Web Application Penetration Testing
The most ideal approach to discover defects in your web application is by doing infiltration check, otherwise called Pen Test or penetration test. This is the most generally utilized security check procedure for most web systems.
Penetration test is completed by starting mimicked assaults, both inside and remotely, to gain admittance to touchy information.
Web entrance check permits the end client to decide any security shortcoming of the whole web application and across its parts, including the source code, data set, and back-end organization). This aids the engineer in focusing on the pinpointed weaknesses and dangers, and concoct methodologies to moderate them.

Profound Assessment of Flaws in Web-Based Software Systems
The in-depth assessment of defects within web software systems, abbreviated as WADAF, operates as a digital defense system aiming to identify potential weak points within web-oriented tools. It operates as a protective wall, warding off potential digital threats by shedding light on hidden deficiencies waiting to be exploited.
Simplifying the Complexities of Flaw Analysis in Web-Based Applications
In essence, WADAF initiates an orderly succession of validated and expertly built-up cyber-attacks targeted at investigating the ruggedness of particular web tool defenses. It replicates authentic cyber-attacks, meticulously scanning the software, detecting passive pitfalls like overlooked system anomalies, technical glitches, or variations from normative operational and protection measures.
Keeping the perspective of an electronic invader in mind, this scanning integrates safeguarding maneuvers built upon discovered liabilities. After the assessment, the software operators are briefed on the unearthed security discrepancies and provided with a comprehensive draft recommending defensive strategies while outlining the potential aftermath of each exposed flaw.
The Crucial Role of Flaw Analysis in Web-Based Applications
As the digital realm continues to evolve, web tools have become a tantalizing target for culprits, majorly owing to the personal and delicate data they store. An unguarded web tool can swiftly morph into a secure haven for cyber rogues, providing them unbarred access to such vital details. In extreme cases, this can lead to wholesale system takeovers.
Consequently, WADAF plays an indispensable role as it guides organizations in identifying and promptly amending their security gaps in advance. It serves an insightful snapshot of the current security landscape and suggests possible improvements.
Driving Principles for Flaw Analysis in Web-Based Applications
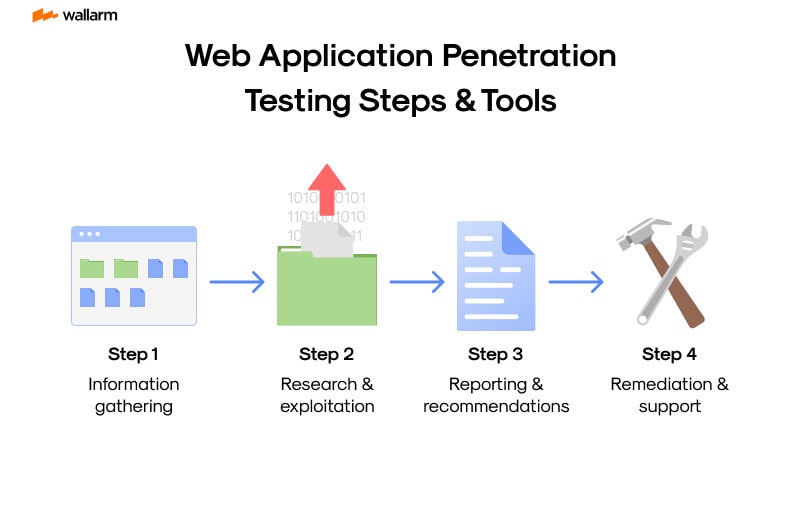
WADAF proficiently performs its responsibility by following a series of precisely crafted steps:
Step 1: Initiation: Research and Data Assembly: The inaugural step encompasses a thorough deep-dive into the software and consequently frames the blueprint for the evaluation.
Step 2: Examination and Detection: The examining committee employs technical stratagems to scrutinize the software, searching for standard security lapses.
Step 3: Evaluation: Post-examination, the assessing team devises robust strategies to comprehend the possible effects of the outed vulnerabilities.
Step 4: Reassessment: The assessing team identifies practical protective mechanisms that could be fused into the reviewed system while gauging the degree of data susceptibility.
Step 5: Record-keeping: The assessing team meticulously records details about the discovered bugs, exploitation techniques, and rectification recommendations.
Balancing Automated and Hands-on Approaches in WADAF
WADAF skillfully blends automated tools with human judgment. Despite automated tools acting as quick solutions for regular discrepancies, they flounder when it comes to complex violations which require human intuition. While hands-on evaluations can be grueling, they offer a comprehensive understanding of a software's protection landscape.
Resolutely, WADAF operates as a pivotal proactive security tool, bolstering software's defenses against virtual hazards. It adopts a coordinated approach to detect, analyze, and strengthen weak points, delivering a consolidated review of the software's security blueprint. With WADAF properly integrated, businesses are equipped to thwart any emerging virtual threats, thereby safeguarding their invaluable data from impending risks.
Understanding the Need for Web Application Penetration Testing
In today's world interconnected via technology, having a digital footprint is non-negotiable. An extensive range of businesses and institutions are heavily reliant on software solutions accessible through the internet for carrying out everyday tasks. Ensuring the safety of these internet-dependent applications via web application security audits is a critical component of establishing a robust cybersecurity setup. These audits identify, scrutinize, and alleviate potential security gaps that cybercriminals may take advantage of.
The Intensifying Cybersecurity Threat Landscape
The ease brought about by being digitally connected can both benefit and harm businesses—it broadens their exposure to various online threats. Digital lawbreakers are constantly devising new strategies to exploit any cracks in internet-reliant applications, which can lead to serious problems such as data breaches, financial damages, and a tainted brand image. A forward-looking study by Cybersecurity Ventures estimates that, by 2021, the worldwide cost resulting from cyber wrongdoing is projected to increase massively, touching $6 trillion per annum. This alarming forecast underscores the urgent necessity of security measures like web application security audits.
The Role of Web Application Security Audits
Commonly referred to as pen testing, this practice simulates a cyber attack on your software to reveal any flaws that can be turned against you. It entails investigating the software from an opponent's perspective, using similar tools and tactics that online lawbreakers might use.
Key objectives of web application security audits:
- Finding flaws in your software that digital lawbreakers can use.
- Evaluating the potential fallout of these attacks on your establishment.
- Creating plans and actions to mitigate these flaws.
The Prevailing Need for Proactive Safeguards
The escalating growth rate of cyber threats has made it too dangerous to respond to issues after they arise. Institutions must shift to a preventive approach toward cybersecurity. Undertaking web application security audits is a central part of this forward-looking strategy. By identifying and fixing vulnerabilities before they can be exploited, institutions can significantly lower their cyber threat exposure.
Compliance with Legal Obligations
In addition to keeping cyber threats at bay, executing web application security audits is key to meeting several regulatory requirements. For instance, the Payment Card Industry Data Security Standard (PCI DSS) mandates that businesses handling credit card information carry out regular pen tests. Non-compliance with these standards could result in hefty fines.
Building Customer Trust
In a world where data breaches take center stage, retaining customer trust is of utmost importance. Customers disclose their private and financial details onto the software, making its security critical. A single data breach can wreck this trust, resulting in customer loss. Regular security audits can demonstrate an organization's commitment to data protection, helping to maintain customer trust.
