfolio with a great number of them unmanaged – which means a sizable and expanding attack surface.

Focused API Protection
OWASP API Security Top-10 risks (Injections, BOLA, RCE, etc.) and other advanced API threats are on the rise – which requires a new API-first security approach to mitigate organizational risk.

Sensitive Data Protection
More organizations are pushing more sensitive data through their APIs, including PII, financial & health data, credentials and more – which increases the danger and impact of unintentional or malicious disclosure.

API Abuse Prevention
API bot, L7 DDoS and other automated behavioral attacks are increasing – which can lead to ATO & carding attacks, disrupt end-user experience and put business-critical services at risk.


Comprehensive API Protection
Wallarm API Threat Prevention automates API threat protection and API abuse prevention with no manual rules configuration and ultra-low latency & false positives.
Coverage
Protect all your API assets regardless of protocol – from REST and SOAP to GraphQL, gRPC and WebSocket – from API-specific risks.
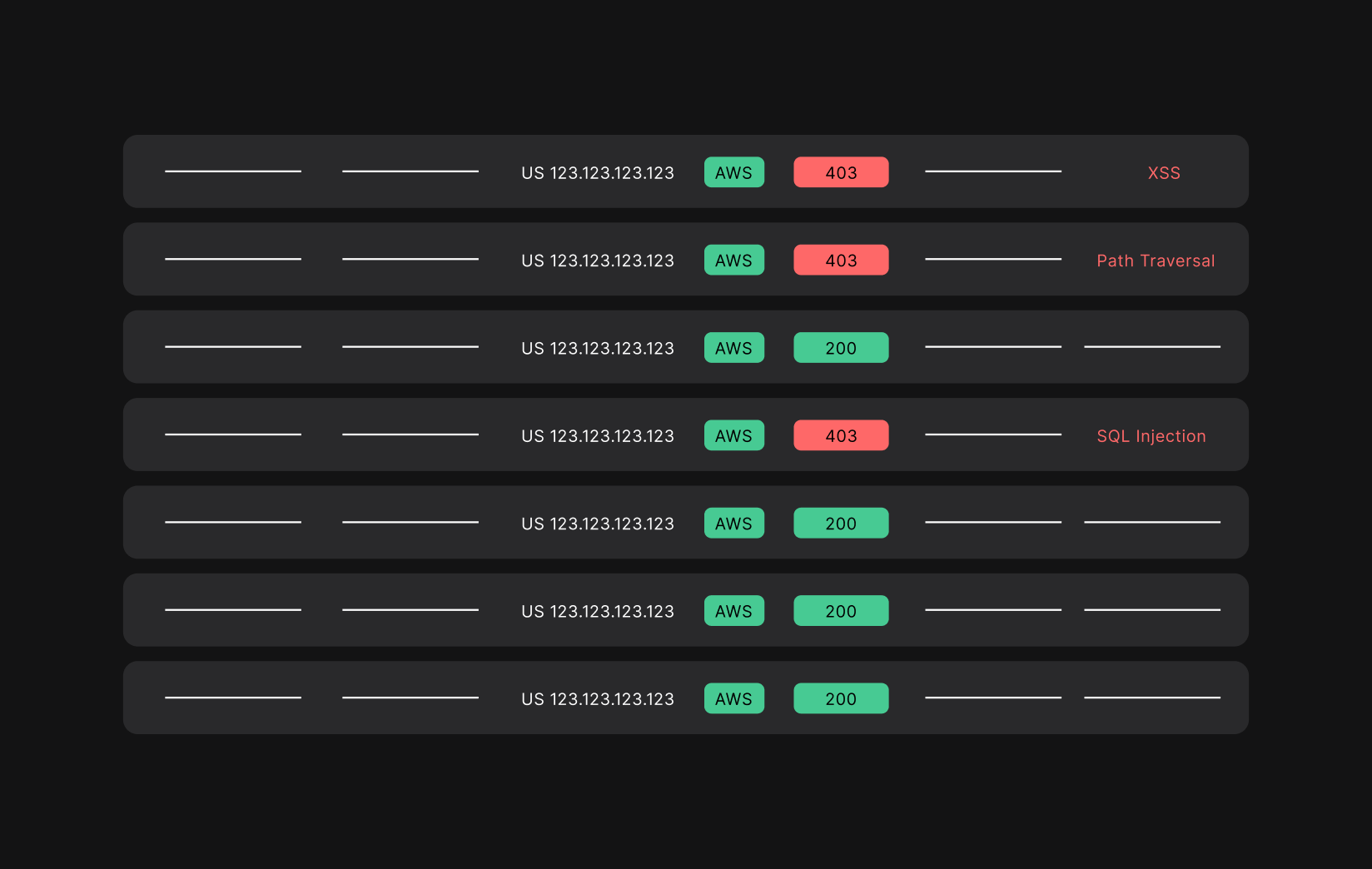
Detection
Identify, consolidate and prioritize unique API risks, from OWASP API Security Top-10 threats to API abuse, to optimize security team effectiveness and workload.
Response
Assess and remediate any weaknesses which open you up to attack and automatically implement rules to protect against any further assaults.
Security for Cloud-Native APIs
Wallarm API Threat Prevention provides comprehensive protection against API threats across your entire API portfolio.

