What is Magecart Attack? ⚔️ How to prevent it?
Introduction
Hackers are getting more and more creative, they tend to always find a way to benefit and usually it is something really unique in the first place. When we are talking about “black-hat” activities, we usually think about ransomware attacks, massive service exploitation or phishing campaigns, this time the attack is something different, it is called skimming.
Skimming is interesting, its idea is to compromise a third party vendor (physical or digital), thus, extracting data about the client's credit or debit cards.
One technique for skimming involves stealing a large card reader from a legal terminal using pincers or a movable wrench. The gadget can also be put nearby on the ground or within a cash machine's mouth. Typically, they are found immediately linked to the ATM faceplate where other devices have previously been attached, but without any visible wire in it (such as glue). Another typical location might be above or below the keypad below, where there is no camera present. In order for a thief to copy the PIN and card being inserted later on with a covert camera or scanner, surveillance cameras can also be used at ATMs to record both of these events.

Magecart malware - What is it and How it Works?
If we were to learn a little bit about the history of hacking, we would quickly discover that hackers prefer to give their organizations creative names. Magecart is an organization of hackers, as you would have imagined. They frequently only focus on online shopping cart systems, one of which is the Magento platform, which offers checkout and shopping cart capabilities for store websites. Magento served as these groups' initial objective, and it serves as the inspiration for the name of the organization.
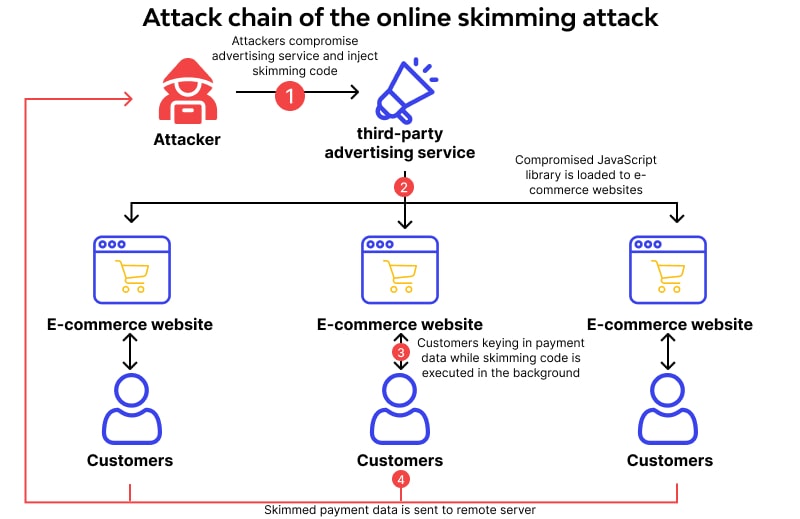
Due to the fact that online shopping carts save client payment information, they make desirable targets. If a malware can access this data context, you have a ready-made card collection tool. The code utilized with these third-party components isn't properly vetted on almost all e-commerce sites that use shopping carts, which is a formula for a precompiled hack.
Magecart hacker group have reportedly performed malicious activities from 2016. The research team of RiskIQ organization reported finding hourly notifications for websites being infiltrated by its skimmer malware in its research of a Magecart incident in 2018. Magecart was listed as "Most Dangerous Hackers In 2018" by a magazine called Wired.
Magecart attack in action
The idea for the Magecart black-hats is to deliver and obfuscate JS payload. Their method contains modifying the source of the targeted software or inflicting it with malware. Many RCE (Remote Code Execution) exploits were enumerated by the research teams. Uploading their code to an abandoned online Repository (such as GitLab) is one cunning approach for black-hats to deliver their malicious payloads. As a immediate result, various web applications will soon have malicious payload that is actively being used. With the attack on MyPillow webapp, Magecart hacker group demonstrated its willingness to proceed forward. The report from the security research teams claims that although MyPillow swiftly identified and eliminated the initially crafted malware, the hacker group "Magecart" was still able to access the website.
