Kubernetes Security
Cybersecurity is essential in today’s world, and when it’s about your business data, applications and assets, its importance is even higher. So, ensuring safety for the K8s configuration is surely a task of the highest priority for your business venture.
Wondering how to get started with the process? Well, this guide has all that you need to focus on.

What is Kubernetes (k8s) Security?
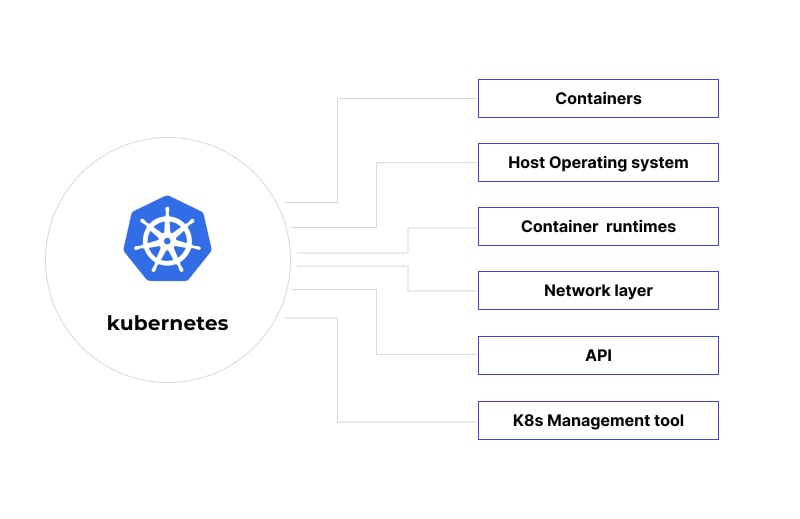
K8s is one of the most famous container orchestration platforms offering endless capabilities. It’s highly portable and highly extensible. Its increasing use has forced the DevOps team to strengthen digital security benchmarks set for the cluster, K8s API, container, etc.
Cybersecurity challenges are becoming a serious matter of concern as nearly 55% of projects are delayed because of weak security. 98% of K8s users have admitted to dealing with one or more security trouble per year.
Safeguarding K8s is the process of using multiple techniques to make sure that the applications developed using K8s are perfect and cyber-resilient.
Securing Kubernetes is basically based on 4C’s that are explained next.
- Cloud/Colocation facility /Corporate datacenter
The foundation of K8s security is the infrastructure/environment used for clusters in it. Either cloud or data centers are used for them. Hence, the best and proven practices should be used to protect the basic setup of the platform.
- Clusters
They are a key component of K8s, and their security should cover all the cluster-based apps and K8s APIs.
- Code
Unprotected codes act like an attack vector allowing cyberpunks to harm any of K8s resources and applications. Hence, relevant code protection techniques must be deployed. Experts recommend using TLS encryption, authentication, discarding unused ports, and scanning codes regularly to keep everything safe.
- Container
The degree of perfection in designing them decides the future k8s security scope. Container design must start with the smallest possible code base, and containers must be scanned continuously.
Why Is K8s Security Vital for a Container’s Lifecycle?
While K8s clusters are useful for container-based app development, their dynamic nature and distributed structure leave multiple scopes for Kubernetes security issues. No one standard security process will work on all the clusters as they pass through different levels of solution-creation.
The evolving runtime environment poses a great challenge for the IT and DevOps team to ensure that each pod is protected in transit. So, K8s security has to be taken care of thoroughly.
Kubernetes Security Issues
- Key vulnerabilities at build time
While building a digital solution and before its launch, mainly two problems may occur.
The first one is using codes from any unverified registries. Developers, knowingly or unknowingly, can use unverified codes that become a backdoor for malware and viruses.
Next, we have bloated base images. As containerized apps cannot hold much, image optimization should be prioritized. The more resources you use, the higher the risks.
- Key deployment loopholes
The most commonly occurring problem during the development stage are allowing too many privileges, not keeping multiple clusters apart, clusters moving laterally inside the application, and granting unauthorized access.
- Key runtime threats/risks
As an application reaches the runtime stage, infrastructure attacks, and their complex cluster nature are two main K8s security issues that developers have to deal with.
Kubernetes Security Best Practices
Ensuring impermeable Kubernetes network security is a key responsibility that every K8s user has to bear. Any leniency in this regard leads to endless troubles like data leaks, malware attacks, corrupted code usage, etc.
As one is involved extensively in Kubernetes container security, here are top practices, according to the development stage, to follow.