OWASP API Security Top-10
- Provides full coverage against API-specific threats (Injections, BOLA, RCE, etc.)
- Delivers API threat detection & response via single tool

Advanced API Protection
- Enables session / token management to limit automated abuse
- Limits inappropriate exposure of sensitive data (PII, API keys, etc.)
- Continuously scans and mitigates vulnerabilities

Blocks API Abuse
- Stops application layer Denial-of-Service (L7 DoS), account takeover (ATO), and credential stuffing attacks with flexible rules
- Guards against crawler & stuffing bots, spiders and scanners

Full Protocol Support
- Supports REST, SOAP GraphQL, gRPC, WebSocket
- Recognizes different protocols / formats automatically and applies chain of parsers to detect encoded malicious payloads


Improve API Security. Maintain Privacy.
At the foundation of the Wallarm design ethos is privacy, flexibility and performance.

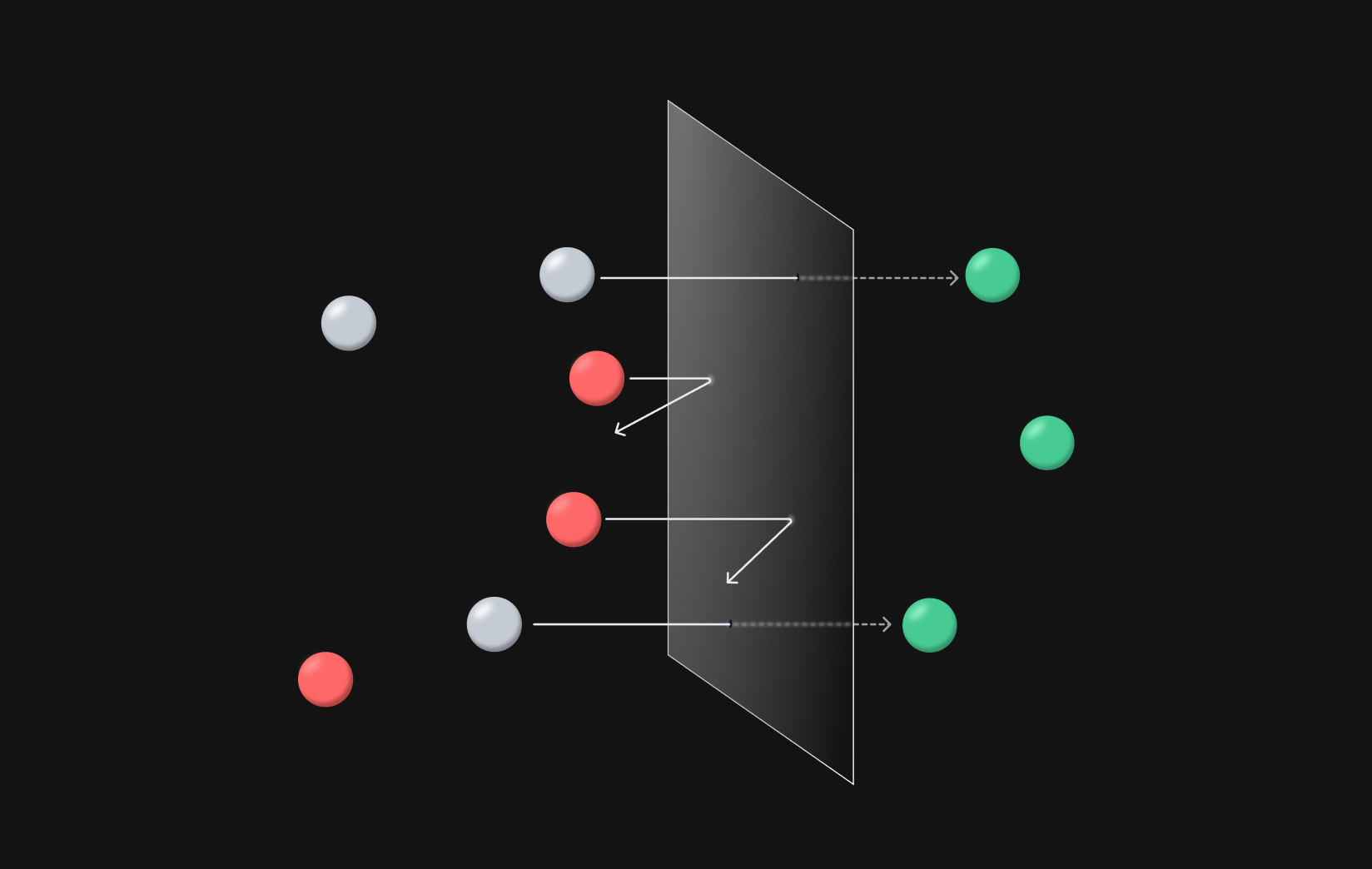
Inline deployment of our hybrid SaaS solution involves two main components: server-side software that deploys in your infrastructure within minutes and our powerful cloud-hosted analytics backend.
Privacy
Regularly monitor and review new API and web application threats & vulnerabilities 24/7 and add quick updates to the threat detection & mitigation systems – so you are staying ahead of attacks.
Flexibility
Continuously leverage the on-going data collection & analysis efforts of the Wallarm Research team for improvements in detection capabilities – so you are equipped with the best possible protection.
Performance
Read our quarterly API vulnerability report and learn why you need to set data-defensible remediation policies that engineers and executives will support.
Fast Deployment Everywhere
The unique architecture enables you to quickly install in diverse environments by mixing different deployment options—and yet manage everything with one unified console.