In conclusion, web application security audits are an essential proactive security strategy, crucial for staying one step ahead in the cybersecurity realm. By spotting and fixing vulnerabilities before they can be turned into threats, establishments can shield their data, stay in line with legal norms, and preserve customer trust.
First Steps to Web Application Penetration Testing
Exploring the Terrain of Web-Driven Software Security Validation
Venturing into the labyrinth of web-driven software security validation can often appear intimidating, especially for beginners. Needless to say, this captivating yet challenging pursuit can be deconstructed with an appropriate strategy. Presented below is a systematic guide designed to groom you for this key segment of digital defence.
Delve into Your Chosen Software
Your initiation into adeptness in web-derived software security validation commences with an exhaustive investigation into your chosen platform. Undertake meticulous study of its features, systems, and principal processes. Delve into the intricacies of the application by going through the relevant handbooks, scrutinizing the raw code, and deploying cutting-edge scanning facilities to disclose any latent vulnerabilities.
Establish the Validation Setting
Once you've defogged the software's aspects, it's high time to lay down the groundwork for your individualized probing domain. This stage typically calls for formulating a safe, sequestered spot for programmatically executing your sequence of validations, thereby eliminating any potential disruption to the running software product or its consumers. Your avenues might range from a mimicked computing atmosphere to a standalone validation server, or an independent network section.
Create the Validation Blueprint
Following the scene-setting for validation, your subsequent duty is to pen down a sturdy validation scheme. Decide on aspects such as the segments of the application you'll test, what forms of security violation models you'll undertake, and what instruments you'll mobilize. Strict adherence to the structured scheme will ensure methodical and comprehensive validation for yeilding premium results.
Commence the Validation Process
Once all blueprints are prepped, it's time for some practical interaction with the software. Utilize a plethora of approaches and supporting tools to scrutinize the application for the detection of any soft spots. Combine the straightforwardness of manual examinations with the complexity of mechanized scrutinization. Your mission is to spot any frailties that digital invaders could possibly leverage.
Evaluate the Validation Findings
After you've completed the validation tests, it's time to undertake a profound assessment of the collected intelligence. This involves looking closely at the obtained results, pinpointing system vulnerabilities, and contemplating their plausible impacts. A constructive evaluation will aid you in prioritizing susceptibilities according to their peril scales and temporal urgency.
Conclude by Compiling a Comprehensive Validation Report
For your last step, craft a detailed account elucidating all your validation undertakings. This report needs to shed light on the spotted software deficits, their probable repercussions, and initiated resolutions. Hand over this appraisal to the software designers or tech aficionados responsible for implementing the corrective measures.
To encapsulate, executing successful web-derived software security validation requires a deep comprehension of the selected application, establishment of a devoted validation workspace, drafting of a rigid validation blueprint, actual performance of the checks, thorough evaluation of the obtained data, and finally, compiling the entire process in a detailed report. By adhering to these pointers, you can guarantee precise, meticulous, and productive validation implementaions.
Acquiring Essential Tools for Effective Penetration Testing
In the arena of internet software intrusion checking, the equipment in your arsenal highly influences your breakthrough. This segment will tackle vital apparatus necessary for thorough intrusion checking, offering an all-encompassing key to aid you in overcoming this intricate expanse.
Gaining Insights into the Different Tools
Before delving in-depth into the different tools, it's crucial to familiarize yourself with panorama. Intrusion testing tools broadly fall into two brackets: programmed equipment and manually operated equipment. Programmed tools are software that execute tests with infinitesimal human interference, whereas manual tools need substantial human input.
Programmed tools enable you to identify typical loopholes swiftly, but they often don't match the meticulousness and contextual-awareness of manual ones. Conversely, manual tools supply an elevated level of comprehension, however, using them can be time-strenuous. An ideal strategy typically encompasses using both varieties of tools.
Crucial Programmed Tools
- Netsparker: This intrusion checking utensil eases the identification of vulnerabilities like SQL Injection and Cross-site Scripting (XSS). It's notable for its promptness and precision, cutting back on time wasted on baseless positives.
- Acunetix: Acunetix is yet another sought after programmed scanner that can spot an array of vulnerabilities. This tool also boasts of high-end capabilities like Software Development Life Cycle integration and inclusive reporting.
- OWASP ZAP: The Zed Attack Proxy (ZAP) is a free, open-source utensil from OWASP. With its highly personalizable nature, it's apt for both programmed scanning and manual intrusion checking.
Crucial Manual Tools
- Burp Suite: This tool is non-negotiable for any intrusion checker. It furnishes you with the ability to intercept, scrutinize, and alter traffic between your browser and the targeted application. It also complements with features to map application contents, automate custom breaches, and much more.
- Wireshark: Wireshark operates as a network proto-collector analyzer, allowing you to capture and scrutinize traffic on a computer network interactively. It's an invaluable tool for deciphering the operations during an intrusion checking.
- SQLmap: An open-source tool that streamlines the process of identifying and exploiting SQL injection flaws. Its effectiveness is amplified in the hands of an adept tester.
Electing the Suitable Tools
While electing tools, factors such as your testing needs, budget, and proficiency level are to be heeded. Here's a comparative spreadsheet to aid your decision-making:
| Tool | Type | Cost | Competency Level Needed |
|---|---|---|---|
| Netsparker | Programmed | High | Novice |
| Acunetix | Programmed | High | Novice |
| OWASP ZAP | Both | Free | Medium |
| Burp Suite | Manual | Moderate | Medium |
| Wireshark | Manual | Free | High-end |
| SQLmap | Manual | Free | High-end |
Bear in mind, tools are simply supportive aids. They are intended to bolster your testing actions, not supplant your skills and discretion. It's crucial to affirm the results produced by programmed tools and not hesitate to delve into manual testing.
The imminent segment will tackle schemes for triumphant internet software intrusion checking. Look forward to it!
Strategies for Successful Web Application Penetration Testing
Understanding the Foundation: The Web Application
The journey to fortified cybersecurity through web application penetration (pen) tests commences with a detailed comprehension of the root application. One needs to fully submerge themselves in understanding the application, from its infrastructure, to the technologies it utilizes, and how it processes information. This kind of knowledge acts as a compass, guiding a thorough inspection and highlighting areas that might be weak.
- The Application Structure: Getting to grips with the application's architecture is paramount. The focus should be on identifying the server setups, the database configurations, and the elements on the client side, all of which can uncover seemingly obscure vulnerabilities inside the system.
- Technological Insights: Venturing into the underlying tech layers provides a window into areas of potential risk. Different programming languages or setups could be more vulnerable to certain risk channels.
- Data Management: A firm grasp of how the application handles data enhances an overall understanding. This includes knowledge of how the data is stored, where it gets transmitted to, and how it is processed. These phases could present exploitable backdoors for cyber threats.
Designing a Test Plan
After decrypting the root application, it's time to create an elaborate pen test action plan. This plan needs to specify the tests to be carried out, the tools required for the same, the expected outcomes, the proposed timeline, and a contingency plan should results prove unforeseen.
Choosing the Ideal Instruments
Selecting the right equipment for pen testing could spell the difference between its success and failure. The market is flooded with a plethora of choices, each with their inherent merits and demerits. A few of the renowned ones include:
- Burp Suite: An end-to-end toolkit intended for evaluating web application security. It empowers testers to build, scrutinize, and modify web applications.
