SASE - Secure Access Service Edge
The system relies on your company's productivity network, affecting everything from opening files to the permissions provided. Due to this, your business needs to have a well-thought-out strategy for your network's structure and privacy. Given the dozens of available grid protection products, it might be challenging to determine whether your web infrastructure is productive. Gartner, a market leader in IT research and advisory services, forecasts that 40 percent of businesses will use SASE to address this problem by 2024.

What is SASE?
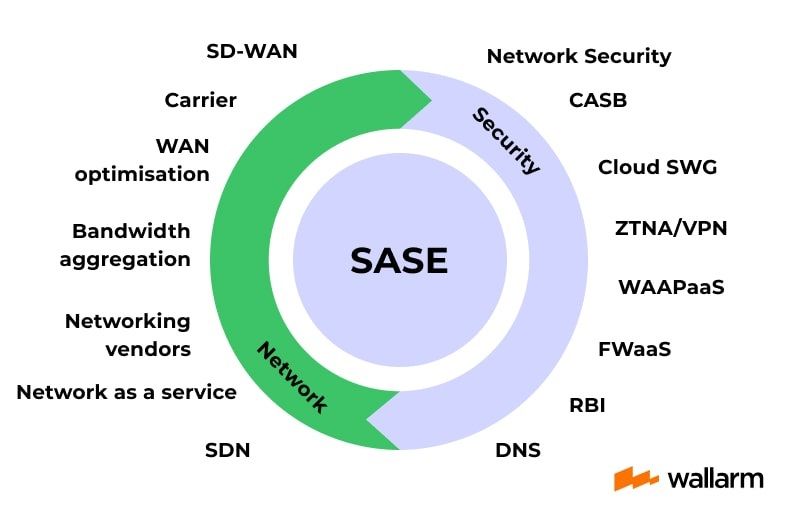
One style of cloud structure, known by the SASE definition, provides a single cloud service that performs web and security-as-a-service functionalities. The basic idea behind SASE is that it improves upon prevailing networking and safety setup. It paves the way for remote and mobile workers to make use of a variety of privacy features, for instance, a firewall as a service (FWaaS), a secure web gateway (SWG), zero-trust network access (ZTNA), and plenty of others. Separated into two categories, SSE and SD-WAN make up SASE.
Gartner's research from August 2019 first introduced the acronym SASE (pronounced "sassy"). Gartner states in the market trend analysis, "Customer aspirations for convenience, versatility, mobility, low bandwidth, and ubiquitous privacy are driving the intersection of the WAN and computer protection segments."
How Does A SASE Framework Function?
Within SASE, system gridlock and privacy priorities are paired with an ever-present danger, data protection, and lightning-fast, direct network-to-cloud transmission. Previously, businesses had to choose between pace and manage when using it; now, thanks to technological advancements, they can enjoy both.
Enterprise safety specialists can use individuality and context in the SASE structure to set the bar high for every web session regarding usefulness, stability, privacy, and economics. Institutions that use this structure can get faster and expand in the cloud's scalability while addressing the new privacy encounters that come with cloud environments.
.jpg)
Main Components of The SASE Model
To better comprehend the skills and tools, we can divide it into six main parts:
It is an overlay design that chooses the most efficient path for data to go to and from the cloud, the internet, and other data centers. It improves efficiency and customer satisfaction. It facilitates the swift rollout of new software and facilities and the unified supervision of strategies for a widespread net of endpoints.
- Centralized And Unified Management
Administering all of those mentioned above from a single interface allows you to alleviate many of the issues associated with change access, software updates, scheduling interruption windows, and policy administration while delivering consistent policies across your organization, irrespective of where users interact.
- Secure Web Gateway (SWG)
Using SWGs, you can block spam and other undesirable content from accessing your private network via the internet. It safeguards your company's network by blocking access to potentially dangerous websites and traffic, internet-borne viruses, malware, and other cyber threats and preventing them from becoming infected with these hazards.
- Firewall as a Service
Cloud-based firewall services, such as those provided by FWaaS, can be used in place of physical firewall equipment to provide enhanced Layer 7/next-generation firewall (NGFW) features like URL filtering (or Web filtering), APT detection, intrusion prevention systems (IPS), and DNS encryption.
The usage of a cloud access security broker (CASB) protects businesses from vulnerabilities like data loss, malware infections, failure to comply with regulations, and a lack of oversight. They safeguard cloud applications whether they are housed in an infrastructure as a service (IaaS) cloud, a private cloud, or a SaaS model.
- Zero Trust Network Access
ZTNA's software and services provide safe, reliable, and convenient access to corporate software from anywhere in the world. A zero-trust paradigm does not presume trust and instead grants the least privileged access possible according to specific policies. This way, you won't have to worry about the security of your internal network or the privacy of your apps while connecting remote workers to the Internet.
