What is the MITRE ATT&CK Framework? 14 Tactics
The MITRE ATT&CK framework has become the "lingua franca" of modern cybersecurity. As cyber threats evolve with a 30% increase in global cyberattacks in 2024 (Source: Check Point Research) organizations are moving away from traditional reactive defense toward behavioral analysis. This guide explores how ATT&CK provides a roadmap for understanding adversary behavior.

What Is the Mitre Attack Framework? (An In-Depth Explainer)
It stands for the MITRE Adversarial Tactics, Techniques, and Common Knowledge document. Cyberattack conduct can be modelled with the use of the matrices available in this framework, which is a curated source. The framework meaning is typically displayed as a table, with columns denoting the tactics employed at various points in an attack's lifespan and rows denoting the procedures employed to accomplish those diplomacies. It keeps track of how often certain approaches are used and any other metadata that is related with them.
Its architecture was developed as a result of an experiment that played the role of both the attacker and the defender in order to better comprehend attack dynamics and augment post-compromise finding through telemetry sensing and behavioral analytics. This framework was developed to help professionals better understand the state of the industry's ability to recognize known forms of hostile activity.
In 2026, the framework is the industry standard for mapping defense coverage, with over 80% of enterprises utilizing it to inform their security operations (Source: Enterprise Strategy Group).
History of the ATT&CK Framework: From Research to Industry Standard
Created by the MITRE Corporation in 2013, the framework was originally an internal project designed to document how attackers moved laterally within network environments after a breach.
- 2013–2015: Transitioned from a research experiment to a public portal.
- 2017–2023: Expanded from Windows-only to include macOS, Linux, Cloud, and Mobile.
- 2024–2026: Current iterations (v15+) now include advanced sub-techniques for AI-driven threats and more granular detection guidance for Cloud-native environments.
Who is MITRE and Why is the ATT&CK Framework Essential?
MITRE is a non-profit organization that operates federally funded research and development centers (FFRDCs) in the U.S. It serves as a neutral party between government and private sectors.
The framework is essential because it provides a common language. Before ATT&CK, red teams and blue teams often used different terminology to describe the same event. Today, saying "T1190" (Exploit Public-Facing Application) instantly conveys the exact nature of the threat to any security professional worldwide.
Who Uses MITRE ATT&K And Why?
Several IT and privacy experts, from "red teamers" who assume the role of an attacker or competitor to "threat hunters" and "security invention growth engineers" to "threat intelligence teams" and "risk management specialists," all make use of ATT&CK matrices in their work.
With the MITRE ATT&CK paradigm as a guide, red teams can better comprehend the attack surfaces and susceptibilities of a company's systems and devices and develop better post-attack mitigation strategies. How the attackers got in, where they go while within the network, and how they avoid detection are all important details. With the help of this set of tools, businesses may better understand their security situation, locate and evaluate weak spots in their defenses, and rank the threats posed by those spots in order of severity.
Its style helps menace hunters comprehend the visibility of attacks targeted against their defenses, both at endpoints and around the network perimeter, and discover connections between the precise approaches attackers are utilizing against their systems.
Throughout the cyberattack lifecycle, it is used by developers and engineers of security platforms to assess the efficacy of their solutions, discover previously unknown holes, and simulate the behavior of their systems under assault.
The framework is utilized by a broad spectrum of security professionals:
- Red Teams: To simulate real-world attacks and test defense resilience.
- Blue Teams (SOC): To identify gaps in detection and prioritize alerts.
- Threat Intelligence Analysts: To categorize and track specific threat actor groups (e.g., APT29, Lazarus).
- CISOs: To justify security investments based on mapped coverage of the most likely attack vectors.
Understanding the 4 Basic ATT&CK Matrices (Enterprise, Mobile, Cloud, ICS)
To keep the data manageable, MITRE organizes behaviors into specific matrices:
- Enterprise: The largest matrix, covering traditional networks and OSs (Windows, macOS, Linux).
- Mobile: Specific to Android and iOS, focusing on app-based threats and network spoofing.
- Cloud: Covers platforms like AWS, Azure, GCP, and SaaS applications (e.g., Office 365).
- ICS (Industrial Control Systems): Critical for infrastructure, covering specialized protocols used in power plants and manufacturing.