Build Phase
The majority of the actions related to app development take place in the build or development stage. If one manages to safeguard code, cluster, and containers at this stage, the developed application is most likely flawless.
Have a look at some of the most preferred SDLC stage K8s security practices:
- Image Scanning
Container images are crucial for container-based application development. As they are vastly used and are accountable for multiple crucial functionalities, it's important that container images are vulnerability-free.
Image scanning is an ideal way to make it happen. Done by an automated tool, image scanning helps you find hidden image vulnerabilities before they become a part of the development.
While you adopt this best practice, you need to make sure that the image scanning takes place at all the CI/CD pipeline stages and that there are no tampering possibilities.
- Reinforcing the host operating system
It’s important to ensure that containers feature only the least possible privileges. This is possible by using a fully reinforced OS featuring enough controls over system calls and file system access. Such an OS ensures that privilege escalation attacks are not occurring and containers don’t have any unwanted access.
- Minimizing the attack surface: Basic container images
An ideal container base image is one that asks for the least possible software package. This way, you will be able to trim down the attack surface of the container image. If such a container image is possibly available, one can easily create it using the Docker From Scratch directives. If you don’t want to create one, you can also use a Linux Distribution image or an Alpine minimal image.
Deploy Phase
Even if you managed to develop an application without any vulnerabilities, certain issues may occur at the deployment stage. Hence, you need to adopt the below-mentioned practices.
- Integrating Security Tools with Kubernetes Clusters
Not every security tool is aware of or compatible with K8s. Hence, one can’t feel relaxed just because security tools like NGFW or web access control gateways are active. They should be integrated with K8s clusters. This way, one manages to broaden the surface of security systems and catch vulnerabilities easily.
One easy way to integrate security tools with the k8s cluster is to enter the TCP or UDP port and IP address details of the workflow into the security tool perimeter and permit them to detect the linked K8s resources.
You can also take the help of security groups and limit the network connectivity of K8s nodes. This way, security groups will become more aligned with the K8s architecture.
- Harden Your Kubernetes Clusters
By default, the K8s cluster configuration is weak and not fully secured. Hence, you must try to harden it. You can improve the cluster configuration by conducting configuration reviews so that existing gaps can be figured out. Tools like Kube-bench will help you do the job perfectly and automatically.
You can also build a trust model for every cluster component so that you can control the cluster response. Using taxonomies and label governance is essential to implement the trust model.
Role Based Access Control is also a great way to strengthen-up cluster security as it allows you to control the cluster access and align it with the threat model.
Runtime Phase
The last phase, the runtime phase, has to be perfect and flawless so that the application remains functional all the time. You can ensure a vulnerability-free runtime phase by adhering to the below-mentioned practices.
- Network Security Controls
As most of the corporate-level network security controls are only focused on node-level security, certain run-time hassles are likely to take place. In general, only the back-and-forth traffic of a node can be controlled. However, it’s impossible to find out which service or node is running.
These are the basic runtime vulnerabilities.
As Kubernetes' workload is fully dynamic and new versions of an existing service keep on showing off anytime, managing security controls becomes harder than ever.
The ideal way to improve network-specific control is to set up a security definition within a workload. The declarative model is of great help in this regard.
Also, you need to make sure that the security definitions should be a key component of workloads and easily accessible by data centers and K8s distributions. Security definitions should be a part of every running workload. The two most preferred techniques to make it happen are using the K8s network policy tool or Kubernetes-native proxies.
- Enterprise Security Controls
Alone, network security controls are not very much useful. They should be combined with viable enterprise security controls. Some of the most recommended enterprise security controls are encrypting data in transit, collecting data in a manner that automated compliance reports are collected, and compliance is achieved continuously.
- Threat Defense
Threat actors can break into a K8s cluster and introduce any malicious content in it.
The result of a successful attempt could be malware inserted during run time or manipulating the cluster configuration. Both situations are harmful. Hence, the DevOps team should prepare an active and viable threat defense system.
Mainly, this system should have great intrusion detection and prevention abilities. With powerful intrusion detection, we meant that the threat defense system should be able to analyze data and figure out abnormalities.
Intrusion prevention involves blocking harmful actions and responses. However, both these tasks are not easy as there is a huge amount of data remaining under investigation. To make sure no data is missed or is at stake in the process, experts recommend aggregating the data by pods, using tools that can easily and automatically analyze the pod traffic, and monitoring IP addresses and domains continuously so that abnormalities are detected completely.
