See Wallarm's API Protection In Action

Moscone Center, San Francisco | Booth 3125
Get Your Free API Security Report Card At RSAC
Know where your API security stands—exposure, abuse risk, and runtime protection gaps—with a fast, expert-led assessment and tailored report.
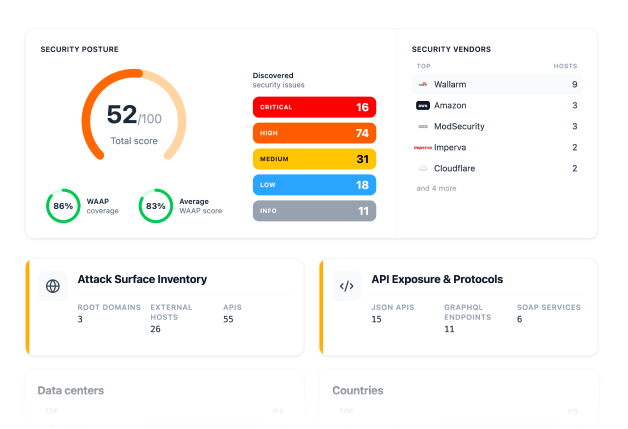
What’s in the API Security Report Card
API Exposure Snapshot
Abuse & Bot Risk Signals
Top Weaknesses
Action Plan
Benchmark View
Meet Wallarm at RSAC 2026
Dates: March 23–26, 2026
Location: Moscone Center, San Francisco
Booth: 3125
Stop by to get your API Security Report Card and walk through our Cyber Security Museum—a quick tour of how attackers evolved and why APIs are the new frontline.
The Cyber Security Museum (RSAC Booth 3125)

Enigma Machine

TBY-8 Radio

2600 Magazine

Blackberry 850

Scytale Cipher

Rosetta Stone

Caesar Cipher

Norton Antivirus
See Wallarm in Action
Stop by booth #4830 to learn about Wallarm’s enterprise API security. We’ll be demonstrating how Wallarm discovers and protects APIs and agentic AI. If you have revenue-critical APIs, Wallarm is the fastest, most effective tool for stopping attackers from compromising your business.


Join us for dinner
If the show floor isn’t your thing, or you just want to take advantage of the amazing restaurants in Vegas, join Wallarm for an executive dinner. We’ll be hosting exclusive dinners with our executives on Tuesday August 5, Wednesday August 6, and Thursday August 7. Request a seat at the table now.


Wallarmを試そう!
Meet With Us
Get Your Report Card