MITRE Tactics And Techniques
An MITRE ATT&CK evaluation's strategies provide an explanation of the evaluation's reasoning or its component sections. The aggressor's planned goal or the purpose for taking action is a stand-in for their offensive strategies. For instance, a foe might be interested in obtaining valid identification documents. These are some examples
These are some examples
Cyber Attack Tactics Overview
| Tactics name | The adversary is trying to… |
|---|---|
| Reconnaissance | Collect data for use in making future plans. |
| Resource Progression | Establish resources to aid operations. |
| Preliminary Access | Get into your grid. |
| Execution | Carry out an attack by executing harmful code. |
| Persistence | Uphold their foothold. |
| Privilege Escalation | Acquire higher-level permissions. |
| Defense Elusion | Avoid being detected. |
| Credential Access | Steal account credentials. |
| Discovery | Figure out your environment. |
| Lateral Measure | Move through your environment. |
| Collection | Gather stats of interest to their goal. |
| Regulation and Direction | Communicate with compromised networks to control them. |
| Exfiltration | Gain unauthorized access. |
| Impact | Manipulate, interpose, or abolish your systems and statistics. |
Its techniques can be broken into groupings and each of it signifies a distinct set of threat modeling or steps that a hacker takes to achieve his goals.
Malware or threat actor organizations have been caught attempting to breach company networks using each of the MITRE ATT&CK techniques. As a kind of playbook or "how to," techniques give defenders a head starts on countering an oncoming onslaught. To what methods are hackers resorting to in order to breach your system? How are they able to stay under the radar? Is there any way you could characterise their journey across your subnet?
In addition, there exist sub-approaches, which are even more nuanced methods. While techniques denote overarching strategies employed by an enemy, sub-methods describe finer nuances of such strategies. For instance, the Phishing technique is broken down into three sub-techniques that explain in greater depth how cybercriminals use phishing emails to compromise computer networks.
The library of techniques in the ATT&CK Framework is ever-expanding and now includes over 150 techniques and 270 sub-techniques organized into the aforementioned 14 strategies.
What are the Procedures of the MITRE ATT&CK Framework?
Procedures are the actual "in-the-wild" implementations of techniques. While a Technique is a general description (e.g., "PowerShell"), a Procedure is the specific script or command used by a known threat actor like APT28. This level of detail allows defenders to simulate exact attack patterns.
The Goal of MITRE ATT&CK: Benefits and Real-World Challenges
Benefits:
- Common Language: Bridges the gap between technical teams and management.
- Gap Analysis: Highlights exactly where your SOC is "blind."
- Interoperability: Most modern EDR, SIEM, and WAAP tools (like Wallarm) now map detections directly to ATT&CK IDs.
Challenges:
- Data Overload: With hundreds of techniques, it can be overwhelming for small teams.
- Maintenance: Adversaries change tactics constantly, requiring continuous updates to your mapping.
- False Sense of Security: Mapping a technique doesn't mean you are 100% protected against all its variations.
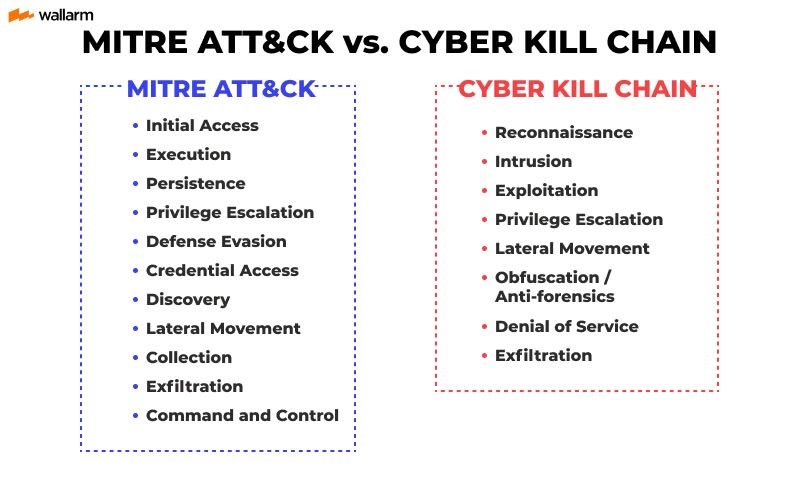
MITRE ATT&CK vs. Lockheed Martin Cyber Kill Chain: Key Differences
Another well-known methodology for analyzing the actions of a cyber-attacking opponent is Lockheed Martin's Cyber Kill Chain. In order, the following components make up the Kill Chain model:
- Reconnaissance - Collects data about conferences, email addresses, etc.
- Weaponization - Combines exploit and backdoor to create a deliverable payload.
- Distribution - Sends the infected person a bundled attack by electronic means (email, online, USB, etc.).
- Exploitation - The use of a vulnerability to execute code on a victim's machine.
- Malware installation: Sets up malicious software on the asset.
- Command and Control (C2) - A command channel for remote manipulation is included.
- Deeds on Intentions: Hackers who gain access using "Hands on Keyboards" complete their original objectives.

MITRE ATT&CK and Cyber Kill Chain diverge primarily in two ways:
- To begin, its framework provides a great deal of specificity on the execution of each stage via ATT&CK procedures and sub-techniques. So that defenders can stay up with the latest approaches, it receives regular updates based on input from the industry.
- Second, as we've seen, a cloud-native attack uses strategies and tactics that aren't taken into account by the Cyber Kill Chain. The Cyber Death Chain design is based on the idea that a threat actor will send malware or other payloads to the target environment, but this is much less of a concern in the cloud.
