What is the Reverse Proxy Server?
Reverse proxies help in shielding web workers from assaults while further developing execution and dependability. Continue reading to learn more about data about forward and invert proxies.

What is a proxy server?
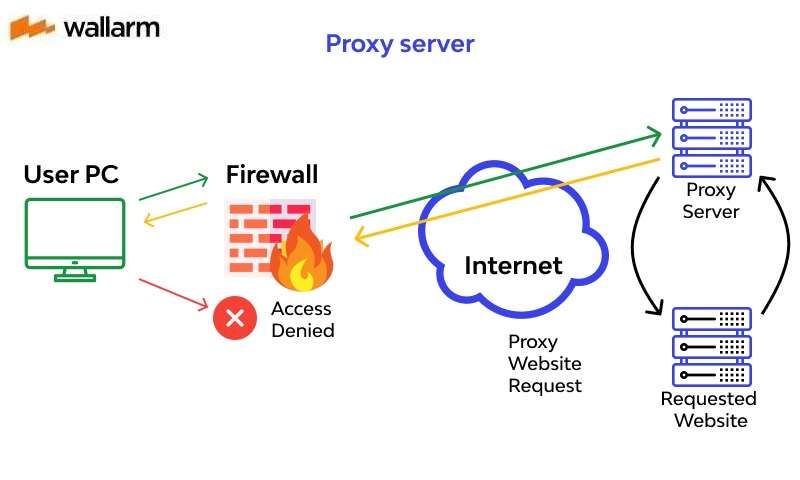
Forward proxies are commonly known as proxies, web proxies, or internet servers, are servers that sit before a gathering of customer machines. At the point when those PCs make solicitations to locales and administrations on the Internet, the intermediary worker captures those solicitations and afterward speaks with web workers for those customers, similar to a mediator.
For instance, how about we name 3 PCs engaged with an average forward intermediary correspondence:
A: This is a client's home PC
B: This is a forward proxy worker
C: This is a site's starting point worker (where the site information is put away)
In a standard Internet correspondence, PC A would connect straightforwardly to PC C, with the customer sending solicitations to the beginning worker and the beginning worker reacting to the customer. At the point when a forward proxy is set up, A will rather send solicitations to B, which will then, at that point forward the solicitation to C. C will then, at that point send a reaction to B, which will advance the reaction back to A.
For what reason would anybody add this additional agent to their Internet proceedings? There are a couple of reasons one should utilize a forward proxy:
To keep away from state or institutional perusing limitations - Some legislatures, schools, and different associations use firewalls to give their clients admittance to a restricted rendition of the Internet. A forward proxy can be utilized to get around these limitations, as they let the client associate with the intermediary instead of straightforwardly to the destinations they are visiting.
To impede admittance to certain substance - Conversely, intermediaries can likewise be set up to hinder a gathering of clients from getting to specific destinations. For instance, a school organization may be arranged to interface with the web through an intermediary which empowers content separating rules, declining to advance reactions from Facebook and other web-based media destinations.
To ensure their personality on the web - now and again, customary Internet clients basically want expanded namelessness on the web, however in different cases, Internet clients live in where the public authority can force genuine results to political nonconformists. Condemning the public authority in a web discussion or via web-based media can prompt fines or detainment for these clients. In the event that one of these nonconformists utilizes a forward proxy to associate with a site where they post politically touchy remarks, the IP address used to post the remarks will be more earnestly to follow back to the dissenter. Just the IP address of the intermediary worker will be apparent.
What is the Reverse Proxy?
Reverse proxies are workers that sit before web workers and advance customer (for example internet browser) solicitations to those web workers. Switch intermediaries are regularly executed to assist with expanding security, execution, and unwavering quality. To all the more likely see how an opposite intermediary functions and the advantages it can give, we should initially characterize what an intermediary worker is.
How Does a Reverse Proxy Work?
- Getting a client association demand
- Finishing a TCP three-way handshake, ending the underlying association
- Associating with the beginning worker and sending the first solicitation
What is the Difference Between Reverse Proxies and Forward Proxies
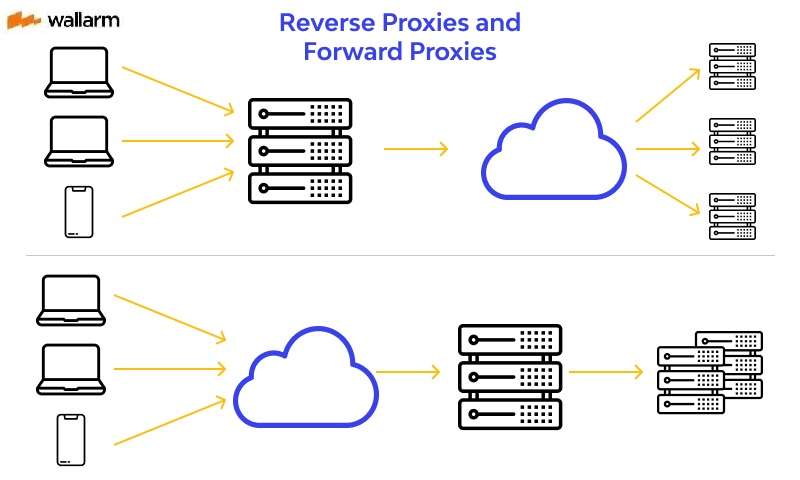
Reverse proxies are workers that sit before at least one web workers, capturing demands from customers. This is unique in relation to a forward intermediary, where the intermediary sits before the customers. With a reverse proxy, when customers send solicitations to the beginning worker of a site, those solicitations are captured at the organization edge by the opposite intermediary worker. The reverse proxy worker will then, at that point send solicitations to and get reactions from the beginning worker.
