White Hat Hacker
Introduction
White Hat programmers or hackers are individuals that do security assessments as a component of a business course of action. Albeit this idea is helpful in many cases, it has no legitimate or moral ramifications. When differentiated to the meaning of Black Hat, this nonappearance sticks out.
Regardless, this definition is the most famous importance related to white hat hacking. Moreso, it will suffice for our comprehension.

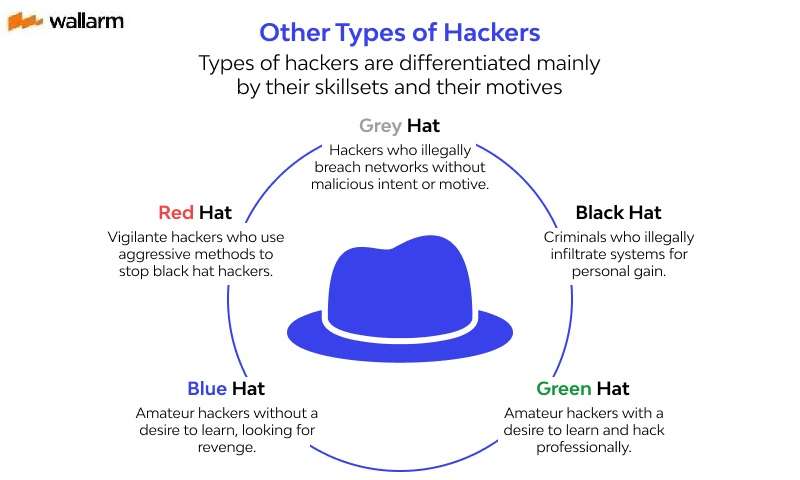
General hacker classifications
- White Hat Hacker

A "white hat hacker" (which you will be if you start as an "infiltration analyst") will be permitted to violate security for non-malevolent targets in order to remedy or patch vulnerabilities that have been discovered.

The "black hat hacker" is on the other extreme of the spectrum. A dark cap programmer will regularly endeavor to break into an ensured network to annihilate information or render the framework inoperable.

