Application Delivery Controller
The primary responsibility of every IT department is to control the volume of traffic and deliver unmatched performance. With the rapid pace of digital transformation, it is more essential than ever to implement solutions, such as an ADC to prevent data leaks, balance the workload among servers, guarantee continuous operations, and boost application performance.
SSL (secure socket layers) termination, health checks, TCP reuse, firmness, content substituting, and hoarding are only some of the well-known features of an ADC. Let's dig deeper into this topic to find out what an ADC is and how it behaves.

An overview of Application Delivery Controller
By definition, it means exactly what it sounds like. Delivery refers to the act of bringing a computer package to the user and giving the service to them, which has become increasingly important as the use of software applications has grown.
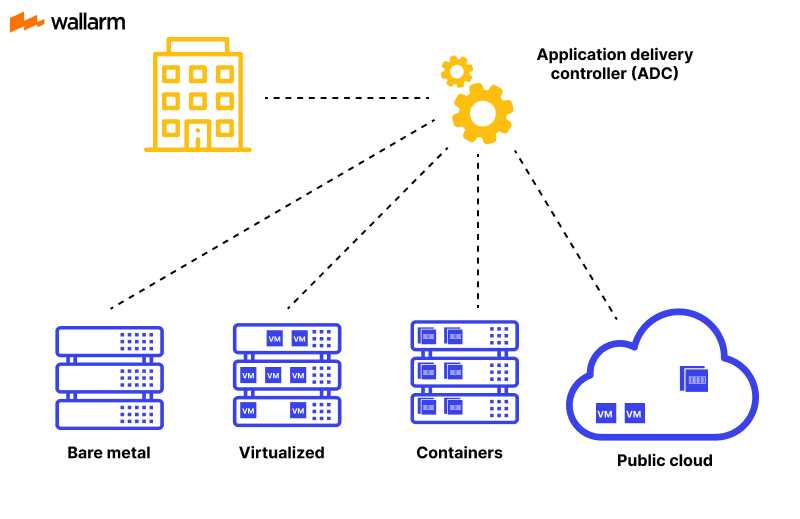
Using cutting-edge technologies and best practices, ADCs are the latest generation of interacting utilizations designed specifically to handle different database delivery needs by regulating traffic between clients and servers.
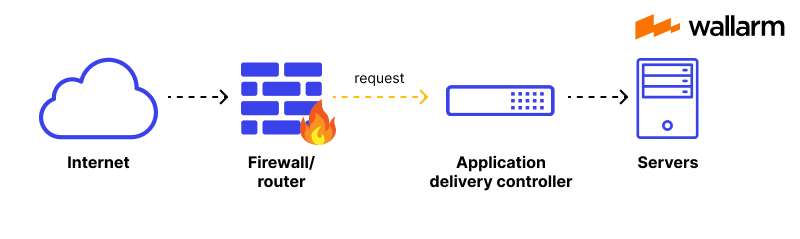
Basically, it sits amid a firewall and software programs, handling requests and responses while giving priority to the reliability, velocity, adjustability, privacy, and resilience of internet-delivered software packages.
Why is it important for organizations to use it?
Businesses now need to ensure that their software is accessible across multiple platforms, from traditional PCs and laptops to smartphones and tablets. Because of the wide variety of operating systems and platforms used by modern mobile devices, it can be challenging for IT departments to stay up.
With the help of ADCs, organizations can quickly and easily distribute software across several platforms and devices without sacrificing performance by making adjustments to the underlying network or protocol.
Organizations often deploy additional servers to provide availability in the event of failure. On the other hand, it can evenly distribute application loads across a group of running servers to ensure a smooth failover.
How Does an Application Delivery Controller Work?
In essence, an ADC is used to evenly spread the load for enterprise programs, as it improves their performance, dependability, resource utilization, and security. However, it also serve to accelerate applications, store and compress data, shape traffic, switch and multiplex content, and protect freeware.
Applying optimization strategies, an ADC boosts the speed at which WAN-delivered apps function. The persistence of an ADC is to act as a centralized location for handling verification, endorsement, and auditing for several application servers located behind cybersecurity protection.
Application Acceleration and ADC
It is suitable to collect performance information and implement enhancement at the ADCs level because it is the point of contact between end-user browsers a back-end web software package server. Features found in ADC that help accelerates applications include:
- Traffic Optimizations: They employ a variety of approaches for traffic compression to reduce data sizes and caching to offload previously serviced client requests, such as retrieving a JavaScript file.
- Blue/Green Deployment: In a DevOps environment, the ability to steer and monitor traffic in real-time to either old (blue) or new (green) deployments based on testing targets (% of traffic, geographic regions, and IP address ranges) enables continuous delivery with no downtime.
- SSL Offload (Transport Layer Security Offloading): Since decrypting and encrypting SSL/TLS sessions requires a large amount of computation, offloading the task from the web application servers to an application delivery controller (ADC) with custom encryption hardware significantly accelerates performance and reduces server load. Support for Elliptic Curve Cryptography (ECC) ciphers, such as AES-NI and GCM, and Perfect Forward Secrecy (PFS) with Elliptic Curve Diffie-Hellman Exchange (ECDHE) are included in the extensive SSL/TLS support. SSL termination, SSL bridging, SSL proxy, and SSL session ID reuse are a few further performance-boosting methods.
