What is PGP encryption (Pretty Good Privacy) ?
Introduction
Protecting data is one of the many priorities that businesses have to look after during operations. The surged frequency of cybercrimes and data theft incidents have forced enterprises from every sphere not to become lenient when data protection is concerned.
In this post, we’ll introduce you to a super-advanced method called PGP encryption. Read ahead and know more.

What is PGP (Pretty Good Privacy) ?
As we all know, adding encryption to safeguard the in-transit data is anindustry’s standard today. The practice makes it inaccessible for hackers or any unauthorized personnel. But, as it has been here for too long and some skilled hackers have found ways to nullify it. Hence, the need for more advanced encryption arises.
PGP is the answer to this requirement. It makes use of cryptography as well as authentication - to be sure that the security is utterly strong after its deployment.
PGP file encryption aims at helping you with cryptographic encryption. During the initial deployment of the PGP open-source software applications, it helped end-users to communicate securely with a server of bulletin board devices. As the world started realizing its efficacy, it soon became a de facto encryption for e-mail exchanges and sensitive discussions through other channels.
Explanation of PGP Encryption
PGP is a vast topic to discuss as one needs to understand the function, its security deployments, PGP decrypt, and various other aspects. However, the basic yet substantial explanation of PGP is that:
- Single-use and user-specific keys are used
- Safest method to safeguard the files at present
- Cracking the 2048-bit RSA SSL certificate may take quadrillions of years
- PGP implementation requires the help of a PGP software.
How does PGP work?
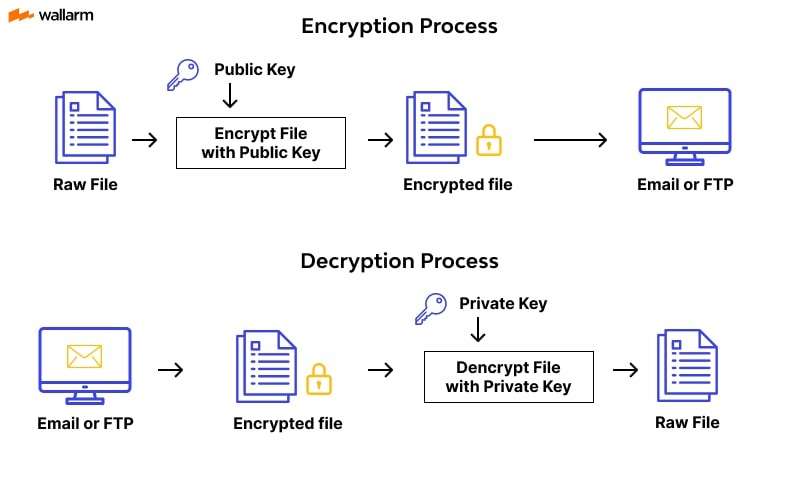
PGP is very similar to Kerberos and SSL encryption, which are useful for website and network user authentication. While one tends to comprehend the fundamentals of PGP encryption, it’s crucial to grasp the fact that utilizing the public and symmetric keys makes the essential part of this procedure.
Though PGP’s algorithm is a bit complex, let us try to see how it functions. Here are the major steps of its functionality in simple words.
- In the beginning, the function PGP creates an arbitrary key for the current session. For this, it uses public or symmetric - any one. On a structural level, session key may feature various numbers and is hard to predict. Just as OTP, it can be used once only.
- At the next step, encryption is added to the key associated with the current session. The procedure also uses anticipated receiver’s public key - the distinct feature of a person that is accessible by everyone.
- Next, the sender forwards the encrypted key (created at the previous step) to the predicted receiver. Here, PGP decryption helps receiver decode the message finally.
This is the basic overview of the modus-operandi of PGP encryption.
PGP Encryption in action
PGP security is easy to understand with the help of a real-time example. Here is why we present you with an overview of PGP encryption in action. We will make it happen by keeping ProtonMail in context.
A leading email service provider, ProtonMail is an advent user of PGP encryption. A simple sign-up process will help you encrypt the emails. It’s easy to check the activation of email PGP encryption in ProtonMail. If you can see a padlock icon on the email’s subject line, the email encryption is activated.