- OWASP ZAP: A tool curated by the OWASP community, its primary role revolves around automating audit procedures and facilitating hands-on analysis of web applications.
- Nmap: A network mapping tool typically used to chalk out network architecture. Its usual applications are to expose open ports and available services of a target system.
Execution of the Test
Now, it's time to put the geared-up plan into actual play. This phase demands diligent adherence to the test plan, effective utilization of the chosen instruments, and a precise recording of the outcomes. Staying alert to the finer details in this stage is key to ensuring no potential risks are bypassed.
Evaluation of Outcomes
After the test run, a thorough examination of the outcomes is crucial. This encompasses discerning the range and intensity of unresolved security flaws and ranking them based on their severity. The understandings developed from this exercise help plot out the roadmap for future actions.
Summarization of Findings
The final stage involves creating a meticulous report of the assembled findings. The report is meant to rightly call out security gaps, their level of threat, and recommend possible rectification measures. The report should be simple and direct, paving a clear path for next steps.
Undoubtedly, conducting a pen test for your web application isn't a walk in the park. Madly as it may seem, it demands a profound grasp of the application, a well-curated test plan, choice of adept tools, rigorous execution, thoughtful interpretation of results, and a crystal-clear report. Each of these stepping-stones act as a guardian, ensuring your web application remains an impenetrable fortress against any looming cyber threats.
Getting Your Hands Dirty: Practical Guide to Penetration Testing
Embarking into the complex field of internet defense, the greatest impact comes from the practical 'hands-on' experience of examining online programs. This element offers you a practical approach to assess websites for potential pitfalls and conditions, awarding you the key principles for effective scrutiny.
Shaping The Scrutiny Background
The initiation of a cybersecurity evaluation requires the manifestation of a safe, precisely-orchestrated scrutiny environment. This milieu could be outlaid as a replicated software platform or a separated network system that isn't linked to your primary workspace. The vision is to reduce the potential chaos that could disrupt your operational platforms or data flow.
For creating this secure examination setting, you have multiple platforms available. VirtualBox, a gratuitous open-source system for making virtual versions, is a widely chosen one. Besides, VMware or Microsoft Hyper-V can also be used. After setting up this replicated framework, websites susceptible to breaches can be established and tested like the Damn Vulnerable Web Application (DVWA), WebGoat, or Mutillidae.
The Scrutiny Outline
A conventional security examination for websites usually comprises:
- Understanding the Details: This marks the beginning of any scrutiny exercise. This step requires collecting abundant data about the selected program and its integrated setting, consisting of details about installed technologies, the application's framework, and potential weak spots.
- Hazard Evaluation: With the gathered data, it's possible to single out possible threats to the program, such as unauthorized intrusions, data breaches, or distributed denial of service attacks.
- Analysis of Breaches: In this phase, numerous applications and tactics are put to use to locate vulnerabilities in the chosen program. The process can be carried out manually, automated, or by a combination of both.
- Meddling: Post the discovery of weaknesses, a series of trials are performed to exploit these voids to gain unauthorized access or hamper normal operation.
- Record Keeping: After finishing the evaluations, the results need to be registered, and suggestions provided for reducing these identified vulnerabilities.
Basic Tools
A range of tools is available for testing website security. Few typically used ones include:
- Burp Suite: A comprehensive platform, specifically engineered to ensure the safety of web applications. It includes features for designing, analyzing, and altering online program traffic.
- OWASP ZAP: A gratuitous, open-source platform provided by the Open Web Application Security Project. It’s devised for automated scrutinies and human-driven examinations of web-based programs.
- Nmap: A strong framework for surveying a network to identify hosts. It helps in locating opened ports and active services on a targeted system.
- Wireshark: A powerful network protocol analyzer that allows capturing and examining network traffic in an interactive way.
- Metasploit: A landscape for designing and employing breach codes against a remote destination program.
Useful Advice
Several points to remember while performing a web app vulnerability test are:
- Legitimate permission must be secured before starting, as unauthorized tampering may have legal consequences.
- Be thorough during the data comprehension phase. The better informed you are, the higher the chances of finding weaknesses.
- Manual inspection can yield results that automated tools may overlook, so do not rely only on automation.
- Adequate documentation of your results is important. It assists during reporting and during retests after the issues have been resolved.
- Always practice ethical tests. The aim of these tests is to improve security, not to cause harm.
Ultimately, scrutinizing web applications is a complex but essential procedure to ensuring their safety. By understanding the process and selecting appropriate tools, you can successfully find and fix potential vulnerabilities.
Examining Web Application Penetration Testing Methodologies
Web application safety probing strategies act as valuable roadmaps utilized by security investigators, aiding them in spotting and exploiting soft spots that lurk within web apps. These handy frameworks, tried and tested, provide a foolproof approach to breach simulation activities, leaving no security aspect ignored during the search for potential system flaws.
OWASP: A Non-Biased Approach towards Web Safety
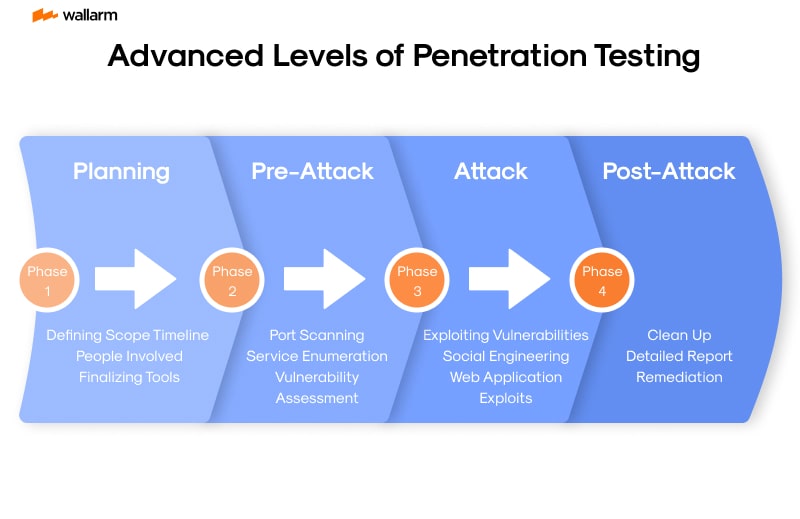
Spearheaded by a not-for-profit body, the Open Web Application Security Project (referred to as OWASP) raises the bar in offering impartial and practical insights regarding web application security. Among the most frequently opted-for strategies for probing the safety of web applications is the OWASP Testing Guide. This well-detailed manual proposes a methodical approach that consists of four steps:
- Projecting and surveillance: This preliminary step involves collecting insights about the app in question and its operating milieu. Aspects like the app's operations, the technologies it utilizes, and its architecture are analyzed.
- Unveiling: During this stage, potential hotspots are investigated by the prober. It might employ techniques like system scanning, hands-on verification, or a blend of both.
- The breach: This step witnesses the investigator capitalizing on the weak spots previously marked to gauge their role and prominence.
- Summarization: The last step revolves around documenting all findings, observing the soft spots unveiled, the actions undertaken to breach them, and remediation suggestions.
