What is an Attack Surface? Definition & Management
While organizations are busy discovering a cyber-threat deterrence strategy, they often forget to analyze the entire area that is prone to face the wrath of an attack. Knowing the attack-prone surface is vital as it lets ventures determine which strategy is soundest and to which extent its execution is required.
Want to guard your organization from cyberpunks? First, find out your attack surface and shield it. And then let’s also comprehend its meaning alongside its other interconnected details.

What Is An Attack Surface?
In a practical sense, it refers to all the application end-points, software apps, digital tools, security loopholes, and everything else that can help a hacker to gain admission to an individual or organizational data and digital assets. In literal terms, the attack surface definition means absolute area/assets/environment that is gullible to a cyber-attack.
The means that bad actors use to exploit data or digital assets of enterprises or individuals are known as attack vectors. The likelihood of facing digital threats is directly proportional to the attack-prone surface area. More area means high hazard possibilities, as cyberpunks will be proffered with ample prospects. Hence, one must try to keep the surface reduced.
The 3 Types of Attack-Surface
- Physical
It refers to the digitized possessions and resources used in physical form. Mostly, hardware elements and devices that an organization/individual uses are elements of this category. For instance, data-driven devices, servers, wearable devices, printers, IoT devices, hardware like hard disks & pen drives, and so on.
A threat actor utilizing unauthorized access techniques can effortlessly access all these attack vectors, and they have the potential to cause serious damage.
Have a look at the menaces that a physical attack-surface is likely to bring to life.
- An ill-intended employee can misapply privileged access to use physical vectors & steal the mission-critical data saved.
- Hackers/threat actors can access all these devices in an inappropriate manner and rob the information or misuse it.
- Baiting is a potential threat that physical attacks surface bears. In this kind of attack, the base actor releases an infected USB device in the public domain with the hope that any user device can use it and the infected code will find a target.
- Digital
It surrounds the all-inclusive digital resources that you use and is unprotected. For an individual, it refers to a website that has weak passwords and is accessed with a protection or antivirus tool or VPN. For a company or its branch, it includes attack vectors falling outside the reach of the firewall used and being released in the public domain without any protection.
On average, the digital attack-prone surface covers servers, networks, websites, and dependencies, forgotten software/marketing accounts/websites, and rouge assets like impersonating apps, and typosquatting domain.
- Social Engineering (SE)
It refers to emotionally weak individuals that are linked with your organization in any sense. Such individuals are prone to make rational decisions and can easily fall for the hackers’ trick. Threat actors can trick such employees or associates and force them to steal particular databases or data of their interest.
The technique paves the path for many cyber-attacks. For instance, CSRF attacks, phishing, whaling, and so on. The ideal way to deal with this issue is to educate people about the dangers of cyber threats and encourage them to be responsible while handling confidential business data.
Relation Between Attack Vector vs Attack Surface
Even though both these terms are used concurrently, they have separate meanings. The attack vector is the pathway leading a threat actor to the targeted data/digital asset of an organization. For example, if a hacker injects malicious code into the company’s server that later manipulates the database, the attack vector in this situation is the server.
Combine all attack vectors within a business’s scope, and you’ll have an attack surface. Every in-house and 3rd party digital resource used, directly and indirectly, is its component.
Attack Surface Analysis And its Cruciality for you
Sound IT security infrastructure is doable only when one has insights into the attack-prone surface perils. Attack surface’s analysis is useful here. The term is used for the process of comprehensive analysis and figuring out hazardous attack vectors.
Even if it’s a labor-extensive task, it’s worth a shot. Organizations seeking improved attack surface cyber security should invest in it heavily as:
- It authorizes the organization to find out which attack vector needs primary attention
- It leads to early threat detection that further supports less damage
- It will help you figure out which all strategic changes one has to make in the present security approach to avoid risks in future
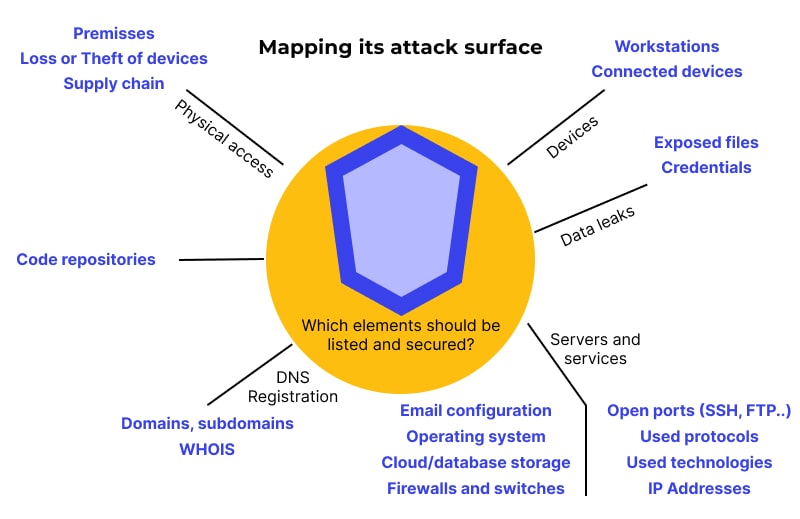
How Do You Determine The Attack Surface Of Your Organization?
