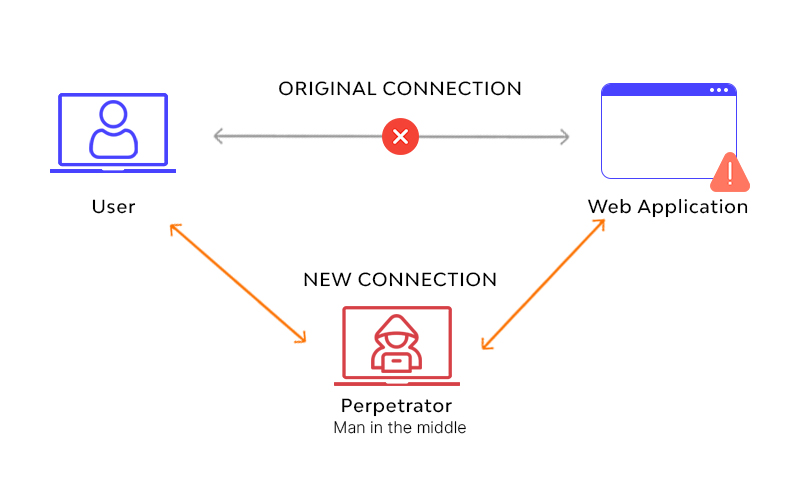
What is MITM - Man in the Middle Attack
MITM Defenition:
A man-in-the-middle (MITM) represents a sort of cyberattack where an intruder covertly taps transmissions connecting two entities to monitor or alter traffic therebetween. Malicious ones may utilize MITM attacks to seize passwords or other sensitive data, snoop on the prey, disrupt connections, or distort content.

MITM Step 1: Inserting a secret listener into communication
Typical means attacker use include:
- Rogue Wi-Fi Access Point
Attackers set up a wireless access point, disguised as a nearby legit Wi-Fi network, and cheat devices to join its domain instead of connecting with the authentic Wi-Fi point. An attacker needs just close enough physical proximity to the original network to get things done.
- Rogue DHCP host
This attack needs physical access to the network. A perpetrator raises a bogus DHCP server and waits for clients to connect or force them to reconnect by sending DHCP RELEASE packets. Furthermore, an attacker may engage a Denial of Service attack on an authentic DHCP host.
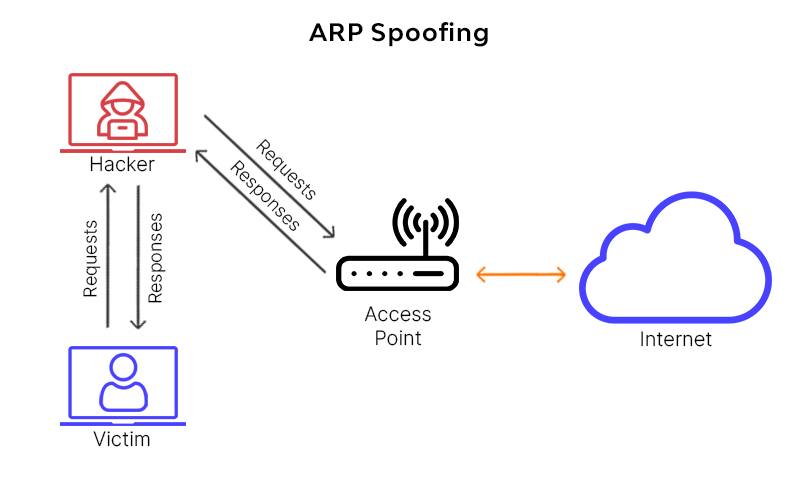
- ARP Spoofing
ARP (Address Resolution Protocol) is utilized to resolve IP addresses to physical MAC (media access control) addresses in a local area network. It asks the ARP cache to resolve the IP to a MAC address. When the IP is not known, a request to the network is made asking for the MAC address for the set IP address. A malicious one could respond to these requests with its own MAC address, set up the connection, get a hand on the data sent, and then redirect it to the real addressee.
- DNS Spoofing
The same way ARP resolves IP addresses to MAC addresses on a LAN, DNS resolves domain names to IP addresses. In a DNS spoofing attack, the attacker tries to inject the wrong DNS cache information into a host. It results in the victim sending sensitive data to a malicious host, considering they send data to a trusted website.
- mDNS Spoofing
Multicast DNS is the same as DNS but works in a local area network (LAN) using broadcast comparable to ARP. The local name resolution system makes the configuration of network devices simple. Smart devices such as printers, TVs, and others use this protocol since they are typically on a trusted network. When an application wants to know a particular device's address, an attacker can respond to that request with bogus data, directing it to the address under control. Since devices maintain a local cache of addresses, the victim will now see the attacker's machine as trusted for a set period.