Breaking Down the PTES Strategy
The Penetration Testing Execution Standard (abbreviated to PTES) proves to be another favorable strategy. It explains a seven-step system for simulating breaches:
- Pre-engagement Dialogue: At this stage, the prober determines the test's scope and objectives, considering the legal aspects.
- Intel Collection: This stage focuses on accruing the maximum amount of info regarding the target application and its surroundings.
- Threat Projection: Potential threats and pathways are identified based on the amassed information.
- Weak Spot Analysis: At this point, potential system frailties are identified within the app.
- The breach: The 'soft spots' previously uncovered are then exploited.
- Post-Breach Analysis: This stage reviews the exploited system's worth while also retaining control for additional testing, if necessary.
- Summarization: Summarizing all findings and providing remediation solutions forms the last stage.
OWASP vs. PTES: A Glimpse
| OWASP | PTES |
|---|---|
| Specifically caters to web apps | Adaptable for any kind of breach simulation |
| An in-depth guide for each probing stage | Offers overview of breach simulation process |
| Highly regarded in the industry | Gaining traction, though not widely known |
| Does not cover post-breach phase | Includes a post-breach phase |
Both strategies facilitate a comprehensive approach to examining web app safety. Selecting one largely depends on the individual requirements of the tester and their acquaintance with the strategy.
Alternative Strategies
Beyond PTES and OWASP, alternatives such as the Information Systems Security Assessment Framework (ISSAF) and the NIST SP 800-115, a helpful manual for security appraisal and testing, exist as well. These tactics likewise offer a comprehensive perspective on breach simulations. However, their application in web app safety testing is much less widespread.
In a nutshell, web application safety probing strategies serve as a road map for pinpointing and exploiting vulnerabilities. They ensure a systematic walkthrough of all testing stages. Irrespective of the adopted strategy (be it OWASP, PTES, ISSAF, NIST SP 800-115, or any other), the main tactic is to fully comprehend it and implement it unfailingly.
Diving Deeper: Advanced Levels of Penetration Testing
We're diving into sophisticated avenues of security testing for online solutions where continual knowledge enhancement is essential, given the ever-changing nature of digital threats. As such, the measures and tactics we use to pinpoint and address weaknesses must keep pace.
Sophisticated Security Examination Techniques
Several distinctive and potent tactics are commonly utilized by security testers to single out vulnerabilities in online applications. They consist of:
- Fuzzing: This entails inputting random or unpredictable information into an online solution, observing how it reacts; a malfunction or an error may signal a vulnerability.
- Code Review: Manual analysis of an application's source code to spot potential weaknesses. It might be time-intensive, but its effectiveness is unparalleled.
- API Examination: As APIs are increasingly backing the functionality of web solutions, susceptibility tests for these interfaces are essential. Tests may focus on the mishandling of data, authentication inadequacy, amongst other issues.
- Sophisticated SQL Injection: Basic SQL injection methods are common knowledge, but specialized techniques that can circumvent standard security barriers exist. They involve intricate queries, encoded payloads, and more.
- Session Hijacking: This is where a user's interaction with an application is intercepted and potentially tampered with, allowing a cyber offender to pose as a genuine user and unlawfully access confidential information.
Sophisticated Tools for Security Testing
Beyond these tactics, numerous specialized tools can assist with security testing for online solutions:
- Burp Suite Pro: This expert-grade tool provides an array of features, from automated sweeps to advanced manual testing tools for web application penetration testing.
- OWASP ZAP: A free, open-source tool that enjoys wide popularity amongst the security testing community. It's packed with features such as automated sweeps and fuzzing.
- Netsparker: A pay-to-use tool that carries an automated sweep function, vulnerability analysis, and more. It stands out for its precision and simplicity.
- Acunetix: Another commercial tool with an extensive range of features for web application security testing – an ideal choice for large, intricate applications.
Structured Approaches for High-Level Security Assessments
When undertaking high-level security tests for online solutions, it's beneficial to adhere to an organized approach – providing assurance that all possible vulnerabilities get uncovered and addressed. Familiar methodologies include:
- OWASP Testing Guide: This well-received guide covers a vast spectrum of web application security testing topics. It maintains its relevance with continual updates to encompass the latest industry best practices.
- PTES (Penetration Testing Execution Standard): A comprehensive, seven-step approach that encompasses everything from initial interaction to reporting. It ensures uniformity in the execution of security tests.
- NIST SP 800-115: Published by the National Institute of Standards and Technology, this guide offers in-depth guidance on technical security evaluations, inclusive of penetration tests.
Given the constantly evolving online security landscape, it's essential to continuously expand your security testing capabilities - using these specialized tactics, tools, and approaches. It's critical to the process that testers remain engaged, learning, and adapting as digital threats morph and evolve.
Case Study Analysis of Successful Web Application Penetration Testing
Invigilating and assessing web tools is a vital procedure in fortifying them against possible threats. In this review, we will describe how broad-ranging evaluations of monumental digital landscapes occur, using actual occurrences to underscore how academic principles are used in forestalling security risks.
In-depth Analysis 1: E-commerce Outlet
A renowned e-commerce hub servicing several million clients was contending with habitual disruptions due to unchecked infractions and sporadic system failures. This prompted an exhaustive examination of the outlet's defense mechanism to discern frail regions and devise optimal responses.
Investigation Method
The examining ensemble's preliminary response was focused on an intelligence-gathering operation to accustom themselves with the implemented technology, the configuration of the e-commerce environment, and possible lapses that could allow unsanctioned ingress.
The following actions encompassed an in-depth exploration of the outlet's integral systems by deploying instruments like Nessus and Wireshark to expose frail regions that could be manipulated. Robotic security applications were also deployed to spotlight recurrent security cracks.
The ensemble then misused these exposed frail regions, such as SQL injections and cross-site scripting (XSS), to infringe the system and potentially incite its failure.
They eventually exhibited how a harmful interloper could attain repetitive illegal access to the system and skillfully hide their trail.
Findings
The evaluation excavated various defense vulnerabilities including SQL injections, XSS, and direct object referencing. These were fortified, significantly enhancing the outlet's durability against impending cyber invasions.
In-depth Analysis 2: Internet-based Banking Tool
A fiscal institution with crucial online functionalities expressed concerns over the security of its allied tools, urging a thorough web app defense analysis to isolate frail portions.
Investigation Method
The defense ensemble kick-started the task with a wide-ranging valuation of the technologies in use, the internet infrastructure, and possible soft points.
After this, the ensemble made use of digital software like Nmap and Nessus to spot weak areas and operational systems. Regular utilization of mechanized software aided in tracking and recording recurrent defense anomalies.
By deploying the exposed frailties, such as insecure direct object references and cross-site request forgery (CSRF), the auditors effectively originated unauthorized routes into the system.
Lastly, the auditors showed how a harmful actor could achieve regular, hidden access and obliterate evidence of the security breach.
Findings
This inquisition successfully unearthed critical defense flaws such as insecure direct object references and CSRF. The rectification of these issues considerably surged the tool's security caliber.
Crucial Revelations
These rigorous defense evaluations underline the necessity for continual defense trials on web tools. They underscore the vulnerability factors, even in platforms considered secure. Periodic evaluations enable organizations to uncover and eradicate these threats, amplifying their digital barricade.