Grey hat hacking is a mix of an highly contrasting hat. A dark cap programmer may ride the web and hack into a PC framework for the sole reason for telling the executive that their framework has a security imperfection. They may then proposal to address the imperfection for an expense. Numerous sites, for example, Facebook and Ebay offer bug bounties (if it's not too much trouble, allude to Chapter 3 for more data), which implies that any individual who discovers a weakness or shortcoming can reveal the opening and get an award.
White Hat vs. Black Hat: Whats the Difference?
Before discussing the areas of convergence and divergence between proficient penetration analyzers and specialists of Ninjutsu. Nonetheless, we likewise need to comprehend the hatsacity of those that assault organizations and frameworks inside the domain of PC security, and recognize what has become a famous technique for distinguishing "heroes" and "miscreants" – white hats programmers and black hats programmers, individually.
The idea of two kinds of "hatss" start from old Westerns films, where the hero wears a white cowpoke hats and battles those with terrible expectation, who can be distinguished by their black cowhand hatss. It should was similarly as simple to recognize the "criminal" component in PC violations by what sort of hats they wear, yet the truth is significantly more hard to paint in shades of high contrast.
Numerous meanings of a black hats programmer attempt to interlace the idea of morals and ethical quality with the exercises of these "awful" programmers. The issue with remembering morals for any definition is that morals involves point of view; speculatively talking, a programmer situated in China who assaults government frameworks inside the United States might be viewed as one of the heroes to the Chinese government in specific conditions, though that equivalent programmer would be viewed as one of the trouble makers to those living in the United States.
The failure to recognize the hero from the miscreant while joining moral viewpoints requires the need to characterize white and black hats in an unexpected way.
To muddle matters, there have been other people who have recommended black hats programmers likewise exist, which can be distinguished as programmers who fall some place in the middle of the activities of white and black hats. Dim hats programmers hypothetically have the advantage of extra adaptability in directing assaults when contrasted and white hat, yet by one way or another stay away from the negative social (and lawful) disgrace of being a black hat programmer, since they don't overstep the actual purpose of the law.
The inconvenience of adding the idea of a black hat in with the general mish-mash implies that it makes characterizing limits even that amount more troublesome when attempting to recognize contrasts among proper and improper conduct.
What do White Hat Hackers Do?
- Tactics
While infiltration testing focuses on assaulting programming and PC frameworks from the beginning – filtering ports, looking at known imperfections in conventions and applications running on the framework and fix establishments, for instance – moral hacking may incorporate different things. An out and out moral hack may incorporate messaging staff to request secret key subtleties, scrounging through leader's dustbins and generally breaking and entering, without the information and assent of the objectives. Just the proprietors, CEOs and Board Members (partners) who requested such a security audit of this extent know.
To attempt to repeat a portion of the damaging methods a genuine assault may utilize, moral programmers may orchestrate cloned test frameworks, or arrange a hack late around evening time while frameworks are less critical.[3] In latest cases these hacks sustain for the drawn out con (days, if not weeks, of long haul human invasion into an association). A few versions include leaving USB/streak key drives with a concealed auto-start code in a public location, as though the drive was forgotten and picked up by an unknowing employee.
Some different techniques for doing these include:
- DoS assaults
- Social designing strategies