Use Cases
It can be utilized in a variety of settings. These are the most common applications.
- Adversary Emulation - ATT&CK can be utilized to generate adversary emulation scenarios for testing and validating defenses against popular adversary tactics.
- Red Teaming - ATT&CK can be employed to develop red team plans and organize operations in order to evade certain defensive measures that may be in place within a network.
- The Behavioral Analytics Development - ATT&CK framework can be used to build and evaluate behavioral analytics for spotting malicious activity in a given setting.
- Defense Gap Assessment - ATT&CK is a standard behavior-focused adversary model that may be used to examine tools, monitoring, and mitigations of existing defenses within an organization's enterprise.
- SOC Maturity Assessment - ATT&CK is one metric that can be used to gauge a SOC's effectiveness at detecting, analyzing, and responding to intrusions.
- Cyber Threat Intelligence Enrichment - ATT&CK is helpful for gaining insight into, and establishing assessments of, enemy groups from a behavioral approach that is instrument agnostic.
How to Use the MITRE ATT&CK Matrix for Better Defense
- Map your existing alerts to ATT&CK IDs.
- Identify the most likely threats for your industry (e.g., FinTech vs. Healthcare).
- Run "Atomic" tests to see if your logs actually capture those behaviors.
- Visualize coverage using the ATT&CK Navigator.
MITRE ATT&CK Framework Tools and Community Resources
- MITRE ATT&CK Navigator: An interactive web tool for visualizing and customizing your matrix.
- CALDERA: An automated adversary emulation system.
- Atomic Red Team: A library of simple tests that every security team can execute to test their defenses.
- Wallarm WAAP: Provides automated mapping of web and API attacks to MITRE ATT&CK tactics, such as Injection and Broken Access Control.
Conclusion: The Future of AI and MITRE ATT&CK Strategy
As we look toward the remainder of 2026, AI-driven attacks are the new frontier. Projections suggest that AI-enhanced malware will grow by 40% this year (Source: Cybersecurity Ventures). The MITRE ATT&CK framework is evolving to include these AI-specific tactics, ensuring that defenders have a roadmap for the next generation of threats.
How Wallarm Helps You Master the MITRE ATT&CK Framework
For modern digital enterprises, protecting APIs and web applications is a critical component of MITRE ATT&CK coverage. The Wallarm platform empowers security teams to bridge the gap between framework theory and practical defense by providing automated detection and response aligned with adversary behaviors.
1. Automated Mapping of Web & API Attacks to TTPs
Wallarm automatically classifies every incident according to MITRE ATT&CK tactics and techniques. Instead of seeing a generic "SQL Injection" alert, your SOC analysts see a direct link to T1190 (Exploit Public-Facing Application). This immediate context allows teams to understand where an attack fits within the broader adversary lifecycle.
2. Visibility into the Reconnaissance Phase (TA0043)
Most successful breaches begin with silent discovery. Wallarm’s API Discovery module identifies "Shadow" and "Orphan" APIs that attackers target during the Reconnaissance stage. By mapping your entire attack surface, Wallarm denies adversaries the hidden entry points they rely on to gain a foothold.
3. Neutralizing Credential Access (TA0006)
A primary goal for many attackers is gaining legitimate access. Wallarm effectively blocks sophisticated Brute Force and Credential Stuffing attacks (T1110), ensuring that attempts to bypass authentication are stopped before they can transition to the Persistence or Lateral Movement stages.
4. Real-Time Mitigation of Execution Techniques (TA0002)
While many security tools focus only on detection, Wallarm operates inline, blocking code execution and injection attempts in real-time. This directly neutralizes techniques such as T1059 (Command and Scripting Interpreter) and prevents attackers from gaining control over your application environment.
5. Shift-Left Security Testing
Wallarm allows you to automate security testing within your CI/CD pipelines. By identifying misconfigurations and vulnerabilities before they reach production, you proactively close the "holes" that attackers seek during their initial access attempts.
Key Stat for 2026: According to the Wallarm 2025 API Threat Report, API-specific vulnerabilities have increased by 20% year-over-year. Organizations using Wallarm reduce their Mean Time to Detection (MTTD) for these threats by 60% through automated MITRE ATT&CK mapping.
References
- MITRE ATT&CK® Official Site: https://attack.mitre.org/
- Check Point 2024 Cyber Attack Trends: https://www.checkpoint.com/resources/cyber-attack-trends/
- ESG Research - The Role of MITRE ATT&CK in SOC: https://www.esg-global.com/
- Cybersecurity Ventures - 2025 AI Threat Forecast: https://cybersecurityventures.com/
- MITRE ATT&CK v15 Release Notes: https://attack.mitre.org/resources/updates/
Subscribe for the latest news

