Using PGP encryption
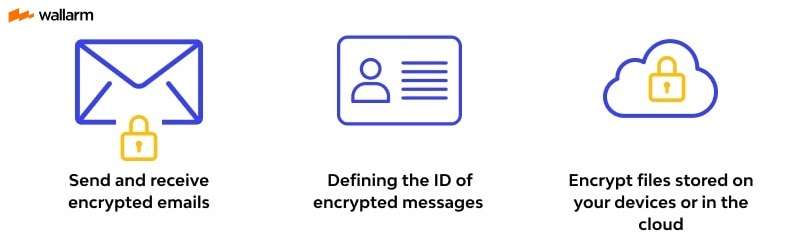
PGP encrypt method has earned a deeper penetration in the online data exchange or communication industry because of its ability to keep transmitting data secured by a public and private key. Based upon the requirement, it can be of great use in:
- Encrypting Files
Organizations that have to send or share files featuring data of high cruciality, vulnerability and sensitivity use the PGP key to encrypt the data included. The main algorithm in action is the RSA algorithm. Now, you must learn that the RSA algorithm is practically unbreakable. Hackers will have no luck in breaking it down. This is why it’s most commonly used in the development of threat detection software.
Its role in file encryption is to protect the data mentioned in the files, verify the user authentication beforehand, and remove the complexities.
- Digital Signature Verification
It is one of the many ways to protect email data and have robust email verification in place. It’s very common to receive emails from unknown recipients. But, entertaining them could prove fatal for anyone. With the help of digital signature (DS), it’s easy to check the identity of the unknown sender.
With the help of a digital signature, an algorithm can add a key to every piece of data that is supposed to be part of an email. This way, a hash function is created. Now, the hash function is a type of algorithm that is useful to transform the email-included messages into a standard data block.
This newly-constructed data block is backed with the power of the sender’s private key. A receiver will have accesssender’s public key that s/he can use to decrypt the received data block, mentioned in the email.
This process of email verification makes it easy to figure out whether any alterations have been made to the in-transit data. This is also useful to find out the authenticity of the sender or spot the presence of any bogus digital signature.
- Encrypting Emails
Email encryption is a wide usage of PGP. Primarily, users seeking exchange of sensitive information used it. With time, it became a mainstream solution for government organizations and agencies.
These entities are using this kind of encryption to protect sensitive information.
Advantages and disadvantages of PGP encryption
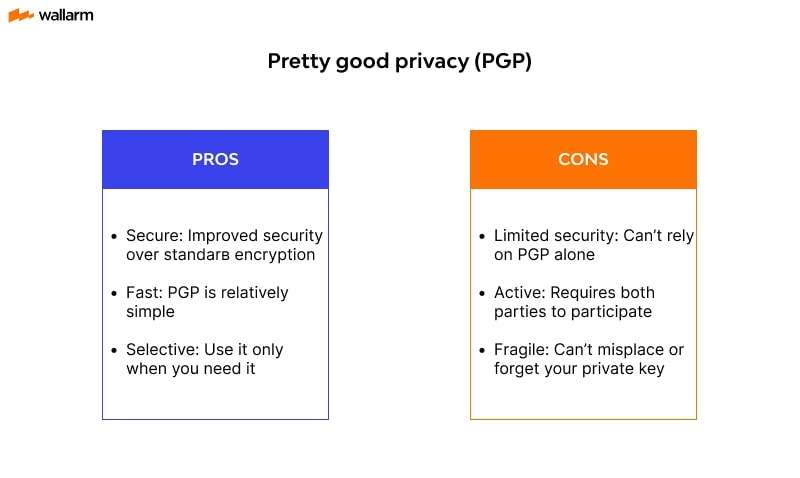
PGP’s implementation demands more than usual efforts from the users’ side as one has to figure out its implementation extent and the type of data they need to protect.
If due attention is paid, it manages to improve the system security and can help organizations to reduce the risks of cyber threats. However, this technology is not always beneficial.
In fact, just like anything else, it comes with its share of pros and cons. So, before you start using this technology, you need to weigh its advantages and disadvantages.
Let’s talk about the advantages first.
- Of course, we love this encryption for its unbreakable feature. If previous data is taken into consideration, there is hardly any incidence of cyber threat that has happened because of the breach of PGP encryption. This is why enterprises and individuals use it for securing sensitive information.
- It’s compatible with all the leading devices. Whether you use a Windows device or Linux system, it works perfectly fine. This makes it useful for everyone.
- It makes file encryption possible for everyone. There are many PGP software that are quick in action.
However, these benefits won’t make us ignore the flaws it has.
- It’s too complex. Implementation of private/public keys and authentication systems can be too demanding. It takes more than usual efforts to make it happen.
- As it involves public and private keys, its management is tedious. It’s very crucial to fully understand the use of cryptographic keys for both the public and private. End-users must understand how to use keys and manage them. If that’s not effective, it’s very obvious to misplace the keys, which are the building blocks of this encryption. This is too overwhelming for a few as it demands a high-level understanding of cryptography.
- Lack of anonymity is another major issue that people use PGP encryption. Even though the sensitive information is encrypted, anonymity isn’t maintained. This is why it’s easy to track the use of the PGP tool. Those who are seeking anonymity in their communication must use a VPN.