As mentioned above, the attack surface comes with a wider periphery, and it’s not easy to have a clear distinction between what’s included in it and what’s not. However, one must clearly know the organizational attack surface for quick and effective hassle
Think about every crucial path via which data comes and goes in. They all are attack vectors. Every deployed security control like data validation tools, user authentication software, activity-logging technology, and so on is part of it.
Assess the kind of data your business uses and shares. Wherever that data goes, include those destinations in the attack-surface.
Figure out all these things and bring them together; you’ll have attacked the surface of your venture.
What Is Attack Surface Management?
ASM (Attack Surface Management) is the practice of ensuring that hackers have the least possible access to your attack-surface and that all the attack vectors are protected. It keeps threat actors’ thought processes at the pivot and allows organizations to do early and real-time threat detection and remediation.
ASM is done with the help of various automated tools like Attack-surface Detector tools, Sandbox Attack Surface Analysis Tools, and so on. They all are fully automated software keeping track of the suspicious activities happening in and around the attack vectors.
On a per-case basis, organizations can easily use these tools for internal and external attack surface management.
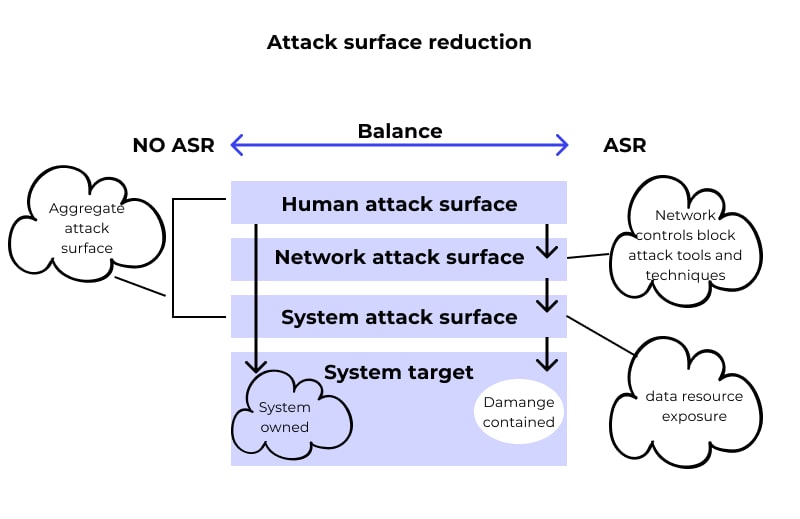
Tips to Reducing Your Attack Surface
As mentioned above, a wide attack-prone surface is a matter of concern for organizations and individuals. Hence, it’s very crucial that everyone should make an effort to keep it under control. Even though it’s a tough task, it’s achievable by following a few rules.
Wondering how to find attack surface reduction rules? Here are recommended actions to take for trimmed attack-prone surfaces.
- Check your ports and close the ones you’re not using now. Open ports are a serious threat when they are misconfigured and are in the hands of hackers. They can lead to tons of hassles like zero-day vulnerability. So, it’s better to close the ports that you no longer require.
- Reduce the MITM attack possibilities as much as possible. This is possible by ensuring that your public domains are backed by SSL, keep their HTTP a secret, and has a valid hostname, and use updated TLS/SSL encryption.
- Enforce viable email security strategies. Using DMARC, SPF, and DKIM are the appropriate email spoofing prevention techniques that organizations should use.
- Make sure that the domains and IP addresses you’re using are not outdated, flagged, or inactive. It’s better to adopt the auto-renewal option for both of these.
- Activate DNSSEC as this approach can protect the IP and DNS with adequate measures.
- Take the help of an effective vulnerability management approach. The approach allows organizations to do early vulnerability detection, evaluation, reporting, and remediation. Make sure you cover software, IoT devices, web applications, data-driven devices, servers, and networks. It will help you reduce the risk.
- Always use HTTP-based cookies as JavaScript-based threats like XSS can have severe outcomes.
- Keep an eye on data leaks and use viable data leak detection software. Use it for all your physical and cloud resources.
- Report a noticeable typosquatting domain as soon as you notice it. It’s observed that typosquatting domains are used by hackers to install malware and viruses. You can even invest in software with security features for automated assistance.
- Keep your DNS record protected. Unprotected DNS records can cause troubles like data leaks, data theft, misuse of information, and so on. So, ensure that they are well protected.
- Try to be less code-dependent. The more code you run, the higher will the entry points and bugs. That’s a treat for hackers as they have more opportunities to exploit you. So, run less code and stay safe.
- Uninstall the software or tools that you’re not using. Idle software/tools are potential entry points for hackers. Also, ensure that the OS or version of your software/devices is always updated.
- For effective attack surface reduction, separate and segment the network you’re using. Keeping all of your digital resources on a single network is the biggest mistake that one can make. If that network is under attack, all of your assets will be at stake.
- Don’t trust the 3rd party vendors blindly and adopt best practices to protect and safeguard the 3rd party tools and software.
Follow these above-enlisted rules and enjoy the improved system and organizational security.
Subscribe for the latest news









%20Attack.jpg)