MITM Step 2: Tinkering with your data
When successfully interposed into the communication between parties, an attacker can analyze and manipulate all the data sent. Typical ways of using this opportunity are:
- Sniffing
Attackers can utilize packet capturing instruments to scrutinize packets at a low level. Using special wireless devices that can be put into monitoring or promiscuous mode can allow seeing packets addressed to other hosts. Invaluable data can be obtained from the traffic, such as session tokens, transaction information, and every kind of sensitive data party is supposed to be exchanging.
- Packet Injection
An attacker can use a monitoring mode to inject malicious packets into information streams. The packets can mix malicious payloads with original data, looking to be a legit part of the communication. Packet injection generally requires first sniffing to discover the right ways and timings to compose and transmit packets.
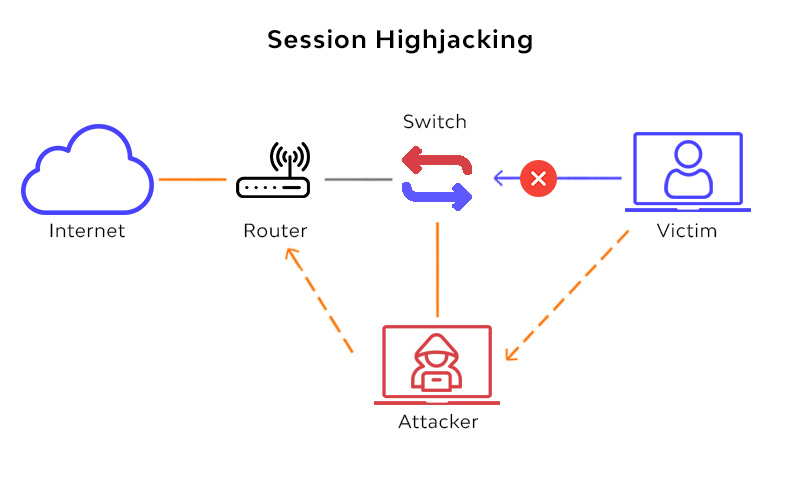
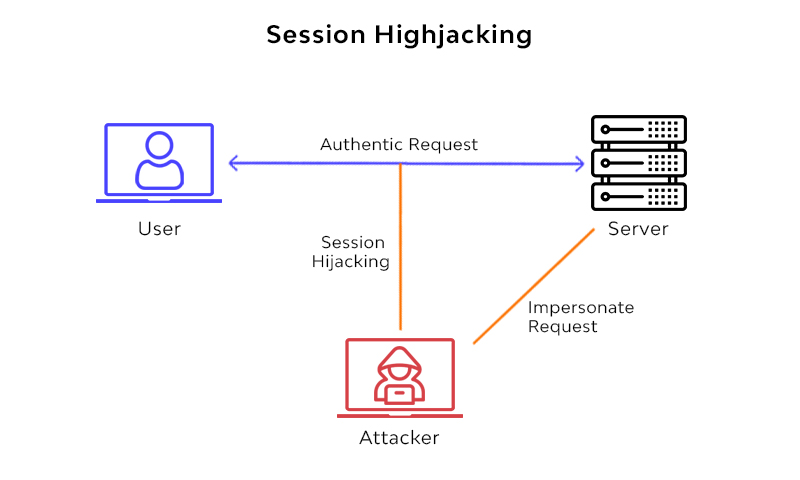
- Session Hijacking
Most web applications employ a login mechanism generating a temporary session token for future requests. It helps to release the user from typing a password on every page. After sniffing sensitive traffic and seizing the session token, the attacker makes requests under the victim's identity.
In some cases, to perpetrate a successful attack, the con needs to get along with tokens to get all the information used for “fingerprinting” (victims software and hardware characteristics, country and time zone, etc.)
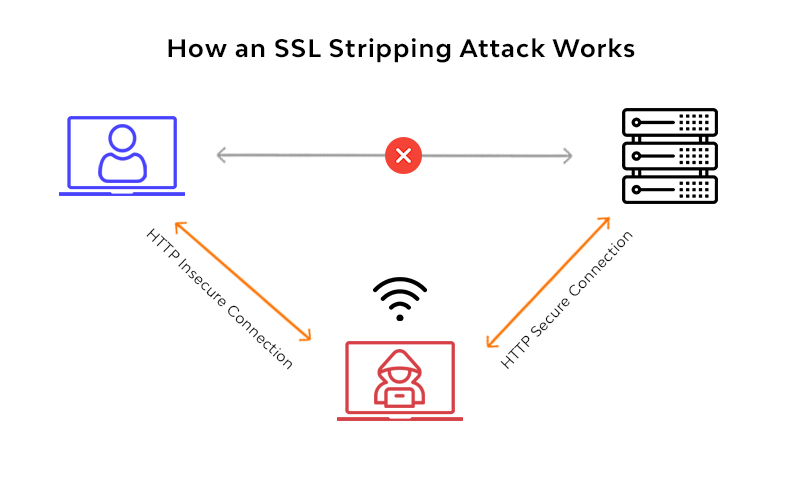
- SSL Stripping
HTTPS is a primary safeguard against ARP or DNS spoofing. To avoid it, attackers use the SSL stripping technique to catch packets and change their HTTPS-based address requests to their HTTP equivalent. It drives the hosts to make unencrypted requests to the effect that information can be gotten in plain text.