Security Edge
A simple DNS record change will route application traffic through the distributed network where Wallarm runs on the edge. This enables deployment as fast as 15 minutes and the benefits of a cloud service (such as CDN, cache, and others).

Cloud and multi-cloud
Jump-start deployment with pre-built images available in cloud providers' marketplaces, like AWS, GCP, MS Azure, or IBM Cloud. Get Wallarm up and running in any public or private cloud, or any combination of them.

Kubernetes or container-based infrastructure
Deploy Wallarm site-wide with the Ingress Controller or with the flexibility of an Envoy-based sidecar proxy for select services to enable both north-south and east-west traffic analysis.

API Management and Load Balancers
Deploy directly into your load balancers (e.g., NGINX, Envoy) or API Gateways (e.g., Kong) to avoid added complexity and inspect traffic with near-zero latency.

Private data center
Wallarm API Security platform is architected to provide the same web app and API protection in your private cloud and data centers as in public clouds.

Out-of-band deployment
For faster POV or when deploying inline is not an option, Wallarm can analyze your web app and API traffic by tapping to cloud-native technology (such as ePBF).
Cloud-Native Integrations
Wallarm integrates easily into your existing workflow, reducing learning curve and duplicative effort – and improving time‑to‑protection.
Incident Response
Integrate API security data into existing monitoring tools.
Security
Aggregate API security data into existing SIEM / SOAR tools.
Code Repo
Leverage real-time API security data in your CI/CD pipeline.
Communication
Enable seamless communications between teams.
Observability
Provide monitoring and alerting on API incidents.
Universal
Create custom integrations into existing tech stack.
Wallarm is the Leader in API Security
Don't just take it from us. Read what security leaders and practitioners think about our platform.
read reviews
Delivers advanced API security

In any environment
- AWS, GCP, Azure, IBM Cloud
- Private, Hybrid and Multi-Cloud
- Kubernetes / Service Mesh
- Zero-Trust

Against sophisticated API threats
- OWASP Top-10 Risks and Sophisticated API Threats
- API Abuse (bots, L7 DDoS)
- Account Takeover (ATO) / Credential Stuffing
Learn how Wallarm improves API Protection for best-industry companies
Ready to protect your APIs?
Wallarm helps you develop fast and stay secure.
See Wallarm's API Protection In Action