The distinction between forward and reverse proxies is inconspicuous however significant. An easy approach to summarize it is say that forward proxies sit before a customer and guarantee that no beginning worker at any point discusses straightforwardly with that particular customer. Then again, a reverse proxy sits before a beginning worker and guarantees that no customer at any point discusses straightforwardly with that beginning worker.
Indeed, how about we show by naming the PCs in question:
D: Any number of clients' home PCs
E: This is a reverse proxy worker
F: at least one beginning workers
Switch Proxy Flow
Ordinarily all solicitations from D would go straightforwardly to F, and F would send reactions straightforwardly to D. With a reverse proxy, all solicitations from D will go straightforwardly to E, and E will send its solicitations to and get reactions from F. E will then, at that point pass along the fitting reactions to D.
Benefits of a reverse proxy
- Burden adjusting
A famous site that gets a great many clients consistently will be unable to deal with the entirety of its approaching site traffic with a solitary beginning worker. All things being equal, the site can be dispersed among a pool of various workers, all taking care of solicitations for a similar site. For this situation, a reverse proxy can give a heap adjusting arrangement which will circulate the approaching traffic equitably among the various workers to keep any single worker from getting over-burden. If a worker flops totally, different workers can venture up to deal with the traffic.
- Insurance from assaults
With a reverse proxy set up, a site or administration never needs to uncover the IP address of their starting point server(s). This makes it a lot harder for aggressors to use a designated assault against them, for example, a DDoS assault. Rather the assailants may have the option to focus on the reverse proxy.
- Worldwide Server Load Balancing (GSLB)
In this type of burden adjusting, a site can be dispersed on a few workers all throughout the planet and the reverse proxy will send customers to the worker that is geologically nearest to them. This reductions the distances that solicitations and reactions need to travel, limiting burden times.
- Storing
A reverse proxy can likewise reserve content, bringing about quicker execution. For instance, if a client in Paris visits an opposite proxied site with web workers in Los Angeles, the client may really associate with a nearby reverse proxy worker in Paris, which will then, at that point need to speak with a beginning worker in L.A. The intermediary worker would then be able to store (or briefly save) the reaction information. Ensuing Parisian clients who peruse the site will then, at that point get the privately stored adaptation from the Parisian reverse proxy worker, bringing about a lot quicker execution.
- SSL encryption
Encrypting and unscrambling SSL (or TLS) correspondences for every customer can be computationally costly for a beginning worker. A reverse proxy can be arranged to decode every approaching ask for and scramble every cordial reaction, opening up significant assets on the beginning worker.
Use Cases
Reverse proxies have varied operational capabilities. With a single tool, you can do tons of things in one go. If you adopted CASB deployment mode, it became the essence of SSE.
In addition, it plays a crucial role in the formation of ZTNA and SWG. So, you need to be clear about your expectations from reverse proxy and then move forward. We present you with some of its most preferred cases.
- Protect ill-managed devices
When work-from-home is the new normal, it’s common to see tons of ill-managed devices used for work purposes. Your employees will be using their personal devices to conduct a meeting or email a critical document. Such devices are at huge risk as they feature no robust security measures.
This unmanaged device issue has deeper penetration as it covers 3rd party endpoints and partner devices. Protecting these devices with the help of agents isn’t possible as no one will allow their personal devices or endpoints to be exposed to someone else.
Reverse proxies are of great help on this front. Your devices will be safeguarded against malware as well as data leakages well with their help.
- Reliable protection against the threats
The presence of a single infected file has the potential to corrupt the connected end-points, including devices & software. Unmanaged end-points are the highest risk in this scenario.
Reverse proxy has the potential to stop this malicious file spread by simply stopping the auto upload or download from impacted files or resources. As it hides the IP addresses, considerable protection against DDoS attacks is already offered.
- Seamless load balancing
When it comes to loading balancing, there is hardly anything that can beat the utility of reverse proxy. It will help you distribute the client requests to prevent server burnout. This can also be done by caching the original content from the server temporarily and sending it directly to the relevant client without involving the server in the procedure.
- Safeguarding the data
This proxy type is highly useful to stop data loss by stopping planned or unplanned uploads/downloads from cloud apps/devices. It can operate in line and keep an eye on the movement of encrypted traffic. Because of this feature, it’s easy to make sure that the file download/upload is as per your data protection rules.
How To Implement a Reverse Proxy?
Its implementation depends on what kind of jobs you want to get done with it. You need to first decide what you expect out of it. Do you want it for load balancing or to prevent cyber attacks? Decide on this first and then move forward.
Next, you should make sure that the reverse proxy and your owned website should be functioning in the same type of environment(s).
Contact your service provider and be specific with your goals, as HTTP reverse proxies are useful for tons of things. Forward your requirements crisply and clearly.
Ensure that its setup adheres to what you need and what your goals are. To do so, focus on the deployment and design rules specifically. Comprehending these rules right will help you pick the optimal proxy variant.
Subscribe for the latest news

