The auditing process in both cases followed a pattern - starting with an initial intelligence-gathering operation, proceeding to an in-depth exploration, manipulating the disclosed flaws, and lastly showcasing how an intruder could sustain illegitimate access.
The archived data from these trials emphasizes the requirement for a pairing of robotic diagnostic logarithms and manual probing. Robotic software can effectively pinpoint typical weaknesses, whereas manual probing is pivotal for exposing sophisticated frail points which may elude robotic systems.
In conclusion, periodic web tool defense assessments are key factors in an organization's cyber defense policies. Applying lessons from successful evaluations enables these entities to refine their detection strategies, offering enhanced safety for their digital landscapes and sensitive data.
Overcoming Challenges in Web Application Penetration Testing
Hurdle 1: Insufficiency of Technical Skills
Top on the list of predicaments in network application intrusion evaluation is the inadequacy of technical know-how. Proficiency in various technologies, codes, and mishap awareness is the cornerstone of this process.
Countermeasure: Dedicate resources to learning and professional development. Propel your team to obtain distinctions like the Sanctified Hacker Specialist (SHS) or Intruder Security Licensed Expert (ISLE). Incorporating external specialists with a solid track record in your operations might also prove beneficial.
Hurdle 2: Restricted Timeframe
The exhaustive design, execution, and study of intrusion evaluations can be a drain on time reserves especially in a high-speed business setting.
Countermeasure: Strategise and allocate time for these operations. Immediate attention should be given to high-priority systems and software. Explore the possibility of mechanizing regular tasks for efficiency.
Hurdle 3: Opposition from Decision Makers
The mountain sometimes is not technical but administrative. Some decision-makers may balk at the prospect of intrusion evaluation for fear of operational interruptions, resulting harm, or exposure of weak points.
Countermeasure: Keeping the lines of communication open is fundamental. Stress the significance of intrusion evaluation in preserving the organization's resources and goodwill. Provide assurances that all operations will be secure and orderly.
Hurdle 4: Continual Emergence of Threats
The landscape of cyber threats is ever-changing. Mountains of fresh vulnerabilities are mined daily with cyber intruders inventing novel exploitative measures.
Countermeasure: Stay ahead. Digest security newsletters, join virtual networking communities, and participate actively in industry symposiums. It's important to revamp your evaluation approaches consistently to remain relevant amidst evolving threats.
Hurdle 5: Juridical and Moral Doubts
The hunt for weak points and subsequent exploitation attempts used in intrusion examination can stir up legal and moral uncertainties, further complicated by a lack of requisite approval.
Countermeasure: Secure expressed consent before initiating any intrusion examination. Keep within the bounds of moral standards and privacy laws. Documentation of all actions and findings is vital for transparency and accountability.
Hurdle 6: Resource Scarcity
Dwindling security resources are often the bane of many establishments, causing a hitch in conducting rigorous and consistent intrusion assessments.
Countermeasure: Maximize the use of freely available and communal tools when you can. Rank evaluations based on threat appraisals. If required, engage the services of an external intrusion evaluator.
In sum, although network application intrusion evaluation can present numerous obstacles, with the right stratagem and resources at your disposal, navigating these hurdles becomes quite achievable, effectively bolstering your organization's cyber defense.
Best Practices For Web Application Penetration Testing
Rigorous Assessment of Internet-Based Platforms
An advanced strategy for protecting internet platforms begins by decoding the intricacies of the individual online service at hand. Understanding details about network structure, the technology strata involved, data movement characteristics, and probable transmission vertices is crucial for identifying concealed security loopholes and crafting a complex evaluation plan.
Thorough Examination Regimen and Profound Analysis
An intense scrutiny of the safety features of an internet platform demands a meticulous, methodical evaluation strategy. Articulating expected results, probing the inherent characteristics of the platform, opting for suitable inspection models, and suitably pacing the task is indispensable. The scope of the evaluation must also be clearly delineated to prevent disruption of business processes.
Dual Strategy: Automation and Human-guided Methods
Prime security applications can promptly highlight usual shortcomings. However, they might occasionally fail to detect advanced weaknesses demanding a deep comprehension of the platform's functionality and data movement. Thus, integrating a human-guided approach with machine-driven checks can be beneficial in revealing understated security weaknesses.
Systematized Deficiency Assessment
Detected security breaches should be classified according to potential damage and feasible repercussions to the corporation. Aptly classifying these deficiencies facilitates prioritizing of the most severe infringements. Instruments like the Shared Vulnerability Assessment System (SVAS) can methodically sort and control these safety risks.
Repairing Inadequacies and Post-treatment Analysis
After weaknesses are pinpointed and categorized, the rectification process is the subsequent important phase. This repair process encompasses rectifying identified weaknesses and then auditing the online service to ensure each issue is resolved. Detailed documentation of the rectification task and the following assessment outcomes should be maintained for future reference.
Ongoing Examination Cycles
Safety audits should not be standalone occasions, but recurring tasks to monitor changing platform features and burgeoning security threats. The chore of addressing security risks requires continual dedication to sustain a secure network setup.
Compliance with Regulatory and Corporate Guidelines
Fundamentally, all actions linked to cybersecurity audits must comply with relevant legal and company policies. This compliance process should incorporate obtaining necessary permissions before starting examination phases and making sure all measures remain within lawful boundaries.
Collaboration with Essential Associates
Involving crucial associates during the audit process ensures harmony between corporate objectives and security precautions. Including stakeholders, technical members, and top-tier management augments the effectiveness of the examination process.
Thorough Documentation Maintenance
Maintaining records of evaluations and outcomes should be systematic and exhaustive. These accounts should include the audit plan, applied examination measures, exposed weakness, the instigated security actions, and subsequent re-examination outcomes. Such conscientious record-keeping is indispensable for planning subsequent audits and perpetuating optimal safety practices.
In conclusion, utilizing these methods enhances the efficiency of an internet platform safety audit, discovers and rectifies weaknesses, hence, increasing the security of internet platforms and protecting corporations from emerging cyber threats.
Importance of Regular Web Application Penetration Testing
Asserting the resilience of web application fortifications against possible online dangers is a critical aspect of a comprehensive internet safety plan. This forward-thinking strategy aids businesses in pinpointing prospective hazards in their applications before hackers set their sights on them.
Web Application Protection - Regular Monitoring is Key
As innovative tech solutions continuously adapt to meet shifting business objectives and user needs in our internet-centric landscape, even minor modifications can expose new weak spots. Consistent cybersecurity assessments enlighten us about these exposures early on, paving the way for swift fixes. This practice considerably minimizes the chances of a breach in the digital infrastructure.
In addition, the methods and machinery used by hackers are constantly acquiring sharper edges. Through routine cybersecurity assessments, businesses can maintain an advanced stronghold against these digital predators by persistently evaluating and advancing their online security measures.
Advantages of Frequent Cybersecurity Assessments
Regular scrutinies of web applications come with multiple benefits:
- Preemptive Security Methods: Routine checks empower businesses to identity and fix weak spots before they become targets. As a result, they can act preemptively in the face of a security breach instead of merely reacting to the situation.
- Ensuring Rule Adherence: Several supervisory entities, including those presiding over standards like PCI DSS and HIPAA, demand regular cybersecurity assessments as an element of their compliance procedures.