Mageccart's attack steps
The idea behind Magecart's attacks is known as data skimming, for such an attack to be successful, the following conditions must be met:
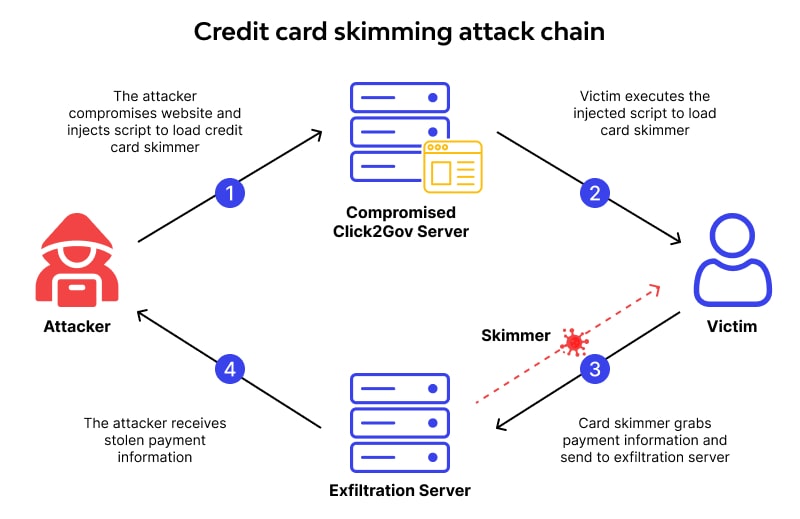
- Step 1: The intruders must get on your website: The hacker has two options for accessing your website and executing the skinning code. Even the targeted networks may be broken into. Sometimes they even leave after the third-party seller arrives, making it simpler to get to the goal at that point. You require a browser since tags occasionally link to harmful scripts.
- Step 2: Scrutinize private data from a form: multiple techniques for obtaining data are present, but the code used for skimming includes JavaScript, which listens for and gathers personal data. The intruder always notices the approach and makes an effort to keep track of keystrokes made on the sensitive page. Additionally, they look for anything that has intercepted data in a particular webform area, such as the credit card's CVV data. In order to evade discovery, the attacker will typically conceal the malicious payload inside the other code.
- Step 3: The final and most straightforward step of the procedure is to beacon data back to public infrastructure, owned by the hacker group. Once they breach your web application, hackers will begin to gather more and more information by scraping and other techniques. As soon as they are able to convey data from the browser of the end user, which will travel to any place via the internet.
Magecart history
Even though the first Magecart activity was officially reported in 2015, they are active since 2012.
Many online retailers are utilizing the targeted framework for online shopping, also known as “Magento”. This causes a huge attack vector. One of the most popular and known attack of the black-hats is in 2015, that’s when their name was shaped. Research organizations enumerated that over 3000 instances of the framework were compromised.
This quantity of hacked stores increased quickly during the ensuing years. By 2022, the same reporting agencies have found over 70,000 compromised establishments that had once housed a digital skimmer. If you count the victims of the supply chain attack, more than 100,000 stores were impacted.
Cybercriminals target various open source ecommerce platforms in addition to Magento while performing web skimming. For the most popular sites, we monitor breaches monthly.
How to prevent magecart attack
Website owners with minimal resources shouldn't give up hope, even if hackers can utilize sophisticated tactics to plant and conceal skimmers. Free website scanners can assist in identifying unusual connections made by programs like Magecart, and browser developer tools can help examine the contents of such connections.
A guide with comprehensive instructions on how to conduct such investigations and a list of helpful tools particularly made for locating and removing Magecart infections was released by Trustwave, a research from SpiderLabs.
Consider initially listing all of your outside e-commerce and internet ad providers. You may mandate that they perform audits or other self-evaluations of their code.
Subresource integrity should be implemented to prevent the loading of updated scripts without your consent. To find these scripts, you'll need to actively train your devops staff and do a comprehensive code review.
Instead of using the servers of any of your suppliers, host as many of your third-party scripts on your own as you can. Given that the typical e-commerce homepage has dozens of third-party sources, that is easier said than done.
Check your endpoint security provider to see if they can thwart attacks like Magecart and others that involve third parties.
Make sure your cyber insurance covers this sort of breach.
What Can Merchants Do to Prevent Magecart Attacks?
Take the following actions to lessen the danger of Magecart as well as other client-targeted attacks:
- Create a list of all third-party JS payload code on your web application to help you identify it.
- Request code auditing from outside suppliers to make sure the code is their own and free of viruses or dangerous instructions.
- Instead of using third party solutions, whenever possible, switch to first-party ones . You should also try to execute your program on your own servers wherever possible. This can be difficult considering how highly reliant today's stores are on outside sellers.
- Implementing HTTP Content-Security-Policy headers adds an extra layer of defense against code injection attacks such as cross-site scripting (XSS) and clickjacking.
There are now specific programs that handle client-side defense and aid in avoiding Magecart assaults.
What Can Consumers Do to Protect Themselves?
When purchasing online, customers put their faith in eCommerce sites. While eCommerce businesses are in charge of protecting their websites, each individual customer may also take precautions. Consumers should think about using these security precautions:
- Avoid providing personal information on unreliable websites.
- Create one-time use credit cards by using a service like privacy.com.
- Check the domain URL to make sure it isn't an attacker-created phony domain, having a similar name record.
- Use browser add-ons to stop JavaScript from loading from shady sources. This may aid in lowering the attack surface. Be aware that this method cannot defend against malicious code that is already present on reliable websites.
Subscribe for the latest news

