- Imitatition engineering
- Organization security
- Plate and memory criminology
- Weakness research
- Security scanners like
- W3af
- Nessus
- Burp suite
- Structures like
- Metasploit
- Preparing Platforms
These strategies distinguish and misuse known security weaknesses and endeavor to dodge security to acquire passage into got regions. They can do this by concealing programming and framework 'secondary passages' that can be utilized as a connection to data or access that a non-moral programmer, otherwise called 'dark cap' or 'dim cap', might need to reach.
White hat programmers have long provided penetration testing (also known as pentesting) services in the corporate security industry. In ordinary pentesting commitment, white cap programmers are recruited by associations that are hoping to reinforce their safeguards. These white cap programmers then, at that point try to hack into their customer's organizations.
At times, they might be given a wide contract to attempt to assault explicit resources, like private organizations, applications, and endpoints. On the other hand, they might be given an expansive command to uncover security holes, any place they might be.
By utilizing skilled programmers to discover holes, security groups can all the more likely test their protections. Along these lines, these groups can accordingly be better situated to kill holes and reinforce their guards—before a genuine assault occurs. In view of the experiences a white cap programmer uncovers, groups may have to set up new strategies, update or change setups, or refresh or supplant instruments.
Utilizing genuine assault methods to proactively discover shortcoming is the awesome best way to really demonstrate the viability of safety guards. White cap programmers frequently utilize similar apparatuses and strategies as their dark cap partners.
The methods utilized can go from basic public "root packs" with reported methodologies, to mind boggling and modern missions that may incorporate social designing, abusing endpoint weaknesses, introducing assault baits, mocking conventions, and the sky is the limit from there.
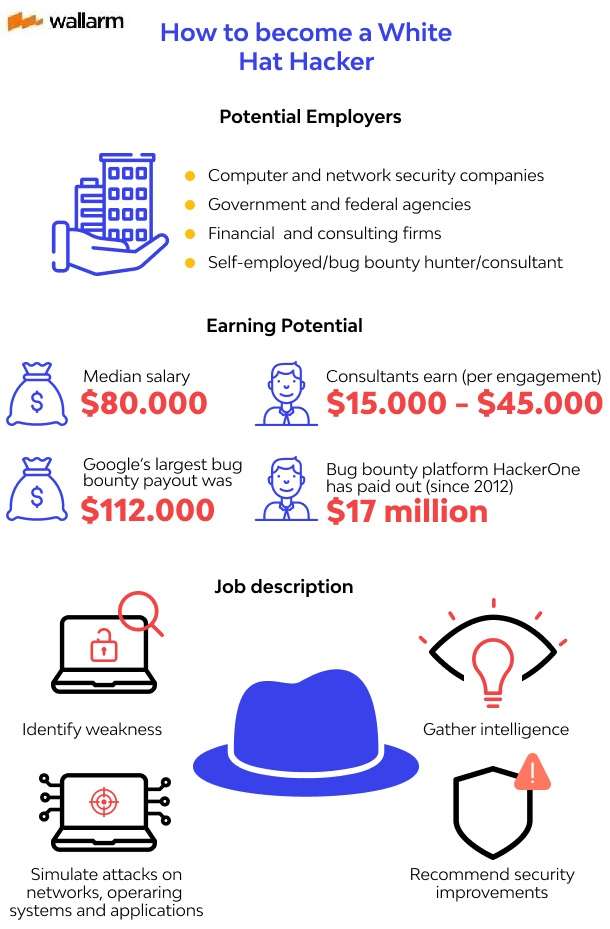
Get a Job as an Ethical Hacker
While the expression "hacker" might not have the best reputation in the present dictionary, it truly alludes to a different gathering of specialists with an assortment of intentions. Look at the whole infographic beneath to find more about the different kinds of programmers, just as how to turn into a white cap programmer.
Top 11 hackers
- Tim Berners-Lee
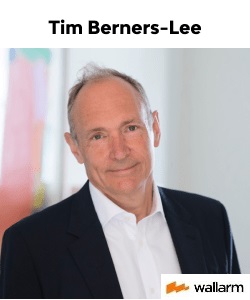
Arguably the most popular name in software engineering, Berners-Lee is the organizer of the World Wide Web. Today he fills in as the head of the World Wide Web Consortium (W3C), which regulates the improvement of the web.
- Greg Hoglund
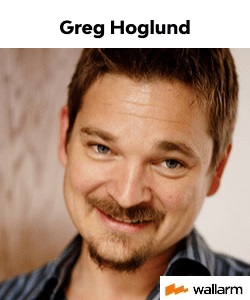
PC legal sciences master Hoglund is most popular for his work and examination commitments in malware identification, rootkits and web based game hacking. Previously, he worked for the U.S. government and the knowledge local area.
- Richard M. Stallman
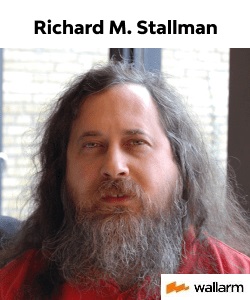
Author of the GNU project, a free programming project that elevates opportunity with respect to the utilization of PCs, Stallman is a great representation of a "hero" programmer. Stallman established the free programming development during the 1980s, with the possibility that PCs are intended to help participation, not thwart it.
- Dan Kaminsky
A notable figure inside the network protection world, Kaminsky is the central researcher of White Ops, a firm that identifies malware movement by means of JavaScript. He's most popular for finding a basic stream in the Domain Name System (DNS) convention that would permit programmers to perform boundless store harming assaults.
- Jeff Moss
Moral programmer Jeff Moss served on the U.S. Country Security Advisory Council during the Barack Obama organization and co-led the gathering's Task Force on CyberSkills. He likewise established programmer gatherings Black Hat and DEFCON, and is an official at the Global Commission on the Stability of Cyberspace.
- Charlie Miller