- Boosting Client Trust: Meticulous and ongoing assessments demonstrate a company's commitment to data safety, which enhances consumer faith and loyalty.
- Financial Prudence: By detecting and fixing blemishes before they turn into bullseyes, companies can avoid the hefty costs that come with a digital transgression, such as data recovery, legal fees, and the price of tarnished reputation.
Determining the Audit Frequency for Cybersecurity
Factors like the kind of data, the size of the program, application intricacy, and an organization’s risk acceptance level influence how often a web application should be scrutinized. Typically, web applications require a review at least once each year, but applications running a higher risk might call for more frequent checks.
In Closing
Given these insights, the regular inspection of web applications has become an indispensable element of solid online defense strategies. It not only allows companies to efficiently discover and mend flaws, but also helps them keep abreast of looming threats, supports their adherence to legal norms, improves consumer trust, and assists in dodging fiscal repercussions. Hence, regular cybersecurity assessments serve as a formidable protective barrier for web applications against online hazards.
The Future of Web Application Penetration Testing
Peering into the horizon, web application probe investigations are anticipated to adapt and shift in accord with the ceaseless flux of digital hazards. Advances in technology, augmented complexity of web programs, and digital assaults that are more refined all promise to steer this sphere in unanticipated directions.
Technology Progressions: Opportunities and Challenges
The incipient ascendancy of cutting-edge technologies such as Artificial Intelligence (AI), Machine Learning (ML), and the Internet of Things (IoT) subsidiary will undoubtedly affect how web applications are scrutinized for security weaknesses. These emerging technological tools can augment the proficiency of probing endeavors. However, they also usher in novel risks.
AI and ML capabilities serve to expedite and empower the task of pinpointing weak spots within web applications. They can sift through mounds of data at high speed and with precision, recognizing patterns or outliers that signal a likely security risk. Conversely, understanding and mitigating the new vulnerabilities that AI and ML introduce is a novel challenge for probe investigators.
The IoT framework brings with it a mixed bag. The rampant spread of IoT devices amplifies the possibility of cyber nefarious acts, amplifying the need for detailed probe investigation. However, the variety and intricate nature of IoT also amps up the difficulty of security scrutiny.
Increasing Web Application Multifacetedness
The intricacy of web applications is on an upward trajectory, with an incremental amount of features and coding content. This trend translates into a greater propensity for security weak spots, underlining the necessity for meticulous and proficient probe investigations.
Accommodating this intricacy also ups the ante for investigators. Unraveling tangled codes, spotting nuanced weak spots, and conceiving strategies to leverage these weak spots necessitates prowess and expertise. This fact highlights the significance of constant skill upgrades and learning for probe investigators.
Enhanced Skill Required in Cyber Defenses
The craftiness of digital hazards is ratcheting up with malevolent parties using more advanced ways to leverage vulnerabilities in web programs. This pattern is expected to persist, with malevolence morphing in response to fresh security measures.
To parry these rapidly shifting security threats, probe investigators need to be at the top of their game. Equipping themselves with the latest digital offense measures is critical alongside devising fresh strategies for identifying and manipulating weak spots.
Automation: A Partial Solution
The future looks certain to incorporate a broader degree of automation within web application probe investigations. Coded tools promise speed and precision, highlighting vulnerabilities that could slip through the cracks during human scrutiny.
But the reliance on automated means is no magic bullet. It is pivotal to bear in mind that automated tools are ultimately limited by their algorithmic programming, and cannot substitute human insight and expertise. It points towards a future where automated scrutiny coexists with human-led parameters to harness the potential of both.
Summarizing, we foresee that the future trajectory for web application probe investigations hinges on the burgeoning of cutting-edge tech, growing intricacy of web programs, and shrewdness of digital threats. To ensure readiness, probe investigators should constantly upgrade their knowledge arsenal and embrace automation, without loosening their grip on thorough human scrutiny.
Upgrading Your Skillset: For Modern Web Application Penetration Testing
In the wildly fluctuating sphere of digital safety, it's crucial to stay abreast of rising trends. A distinct component that's made swift strides is the scrutiny of defensive steps executed in web-based apps, a process commonly coined as web app penetration auditing. The high-speed unveiling of fresh assaulting schemes and susceptibilities is nothing less than astonishing. To remain buoyant in this persistently shifting environment, fine-tuning your proficiency is primary. This narrative sketches an action plan to polish your keen insight to fulfill the prerequisites of present-day web app penetration auditing.
Acknowledging the Prevailing Circumstances
When considering the enhancement of professional prowess, it has value to examine the existing landscape of web app penetration auditing. Presently, web apps are complex, stratified constructs weaving together multiple technologies, featuring exclusive programming languages, data reservoirs, and cloud-assisted services. This technological intricacy fosters user functionality and experience, but inadvertently, it also births a myriad of potential security gaps.
Familiar loopholes have been SQL infiltrations, Cross-Framework Scripting (XFS), Cross-Framework Request Fabrication (XFRF), and flawed safety setups. Nonetheless, fresh categories of susceptibilities continue to surface. For a penetration auditor, it is vital to stay updated about these susceptibilities, understand their operations, and implement successful breaches.
Expanding Your Tech-Mastery
The first step towards honing your skills lies in boosting your technical literacy. This signifies fostering an in-depth understanding of the tech-tools involved in today's web apps. Below are some crucial areas of study:
- Programming Languages: Understanding languages integral to the building of web apps, such as JavaScript, Python, Ruby, PHP, and Java. This understanding equips you to decipher the code being tested and identify potential weak spots.
- Web Tech-Room: Get used to tech-tools like HTML, CSS, and JavaScript, in conjunction with systems like AngularJS, React and Vue.js. Understanding these will help you appreciate the design and workflow of web apps.
- Databases: Learn about the functioning of databases and their interplay with web apps. This encompasses mastering SQL and NoSQL data reservoirs, including general susceptibilities associated with them.
- Cloud Services: Many modern web apps are leveraging cloud services for their hosting, storage, and more. To understand these services' workflow and potential safety gaps is beneficial.
Relevance of Current Tools
Along with sprucing up your technical expertise, it's advised to familiarize yourself with the latest tools applied in web app penetration auditing. These tools can de-complicate certain tasks, detect vulnerabilities more effectively, and make the entire auditing process smoother. Some common tools include:
- Burp Suite: A comprehensive tool engineered for web app safety examination. It includes elements for sketching, inspecting, and compromising web apps.
- OWASP ZAP: A free, open-source tool designed for web app safety checks. It's user-friendly and suitable for both newcomers and veterans.
- SQLmap: This tool concentrates on finding and leveraging SQL injection susceptibilities.
- Nmap: A powerful network explorer used to locate hosts and services on a computer framework.
Boosting Life-skills
While technical skills are fundamentally important, general life-skills also hold equal weight in web app penetration auditing. These include skills like problem-solving, critical thinking, and communication. Penetration auditors frequently have to brainstorm to discover and exploit susceptibilities. Additionally, they also need to efficiently communicate their discoveries and observations to developers, management, and other interested parties.
Staying Up-to-Date with Recent Trends
Lastly, it is crucial to keep track of the latest trends and progress in web app safety. Following related blogs, forums, social media accounts, attending web-seminars and web-meets, and active participation in online communities might be beneficial. Staying informed enables you to anticipate upcoming threats and tweak your testing strategies accordingly.
