See Wallarm's API Protection In Action


Know Your API Security Exposure, Instantly
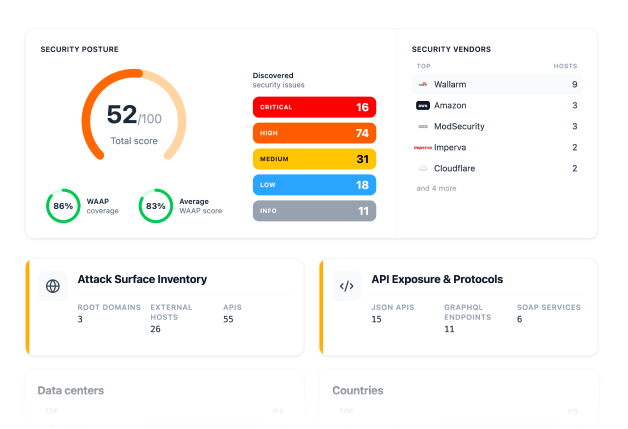
Instantly scan your domain to uncover exposed APIs, security gaps, and risk areas you can’t see from the outside.



You can’t secure what you can’t see

APIs are now a major attack surface, yet many teams lack a clear view of what’s publicly exposed outside their perimeter. Shadow APIs and misconfigurations often exist without visibility or ownership.
The API Security Report Card gives you a fast, external view of your API exposure, before attackers find it.
What you’ll get in your API
Security Report Card
A fast, high-level view of your external API security posture.
A list of your externally exposed APIs
Scan for leaked API keys and tokens
Detect common security vulnerabilities
Check if APIs are protected by firewalls
How it works
1
Enter your domain
2
We scan your publicly accessible APIs
3
You receive your API Security Report Card
Trusted by Security.
Attackers don’t care that you watch them, they only care if you stop them. That’s why Wallarm is the preferred choice for Security teams seeking unparalleled protection and prevention capabilities.
#1
In customer reviews
160K+
APIs protected
Billions
APIs requests protected, daily
With Wallarm, we've been able to scale API protection to the scale we need and manage with our infrastructure-as-code approach.

Built by API security experts
This tool is powered by the same API security expertise behind Wallarm’s Attack Surface Management platform, used by security teams to protect production APIs at scale.
#1
In customer reviews
160K+
APIs Protected
Billions
API requests protected, daily