- Metrics: ADCs collect a wide variety of metrics, such as real-time traffic statistics, security events, server performance data, and system health, that can be utilized to acquire insights into issues and optimize the system.
Application Delivery Controller and Application Security
ADCs are the first line of defense for web application servers, which is why they are a key component of any company network. Secure application delivery controller (ADC) functions include:
- DNS Application Firewall: DNS infrastructure is vital for routing to and from networks in enterprise systems, and as a result, attacks on the DNS service have become a popular target for cybercriminals. Malicious and invalid queries, distributed denial of service attacks against DNS servers, and DNS flooding are all forms of assault against the DNS.
- DDoS Protection: DDoS attacks have become a common threat to company networks, so ADCs are the first line of defense for safeguarding online applications.
- Web Application Firewall: A WAF blocks attacks that exploit security flaws such as cookie poisoning, cross-site scripting (XSS), data form (buffer) overruns, SQL injection, and malformed HTTP packet attacks.
- Central Identification: An application delivery controller can serve as a central authentication point to manage client authentication and authorization and communicate with application access management (AAM) systems. Multi-cloud management relies heavily on having access to centralized authentication services.
What Are Virtual ADCs and Their Benefits?
All ADCs (application delivery controllers) act as a centralized management hub. They provide for the authorization, authentication, and accounting processes necessary for a secure application to operate.
These same services are offered by virtual application delivery controllers, but they are optimized for use in cloud environments and data centers that rely on virtualization technology. Despite being functionally equivalent to hardware ADCs, virtual ADCs have lesser performance because they lack the hardware acceleration provided by application-specific integrated circuits (ASICs) or dedicated network connections. Application distribution in the cloud has numerous significant advantages:
- Infrastructure simplification
The hardware-based method is being replaced with cloud-based application delivery. Providing quality while expanding internationally is best accomplished by using a public cloud service.
- Cost-cutting measures
Using the cloud to distribute packages has the apparent financial benefit of decreasing the need for new and updated hardware. The more efficient an application is, the better the user experience will be, which in turn will reduce the number of money businesses needs to allocate to support.
- Enhanced efficiency
With cloud-based application delivery, customers can instantly have access to services and information from any location using any device.
ADC vs. Load Balancer
The misconception that an ADC is simply a load balancer of the next generation is quite widespread.
Load balancing is just one of the numerous functions that may be performed by an ADC, which is a component of a network that offers a variety of services that are provided by OSI layers 4-7. The majority of ADCs also contains services for web application firewalls, GSLB, CGNAT, DNS, IPAM, proxy/reverse proxy, IP SSL offload, traffic chaining/steering, and traffic optimization.
Many also offer additional, more advanced ADC functionalities, such as server health monitoring, content redirection, and program production and monitoring services.
How To Choose the Right ADC Vendor?
The following is a list of important characteristics that should be present in an ADC solution in order to guarantee that the enterprise's applications and services will continue to function quickly and securely even when they are offline.
- It is necessary to handle apps and DevOps simultaneously
The present crop of ADCs does not adequately address the philosophical and technical gaps between DevOps requirements and those of the existing and future markets. Avoid hardware solutions and vendors based on legacy equipment that are resource-intensive and have complex and unneeded systems in favor of software-based options that are easy to adopt and administer.
Load balancing, web acceleration, scalability, application delivery controller (ADC), disaster recovery, and high availability are just some of the features that businesses need and may need in the future, and these features should be easy to use and deploy, as well as highly maintained.
- Success hinges on how well one performs ultimately
What's needed is an answer that prioritizes the efficiency of the program rather than just its uptime. Search for a comprehensive answer that tracks not just your connections but also your response times, server load, HTTP/S failures, and more.
- It needs to make sense of every piece of legitimate information
What's needed is a strategy that can read, process, and relay reliable information. Since last night's deployment, have your app servers slowed down? Do more and more HTTP errors seem to be occurring? Get your ADC up to speed on the key KPIs that will determine your performance and scalability.
- Multiple data streams must be monitored by the proposed solution
For this problem, we require a Layer 7-level answer. Try to find a solution that will keep an eye on HTTP responses, filter out error codes, and stop downtime at all costs.
- It shouldn't hinder DevOps
An approach that doesn't impede DevOps workflow. If you're an engineer, you know how important it is to find a product that fits seamlessly into your workflow as a reliable solution. The ADC should be unobtrusive, simple to set up and manage, and rich in useful performance data.
FAQ
Using an ADC can provide several benefits, including better application performance, improved availability, enhanced security, and reduced load on servers. ADCs also provide scalability, allowing organizations to handle more traffic and users without the need for costly infrastructure upgrades.
An ADC sits between clients and servers, intercepting and processing application traffic. It performs a range of functions to optimize application delivery, such as load balancing, SSL offloading, caching, compression, security, and traffic management. ADCs use algorithms to distribute the traffic across multiple back-end servers, ensuring that no single server is overloaded.
The role of an ADC is to optimize the performance of application delivery, ensuring that web-based applications are available, fast, and secure. ADCs perform several functions, including load balancing, SSL offloading, caching, compression, security, and traffic management.
An Application Delivery Controller (ADC) is a network device that sits between clients and servers, managing and optimizing the delivery of web-based applications. It ensures that application traffic is routed effectively and securely, while also providing features such as load balancing, SSL offloading, application acceleration, and security.
Subscribe for the latest news

