Additional Best Practices
The scope of Kubernetes security is wide and involves other concerns and practices. Hence, here are a few best K8s practices that one can use to reduce risks.
- PodSecurityPolicy (PSP)
PSP or PodSecurityPolicy is a feature-rich object that K8s uses to fix the security concerns existing in the pod configuration. As it becomes active, it pre-defines the marginal security requirements that every pod must adhere to before being a part of the cluster.
This practice is not easy-to-use and is delivered with certain limitations. Also, it can’t be activated on its own.
.jpg)
- Network Policy
Network policy is like a virtual firewall for every pod and the network administrator defines it. With this policy, network administrators have a chance to instruct involved pods on how to communicate with other pods. Network policy is automatically activated at the pod level and pods have the right to reject and accept this policy.
- Kubernetes RBAC
There are predefined Roles and ClusterRoles concepts that Kubernetes uses to explain what actions a user can carry out inside a cluster or concerned namespace.
ClusterRoleBinding is allowed to apply a specific role to all the resources. K8s users can also use RoleBinding to apply a role to the namespace. With these predefinition processes, Kubernetes can ensure that a cluster or namespace is not used beyond the defined criteria.
- TLS For Kubernetes Ingress
Applying TLS for k8s Ingress is an easy way to improve Kubernetes security.
Basically, Ingress is used to access a dedicated K8s cluster using any outsider cluster. In general, Ingress uses HTTP/S connection and defines rules for Kubernetes routing.
As one uses tls.crt and tls.key for Ingress, cluster traffic becomes more encrypted.
- Quality of Service
QoS or Quality of Service is an established Kubernetes security practice that K8s automatically uses for every class and pod. With this, it’s easy to optimize scheduling and pods eviction. The great thing about QoS is that it’s 100% customized. Developers can easily set customization rules for every pod.
- Authentication
Kubernetes authentication is a preferred way to protect the K8s API. In general, the API is backed by TLS and is accessed using port 445. This isn’t enough to keep API threats at bay. By using authentication, it’s easy to ensure that not any non-authorized persons or resources are using Kubernetes Authentication.
- Kubernetes Secrets
This is an in-built feature of K8s and helps you store critical data so that it’s not under attack. It’s not recommended to store passwords or SSH keys in plaintext or as a part of pod configuration or container images. Threat attackers can easily access this information from these places.
By creating secrets to store all this information, you can protect this data and reduce authorized access incidence.
Wallarm’s Solution To Protect Kubernetes
Wallarm is a leading API security platform offering multiple cutting-edge solutions to improve K8s security and keep the risks under control. These solutions include
- WAF
WAF or Web Application Firewall is an established application tool to protect web applications. The cloud WAF of Wallarm is best-of-breed and is compatible with all the leading cloud environments and API types.
It meets SOC2 and PCI DSS standards. Hence, its quality service delivery is unquestionable. With features like line auto-tuning, early zero false positives, integration with multiple DevOps tools & SIEM, and one-click installation, this is indeed the ideal Kubernetes API security tool to use.
- API Security Platform
Wallarm API Security Platform is the fastest possible way to keep API threats like malware insertion, unauthorized use, and over usage at bay. It gets along with your existing DevOps resources and empowers APIs from the beginning stage.
As far as its viability is concerned, the tool is best known for mapping the API changes in real-time, modifying the API and app topology, and finding out the sensitive data usage. Its effective use will help you keep OWASP Top 10 risks, harmful bots, and API-specific threats at bay. It is equipped with every required resource to improve your threat response time. It improves the threat observability of corrupted requests and sets real-time alerts and notifications.
It helps developers to find threats, create a remedy, and apply future protections on all sorts of APIs, microservices, and containers. Wallarm provides dedicated technical and deployment assistance as one tries to use this platform to protect the APIs.
FAQ
Kubernetes security is crucial because it protects your Kubernetes infrastructure and applications from various security threats, reduces the risk of data breaches and ensures regulatory compliance.
Kubernetes network policy is a set of rules that define how Kubernetes services and endpoints can communicate with each other.
To secure Kubernetes, you need to implement best practices such as using secure images, access controls, network policies, and secure configurations.
Kubernetes security risks include insider threat, unauthorized access, container vulnerabilities, and data breaches.
Kubernetes security is the set of policies and procedures implemented to secure Kubernetes infrastructure and applications against security threats.
Subscribe for the latest news

