SASE Vs. Traditional Network Security
Table
| SASE | Traditional Network Security | |
|---|---|---|
| Routine On-Site Access | Is an alternative to VPN. SASE users connect to on-premises and cloud components. The SASE administrative interface is used to create and implement the policy. | Most conventional designs rely heavily on virtual private network (VPN) technology via SSL/TLS andbrowser access or a specialized endpoint client. |
| Cloud Computing Access | Facilitates network access to SaaS, PaaS, and laaS that is efficient, simplified, and cloud-aware. API integration and request introspection handle end-user queries. | On-premises cloud access uses typical firewalls, proxies, and routing controls. |
| Network Access Governance | Combine system safety and access measures, particularly firewalls, into one architecture. | Switching, routing, firewalls, and proxies are typically used in on-premises environments to regulate user access. |
| Sd-Wan, Wan Efficiency, Bandwidth Consolidation | Combines SD-WAN access and traffic optimization into a single brokering service. | Controls and features like these are often not well integrated and require support from multiple manufacturers and products. |
| Web Application Surveillance | Despite possible immaturity in policies and capabilities, the platforms now incorporate WAF services and policies into the same brokering strategy. | WAFs are independent appliances or platforms or brokering to a CDN or in-cloud service. |
| Identifying Dangers in Networks | You can detect and eliminate potential threats in your network with a single set of services. | Next-generation firewalls (NGFWs), malware detection sandboxes (MDS), and CASB brokering are all methods used to identify threats in a network |
Top SASE Benefits
When compared to conventional, on-premises network choices, SASE platforms have many advantages. Some of the most compelling arguments in favor of SASE network adoption by businesses include the following:
- IT cost and complexity reduction
The legacy network security models that are currently in use rely on an assortment of various tools to secure the network perimeter. SASE cuts down on the number of solutions required to secure applications and services, which decreases the amount of money spent on IT and makes administration much more accessible.
- Enhanced responsiveness and manageability
As SASE is offered over the cloud, both the grid and the privacy framework are totally customizable. The system can expand your business, making accelerated digital transformation a realistic possibility.
- Made for hybrid work
SASE provides enterprise-level security for all users, regardless of how or where they work, in contrast to conventional hub-and-spoke networks, which struggle to manage the bandwidth required to keep remote employees versatile.
- Enhances UX
Regarding user safety, the SASE cloud is unparalleled since it provides seamless, real-time, intelligent management of security exchanges. It decreases the time it takes for users to connect to cloud applications and services and lowers the organization's vulnerability to attacks.
- Improved safety
SWG, DLP, ZTNA, and other threat intelligence technologies combine inside the SASE architecture to offer remote workers secure admittance to business properties while simultaneously lowering the danger of lateral movement within the network. Without a doubt, in SASE, every link is analyzed and protected, and precise guidelines for threat prevention are laid out from the very beginning.
Problems Related to SASE Implementation
Consequences are vague because SASE is used to characterize a developing technology with varying methods. The biggest potential drawback is that IT departments might not get all the advantages of multisource. For example, they might not be able to ensure different parts of their projects are sourced from the finest possible providers for individual functions or spread out the risk associated with working with multiple vendors. Due to the bundled nature of the networking and security services provided by SASE architecture, any problems on the provider's end might theoretically bring down the entire system for end users.
SSE vs. SASE
Secure Access Service Edge (SASE) strategies benefit from Security Service Edge (SSE) implementations because they provide essential security services for the network's edge, including the web, the cloud, and internal applications.
With SASE, networking and security are provided as a cloud service at the edge of the network rather than in the data center.
Using a comprehensive SASE platform that features cloud-delivered network security services, SSE teams who employ software-defined wide-area networking keep the path operational.
Why Do We Need SASE?
Increased flexibility and scalability, simplified operations, and strengthened protection are essential for a successful digital company transition. Modern organizations must ensure users get the most outstanding experience from anywhere.
Due to these changes, SASE is no longer a luxury but a requirement. Here are four justifications:
- SASE adapts with your organization as your network and security needs evolve. Cloud-delivered SASE helps your business, network, and security scale together.
- SASE facilitates work from anywhere. Hub-and-spoke designs can't handle the bandwidth needed to keep remote workers productive. SASE maintains enterprise-level security for all users and devices everywhere.
- SASE combats evolving cyber threats. Constantly vigilant security personnel guard against the most recent attacks. SASE provides greater protection and easy management, allowing them to handle advanced threats from anywhere.
- SASE enables IoT adoption: The Internet of things produces value for organizations worldwide, but you need a robust platform to develop an IoT ecosystem. With SASE, you can achieve your IoT objectives with unrivaled connection and privacy.
SASE Deployment Tips
When it comes to SASE, many companies only do it in bits and pieces. Even if they don't realize it, they may have already embraced some SASE features. Necessary steps businesses can take toward adopting the SASE paradigm include
- Protecting distant personnel.
- Implementing a cloud-based security system around the regional office.
- Distributing anti-DDoS defenses more widely.
- Bringing locally hosted software to the cloud.
- Implementing a centralized, cloud-native policy enforcement system in place of physical security appliances.
FAQ
Getting started with SASE is easy. Identify your organization's specific security and network needs, select a suitable SASE provider, and start deploying your customized services.
SASE is ideal for organizations that need to provide secure access to data and applications for their distributed workforce, in a scalable and cost-effective manner.
Unlike VPN, SASE provides a complete set of network services including security, authentication, and optimization, all delivered through a single cloud-managed service.
SASE provides comprehensive security features like firewall, VPN, anti-malware, and more, to secure your network from cyber threats regardless of your employees' locations.
SASE is a network architecture that combines security and networking functions into one unified service, delivered from the cloud.
Subscribe for the latest news

