In summary, refining your skills for modern web app penetration auditing requires a mix of enhancing your tech-literacy, learning fresh tools, improving life-skills, and staying updated regarding latest trends. By embracing these steps, you will be prepared to tackle the intricacies of today's web apps, thus guaranteeing their safety.
How to Stay Updated in Web Application Penetration Testing
Navigating the high-speed landscape of cyber defence, particularly in the realm of web application infiltration testing, necessitates continuous awareness of current advancements. Novel risks and infiltration methods are unearthed with alarming frequency. In this section, we delve into diverse tactics and reference materials, to facilitate an edge in staying current with this ever-evolving sector.
Digital Platforms and Cybersecurity Circles
A potent method to remain informed is to consistently engage with digital platforms and partake in cyber defence circles. Digital hubs such as OWASP (Online Web Application Security Porject), HackerOne, and Bugcrowd present a treasure trove of data about emergent hazards, cracks and protective measures. These platforms also run interactive forums where one can engage with other cyber defence experts to gain insights from their feats and failures.
Comparison Factsheet on Digital Platforms:
| Platform | Synopsis |
|---|---|
| OWASP | A non-profit consortium devoted to fortifying software safeguards. Regularly publishes countdowns of the most menacing web application security hazards. |
| HackerOne | An interface which fuses companies with infiltration testers and cyber defence analysts. |
| Bugcrowd | A shared security stage which curates bug bounty initiatives. |
Courses and Accreditations
Acquiring ongoing courses and accreditations is another proactive approach to stay ahead in the wave of information influx. These not only stimulate your intellect and practical knowledge, but also help maintain a grip on the freshest techniques and recommended procedures in web application counter-intrusion testing. Premium certifications in this specialization include Certified Ethical Hacker (CEH), Offensive Security Certified Professional (OSCP), and GIAC Web Application Infiltration Tester (GWAPT).
Directory of Premium Accreditations:
- Certified Ethical Hacker (CEH)
- Offensive Security Certified Professional (OSCP)
- GIAC Web Application Infiltration Tester (GWAPT)
Network through Symposia and Webinars
Symposia and webinars are instrumental in staying updated on the current trends in web application infiltration testing. These platforms offer a chance to glean insights from industry stalwarts, learn about innovation in tools and stratagems, and network within the community. Renowned cybersecurity symposia include DEF CON, Black Hat, and RSA Symposium.
Periodicals and Blogs Digest
Cybersecurity corporations and experts often run blogs and newsletters that focus on the latest trends and happenings in the cyber defence industry. Regularly reading these publications can help in keeping pace with the times with minimal effort. Recommended cybersecurity blogs and newsletters include Krebs on Security, Schneier on Security, and Dark Reading.
Harnessing Social Media
Professional networking platforms like Twitter and LinkedIn have emerged as potent channels for current information in the cyber defense universe. Numerous experts and organizations consistently share updates about newly discovered risks, exploits and defensive measures. Making connections with these individuals and entities could help you stay tuned with what's new in the field.
To sum up, staying ahead in the web application infiltration testing process demands a proactive attitude and an unwavering dedication to continuous enlightenment. By deploying the resources and strategies described here, you can position yourself at the vanguard of this fascinating and crucial discipline.
The Role of AI in Web Application Penetration Testing
Artificial Intelligence (AI) is no longer just jargon in the current technological framework but has emerged as a central entity across multiple fields, cybersecurity and web application penetration testing included. The integration of AI in this realm has revolutionize how cybersecurity specialists conduct these crucial tests, bestowing significant enhancements in dependability, detail, and speed.
How AI Enhances Penetration Testing
One of the remarkable features of AI is its ability to operate independently, adapt as per its learnings, and make well-grounded decisions. All these augment penetration testing phenomenally. AI can adeptly manage monotonous tasks, interpret enormous volumes of data, and discover patterns that could perhaps evade the human eye. The upshot is that penetration tests are done faster and more accurately, enabling the discovery and resolution of security vulnerabilities faster.
Accelerating Penetration Testing with AI
The automation brought about by AI in the process of web application penetration testing is perhaps its most significant contribution. The traditional ways of doing penetration tests were both time consuming and resource intensive and called for superior levels of expertise. But with AI at the helm, much of these tasks can be autonomously managed, freeing up human testers to focus on more complex issues.
For instance, AI can take on the task of combing through a web application to unearth potential security loopholes, identify possible weak points such as faulty code practices or outdated software, and highlight these for closer examination. This streamlines the testing process and minimises the risk of overlooking security threats.
Predictive Analysis by AI in Penetration Testing
AI's prowess in processing gargantuan amounts of data and recognizing patterns lends an additional edge to penetration testing. By analyzing historical security breach data and previous test data, AI is capable of forecasting potential security vulnerabilities. This prescient analysis equips organizations to better direct their security strategies and stymie possible security breaches in their bud.
AI's Dynamic Learning Ability in Penetration Testing
A key contribution of AI to penetration testing is its ability to dynamically learn from the data it processes. Unlike traditional methods that rely on fixed scripts, AI adapts its methods based on the data it analyzes. If it encounters a new type of vulnerability, it integrates this information into subsequent tests. This ongoing learning and adaptation capability render AI an invaluable asset in combating cyber threats.
AI Limitations in Penetration Testing
In spite of its substantial benefits, AI isn't foolproof. Its performance and success largely depend on the quality of its learning data. If the data source is biased or inadequate, the efficacy of AI can be undermined. Moreover, as versatile as AI is, it cannot replace human insights and judgment. Trained human testers play a crucial role in interpreting AI results and making well-informed decisions.
Future of AI in Penetration Testing: The Road Ahead?
The future is likely to see an enhancement in AI’s role in web application penetration testing, spurred by advancements in AI technologies. This will enable AI to get increasingly adept at identifying and managing vulnerabilities. However, the notion that AI will replace human testers needs to be disregarded. The ideal testing approach will always involve a synergistic combination of AI's abilities and human expertise.
In conclusion, AI is transforming web application penetration testing by ramping up the speed, precision, and the wealth of detail. While it has its limitations, the need for skilled human testers to complement the capabilities of AI remains essential. Balancing the use of AI's abilities and human expertise will be crucial moving forward.
Web Application Penetration Testing: Protecting from Cyber Threats
In the current digital landscape, mounting cyber threats pose significant worries for corporates and individuals alike. The alarming upsurge in cyber delinquency has nudged the need for powerful protective countermeasures to shield web software against lurking risks. A notable preventative strategy is the web application penetration trial, designed to discover and rectify flaws before they fall prey to malevolent intruders.
Grasping the Concept of Cyber Dangers
Internet-based hazards or cyber risks can lead to potential damage or losses. These could come in several forms such as harmful software, deceptive email scams, service disruption assaults, and unauthorized data access incidents. Cyber felons tend to zero-in on web software due to their extensive reach and the precious data they encapsulate.
The web app penetration trial is a linchpin in squaring off with such risks. By enacting cyber invasions, penetration auditors can detect weak links in the web software and suggest suitable defensive strategies. This forward-looking approach to safety aids in warding off prospective cyber risks.