- PGP will be in action only when both the sender and receiver are using PGP software. Not only this, the version should be the same at both ends. This makes PGP limited or restricted as it’s not possible to fulfill this requirement.
PGP vs GnuPG vs OpenPGP
While discussing PGP, mention of OpenPGP and GnuPG is imperative as they both are linked with PGP. This is why one must have clarity over all these terms.
OpenPGP is one of the most used open-source encrypting and signing. It came into being in 1997 to allow users to develop customized solutions that can work closely with PGP and makes its implementation easy.
Before the invention of OpenPGP, PGP encryption usage was controlled and highly restricted. Only US Military and government agencies were able to use it. This restriction was the basis of OpenPGP development. The development of OpenPGP promoted easy cryptography export so that anyone can use it.
When one tries to learn about OpenPGP v/s PGP, it’s crucial to know that PGP is highly controlled, and OpenPGP is lenient.
Now, let’s talk about GnuPG or GPG.
This is a way to deploy OpenPGP and is preferred by those who found PGP too complex or tedious. It signifies GNU Privacy Guard and came into being in 1997.
What makes it useful that it makes use of OpenPGP is its ability to interchange the algorithms. For example, private & symmetric key encryptions can be interchanged or work together to provide better encryption to the end-user.
The fact to know about GPG vs PGP is that PGP is communication encryption, on the other hand, GnuPG is a way to utilize the lighter version of PGP.
Hope you have got the full understanding of the subject now. Still got queries? Ask us.
PGP Encryption Software:
PGP encryption software is universally available and can be integrated with various email clients to encrypt messages and attachments. Outlook can be used with the gpg4o plugin to enable Pretty Good Privacy encryption. Apple Mail can be secured with GPGTools, which provides an easy-to-use interface for encrypting emails using the PGP protocol.
Thunderbird users can install Enigmail, a plugin that adds PGP encryption and digital signature capabilities. ProtonMail is a secure email service that uses PGP encryption by default, providing end-to-end encryption for all messages. Android users can use FairEmail, which integrates with OpenKeychain to enable Pretty Good Privacy encryption.
Overall, tools offer a secure way to protect sensitive information and communications by using a complex encryption process that involves a public key and a private key. A diagram of Pretty Good Privacy encryption can help to understand the encryption process and how the keys are used to protect information.
- Thunderbird with Enigmail
Pros: Integrates with Thunderbird email client, easy to use, open-source software, free to download and use.
Cons: May require some technical knowledge to set up, not as user-friendly as some other options, may not work with all versions of Thunderbird.
- Android with FairEmail:
Pros: Open-source software, integrates with OpenKeychain to enable PGP encryption, user-friendly interface, free to download and use.
Cons: May not work with all Android devices, limited functionality compared to other email clients, requires installation of OpenKeychain.
- Outlook with gpg4o:
Pros: Integrates with Outlook for easy-to-use PGP encryption, compatible with Microsoft Office Suite, allows for creating and managing PGP keys.
Cons: Requires purchasing a license, can be difficult to set up for non-technical users, may not work with all Outlook versions.
- Apple Mail with GPGTools:
Pros: Provides an easy-to-use interface for encrypting emails using the PGP protocol, integrates with Apple Mail, includes key management tools.
Cons: Only available for Mac OS, may not work with all versions of Apple Mail, requires downloading and installing software.
- ProtonMail:
Pros: Offers end-to-end encryption by default, user-friendly interface, no installation required, available as a web-based service or mobile app.
Cons: Only supports email communication with other ProtonMail users, limited storage capacity for free accounts, paid plans can be expensive.
Overall, each tool offers its own advantages and disadvantages when it comes to PGP encryption. The best option will depend on individual needs and preferences, such as ease of use, compatibility with devices and email clients, and desired level of security.
FAQ
PGP (Pretty Good Privacy) encryption is a method used to protect sensitive information by scrambling it into an unreadable format. It uses a combination of public and private keys to encrypt and decrypt messages and files.
Yes, PGP encryption is considered one of the most secure methods of encryption available. It has been used for decades and is trusted by businesses, governments, and individuals worldwide.
To use PGP encryption, you'll need to first obtain a PGP keypair consisting of both a public and private key. There are several software options available, such as GnuPG and Kleopatra, which can generate and manage PGP keys.
While PGP encryption in itself is very difficult to hack, there are methods that attackers can use to bypass it. For example, if someone obtains your private key, they would be able to decrypt any messages sent to you encrypted with your public key.
According to the Electronic Frontier Foundation, recent advancements in PGP encryption include the integration of PGP into popular email clients such as Outlook and Thunderbird, as well as the development of new protocols like Autocrypt, which aims to make end-to-end encryption more user-friendly.
References
Subscribe for the latest news

