Mill operator, who's to a great extent popular for discovering Apple weaknesses and winning the notable Pwn2Own PC hacking challenge in 2008, has additionally functioned as a moral programmer for the National Security Agency.
- Linus Torvalds
Computer programmer Torvalds made and fostered the Linux portion, which is the part which in the end turned into the center of the Linux group of working frameworks.
- Kevin Mitnick

When quite possibly the most famous dark cap programmers around, Mitnick turned into a white cap programmer after an exceptionally plugged FBI pursuit landed him in prison for PC hacking and wire misrepresentation. Today, he runs Mitnick Security Consulting, which performs security and entrance testing for organizations.
- Tsutomu Shimomura
White cap programmer Shmomura is most popular for helping the FBI in bringing down Mitnick after the dark cap actually assaulted Shimomura's PCs.
- Marc Maiffret
.jpg)
Presently the main innovation official at a main security the board organization, Maiffret's awards incorporate the creation of one of the primary weakness the executives and web application items. He's likewise credited with finding a portion of the primary significant weaknesses in Microsoft programming, including Code Red, the principal Microsoft PC worm.
- Ivan Novikov

Ivan is the founder of Wallarm, an artificial intelligence-based security company based in Silicon Valley. Ivan is well known in the industry. He is the recipient of numerous bug bounty awards from companies such as Google, Facebook and Honewell. Ivan is also a frequent speaker at industry events and is known as the inventor of memcached injections and for his work in server-side request forgery (SSRF).
Ivan Novikov is an API security expert, bug hunter, security researcher, and blackjack speaker with years of experience in cybersecurity. He has spent decades in the industry and has witnessed both exploits and growth.
How can I become a white hat hacker?
Other white hat hackers who were gotten changed to being moral hackers so they could follow their objectives without agonizing over being captured. Some white hat hackers were initially black hat hackers who turned out to be more moral as they became older.
Despite the fact that having an earnest premium in and love for security is all that resource, white hat hackers can profit from having undergrad or advanced educations in software engineering, data security, or math.
The accompanying certifications may likewise be helpful for those hopeful white hat hackers:
- The U.S. Branch of Defense acknowledges the seller unbiased certification Certified Ethical Hacker from EC-Council.
- Security Essentials Certification, GIAC Penetration Tester, GIAC Exploit Researcher, and GIAC Advanced Penetration Tester are instances of worldwide data confirmation affirmations.
- For white hat, having preparing or affirmation in PC legal sciences can be useful.
The Limitations of White Hat Hacking
Individuals wearing white caps have various disadvantages and limitations in the event that you consider security a contention between white hat and black hat hackers. The following are a couple of critical limitations:
- Restricted time. The fundamental differentiation between white cap and dark cap programmers is time. White hat hackers don't have quite a bit of it, however noxious programmers do. A white hat hacker might be given a day or even half a month in the wake of employing them to follow through with their responsibility and unveil their discoveries.
Generally, these individuals are obliged by issues with cost, timing, and labor. Black hat hackers, nonetheless, are industrious. These hackers have gained notoriety for requiring a long time to finish a mission. Thus, hackers enjoy a critical benefit since they can test incalculable assault techniques until they effectively undermine their objective organizations.
- Restricted testing degree. Pentesting is as often as possible utilized by white hat hackers who are keen on breaking into a business climate or resource. Penetration, nonetheless, is essentially one phase of a genuine cyberattack, or "digital demise chain," which alludes to the total technique. Significant parts of the eliminate chain incorporate moving around inside organizations and frameworks and afterward exfiltrating (taking) information back out.
Nonetheless, because of stresses over the impact these procedures might have on the organization, white hat hackers that perform pentesting seldom feature these exercises.
Basically, in the event that a setup issue is presented for the current week, a white hat hacker's careful examination from last week won't be a lot of purpose.
How to protect yourself from hackers
When was the last time you utilized Wi-Fi in a public spot? Pretty much every coffeehouse, library, air terminal, and lodging currently has a technique for you to utilize your telephone or other cell phone to get to the web. That infers that except if you've played it safe to get your information, programmers in the area may access the data on your telephone.
Here are few ways to protect yourself and vital information from hackers:
- Try not to get to individual or monetary information with public Wi-Fi.
This may appear like an easy decision, yet you'd be astonished the number of individuals check their ledgers or make buys with a Mastercard while utilizing public Wi-Fi. It's ideal to do those things on a protected association.
- Ignore or freeze things you don’t need.
Programmers can utilize certain highlights on your telephone to get at your data, area or association. Thus, rather than keeping your GPS, remote association and geo-following on constantly, simply turn them on when you need them.
- Pick your applications astutely.
Just download applications from dependable sources that have set up a decent standing. Ensure you update your product and applications consistently and dispose of old applications you don't utilize.
- Utilize a secret word, lock code or encryption.
Ensure your passwords are no less than eight characters in length, with a blend of upper and lower case, and incorporate numbers or different characters, and never utilize the auto-complete element for passwords. You can utilize the capacity encryption include on your telephone to ensure your private information, and set your screen to break following five minutes or less.
- Be doubtful about links.
In case you don't know about the source, don't utilize the connection or open the link.
- Delete or Trace
Ensure your information is secure if your cell phone is taken or lost. You can set up your gadget to bolt itself after a pre-set number of bombed sign in endeavors.
- Utilize a superior password.
Open codes like 0000 and 1234 are not difficult to recollect, but on the other hand they're not difficult to figure. All things considered, decide on a haphazardly produced, six-number password.
- Utilize two-factor validation.
Passwords are the main line of guard against PC programmers, however a subsequent layer helps security. Numerous destinations let you empower two-factor verification, which helps security since it expects you to type in a mathematical code – shipped off your telephone or email address – notwithstanding your secret word when signing in.
- Overlook spam.
Be careful with email messages from obscure gatherings, and never click on connections or open connections that go with them. Inbox spam channels have gotten very great at getting the most prominent spam. Yet, more modern phishing messages that impersonate your companions, relates and confided in organizations (like your bank) have gotten normal, so keep your eyes open for anything that looks or sounds dubious.
- Secure your network.
Switches don't for the most part accompany the most noteworthy security settings empowered. When setting up your organization, sign in to the switch, and set a secret key utilizing a protected, encoded arrangement. This keeps gatecrashers from penetrating your organization and playing with your settings.
Conclusion
As a white hat hacker, there are some significant focuses that you should recall. Make sure to instruct yourself consistently. This will assist you with developing.
You must be a ninja; this implies rushing to strike! Whenever you have discovered a weakness, jump on the chance to uncover it.
Lastly, breaking new ground is always a good thing. You can identify difficulties that designers may have overlooked and that various programmers are not keeping an eye on by deducing in a new way. Also, make sure to put your hacking skills to good use for everyone's interest!
Subscribe for the latest news









%20Attack.jpg)