How can Session Hijacking Happen Besides through MITM?
Except for abusing the victim’s identity data through a Man in the Middle attack, cybercriminals can also use a different kind of session-hijacking trick, for example:
- Evil Twin, where the cybercriminal creates a mirror Wi-Fi network that appears to be the original one. Making the victim connect to it, the threat-actor can intercept the network data and misuse it.
- Sniffing, where the threat-actor ‘sniffs’ the information by intruding into a communication channel and seeing what is being sent to or from a device.
- Side-jacking, where the attacker uses sniffing to replicate the session cookies for themselves and fetch unencrypted login data, if it is there.
MITM Examples
While the underlying philosophy of the attack remains the same, MitM can happen in multiple ways. For example:
- A threat-actor can inject a packet-sniffer at an unsecured endpoint in a network, and as soon as a user tries to login to a website, he is sent to a fake site instead. This fake webpage collects the user’s crucial data and enables the threat-actor to utilize it on the real website to perform data or financial fraud.
- A cybercriminal first interacts with the target user and acts as an authority (e.g., a bank official) to gain access to crucial details. Thereafter, it visits the authority site (e.g., a bank website) and acts as the victim to get a loan or start a transaction.
Real-world Incidents
The above-specified scenarios are not just theory. In the history of cybersecurity, there are various MiTM attacks documents. A few are:
DigiNotar Breach (2011) was driven by MiTM and resulted in the organization's bankruptcy. The attacker successfully fetched around 500 certificates for top service providers (including Google, Yahoo, Mozilla, Skype, and so on) to mimic a legit site. Later, he used these certificates to trick Gmail users in Iran that led to serious troubles.
A visual search engine named Superfish was pre-configured in Lenovo systems before 2015. The software had adware scanning the SSL traffic passing through those systems and installing fake certs on these devices. MiTM attackers did eavesdropping through this adware and ran ads as per their wish – even on the pages that were encrypted. The scandal made Lenovo lose $8.3M in the lawsuit.
Equifax’s MiTM-driven Data Breach (2017) made the company take its Android and iPhone apps off the respective app stores. The reason was - organization did not use HTTPS connection consistently and allowed threat-actors to intercept the traffic, resulting in the exposure of personal data of more than 160 Million users from the US, UK and Canada.
How to detect a man-in-the-middle attack
Detecting Man-in-the-middle attacks can be challenging without taking proper actions. If you aren't proactively hunting your communications interception, a Man-in-the-middle attack can potentially run unrecognized until it's too late. Testing for appropriate page authentication and executing some tamper detection methods are essential for identifying a potential attack. Still, these procedures might require extra forensic post-analysis.
It's essential to apply measures to prevent MITM attacks before they occur rather than detecting them while actively happening. Being aware of your browsing habits and understanding possibly dangerous areas can be essential to supporting a secure network.
Here, we have covered some of the most rewarding approaches to prevent MITM attacks from compromising the information you transmit.
Best practices to prevent man-in-the-middle attacks
Keep strong WEP/WAP Encryption on Access Points
Having a robust encryption mechanism on wireless access points restricts unwanted users from joining your network just by being nearby. A weak encryption mechanism can let an attacker brute-force his way into a network and begin man-in-the-middle attacking. The more robust the encryption implementation, the more protected it is.
Use Stronger Router Login Credentials
It's essential to renew your router login regularly (not just your Wi-Fi password but also your router login credentials), and having default credentials left set is the open gate for attackers. If attackers discover your router login credentials, they can change your DNS servers to their malicious servers or infect your router with malware.
Restrict access to the local area network
Discovering and restricting unknown devices from connecting to your local network can guard them against malicious intruders.

Prevent man-in-the-middle attacks
- Use Virtual Private Network
VPN can be used to build a protected environment for sensitive data in a local area network. It uses key-based encryption to create a subnet for secure communication so that even if an attacker manages to get on a shared network, they won't be able to decipher the traffic.
- Force HTTPS
It is essential to use HTTPS to communicate over the net. It limits attackers in using the sniffed data. Websites should only use HTTPS and not provide HTTP alternatives (HSTS is a must).
- Use Public Key Pair Based Authentication
Public key pair-based authentication like RSA can be used in various layers of the stack to ensure the ones you communicate with are the ones you want to.
FAQ
References
Subscribe for the latest news