The Importance of Web Application Penetration Trial as a Cybersecurity Tactic
The web app penetration trial is fundamental in securing against cyber perils. It entails mimicking virtual invasions on web software to determine potential exploitables by internet criminals. This operation comprises several stages:
- Strategy and exploration: This step involves an in-depth study of the web software and devising the trial protocol.
- Probing: The software undergoes a thorough examination to unearth possible weak links.
- Access acquisition: The auditor attempts to manipulate the discovered weak points to get inside the software.
- Sustaining access: The auditor strives to hold on to the software access to ascertain whether an internet criminal could obtain prolonged entry.
- Assessment: The trial outputs are scrutinized, and a comprehensive report is produced covering the identified weak links and mitigation recommendations.
Identifying and rectifying weak links in advance ensure the web software protection against cyber risks.
Anecdotal Account: The Significance of Web Application Penetration Trial
Let's consider a large-scale online retailer's situation to underscore the web application penetration trial's importance. The firm had a formidable security fortress but opted for a web application penetration trial to reassure themselves regarding their system's absolute security.
The trial unveiled several overlooked weak links that the firm's security brigade had missed. These susceptibilities could have potentially aided cyber felons in accessing critical buyer data. By discovering and rectifying these weak links, the firm could beef up their security shield and safeguard their clientele from possible cyber risks.
Overcoming Hurdles in Web Application Penetration Trials
While web application penetration trials are robust mechanisms against cyber threats, they come with their own set of complications. These involve an inadequate comprehension of the trial process, opposition from key members, and the requirement for specialist auditors.
To circumvent these obstacles, it becomes exigent to enlighten key members about the penetration trial's significance and the possible perils of not undertaking these assessments. Also, funneling funds into training and toolkits can equip auditors with the requisite knowledge and tools for conducting meaningful trials.
Conclusion
To summarize, the web application penetration trial is quintessential in securing against cyber risks. By detecting and fixing weak points before exploitation, it aids in preserving web software and the crucial data they house. Although getting a penetration trial done comes with its challenges, the merits certainly offset minor hitches, making it an indispensable asset for addressing web application security concerns.
The Economics of Web Application Penetration Testing
Undeniably, in the context of safeguarding digital data, the saying 'time is of the essence' attains a decidedly exceptional connotation. With the costs associated with a security breach escalating fiercely and quite literally as each moment passes, companies can ill afford to lax in maintaining their cyber defensive mechanisms. Among these, one straightforward solution lies in periodic penetration testing for web applications. This detective approach helps businesses spot vulnerabilities within their systems before cybercriminals leverage them, which can prevent heavy financial losses.
The Economic Consequences of Ignoring Penetration Testing
Understanding the monetary aspects associated with web application penetration testing necessitates a closer examination into how taking this procedure lightly can dent your firm's finances. According to a study by the Ponemon Institute, businesses had to deal with an estimated mean financial setback of $3.86 million following a security breach in 2020. However, it isn't just the apparent costs such as forensics, legal procedures and remediation, but the silent losses such as diminished customer faith and the corporation's maligned image that multiply the financial impact.
And these are only average figures. Large corporations or those operating under stringent regulations may have to face steeper consequences. An illustrative example is the 2017 breach of Equifax that compromised the personal data of approximately 147 million people, culminating in a direct fund depletion of over $1.4 billion.
The Fund Allocation for Penetration Testing
We must weigh these costs against the money spent on conducting a penetration test on a web application. There is variability, depending on the complexity of the web application and the extent of testing, but a safe estimate puts the cost of a penetration test between $5,000 and $50,000. The comparative nature of this expense is evident when stacked against the potential aftermath of a security breach.
Moreover, regular penetration tests have long-term cost-effectiveness. They can save companies from financial penalties attributable to non-compliance with data protection laws. It also reduces the chance of operational interruptions, whose implications on productivity and sales can result in considerable losses.
Scrutinizing Expense and Return on Investment
Evaluating the financial fundamentals of web application penetration testing can benefit greatly from a cost-benefit analysis. On one hand, we have the cost of the procedure itself, while on the other, the money saved from deflecting a potential attack, avoiding regulatory penalties, and reducing downtime.
More often than not, the potential savings greatly tip the balance in favor of performing the test. It makes financial sense to invest in this preventive measure. However, bear in mind that penetration testing is not a one-time event but a periodically repeated process necessary to stay ahead of constantly emerging threats and adapt to ongoing developments in web applications.
The Power of Expertise
The value of specialist acumen cannot be sidelined when calculating the economics of web application penetration testing. This function demands deep insight into web applications, their potential security flaws, and how they can be exploited. Hiring a skilled penetration tester or a reputable firm specialising in penetration testing is often more usable than developing these skills internally.
In conclusion, investing in web application penetration testing might seem like an upfront expense, but the potential monetary savings coupled with the invaluable insight gained justify this disbursement. It serves as an integral component of an all-rounded data defense plan, assisting businesses in protecting their digital assets, their clientele, and their standing in the market.
Overcoming Resistance to Web Application Penetration Testing
In the realm of digital security, the practice of examining web applications for weaknesses is a crucial method to secure a system's integrity. However, this method often faces opposition due to various reasons such as misunderstandings, apprehensions of disturbances, or economical worries. This article will delve into these issues and suggest ways to address them.
Comprehending the Opposition
The initial phase in handling opposition to examining web applications for weaknesses involves recognising why it exists.
- Miscomprehension: Several companies might not entirely understand the relevance of such cyber prying. They may see it as an unnecessary financial burden or a process that could disturb the workflow.
- Apprehensions about Disturbances: The process of cyber probing is perceived as causing interruptions, more so if not thoroughly planned and carried out. There is concern that it might obstruct business functions or lead to system downtime.
- Economic Worries: The problem of cost comes into play when economically cautious, particularly small- to mid-range companies are considered. The possibility of high costs could deter them from embracing this technique.
Counteracting the Opposition
Once the reasons for opposition are identified, it's time to respond. Here are some methods to neutralise these issues:
- Education: Misunderstandings can be tackled by enlightening stakeholders about the relevance of prying into web applications and the role it plays in safeguarding the organization against digital threats. Using actual examples and experiences to highlight potential hazards and the advantages of cyber prying can be quite effective.
- Organize and Inform: Fears of disruption can be mitigated with proper structuring and communication of the process. Scheduling it during non-busy hours or when it will least affect business operations is advised. The process needs to be communicated to all involved, with a continuity of information flow throughout.
- Showcasing Worth: Addressing economic fears involves showcasing the worth of cyber probing. Illustrating how it can prevent expensive data leaks and save the company's reputation can be a pivotal factor. Offering flexible payment options or finding a service provider that delivers cost-effective solutions could also be considered.
Example: Counteracting Opposition
To clarify these methods, let's go through an example. Suppose Company A, an emerging online retail company, resisted implementing web application penetration testing due to cost worries and disruption fears.
The digital security team at Company A took the following initiatives to counter this opposition:
- They set up multiple sessions to enlighten the management about cyber prying's importance. Instances of similar retail businesses that were hit hard due to cyber-attacks that could have been checked through cyber probing were explained.
- They created a comprehensive plan for the cyber probing process to ensure minimal disruption by scheduling it during off-peak hours. The plan was shared with the management and they were kept updated throughout the process.
- They collaborated with a well-known service provider who offered economical cyber probing services. They also showcased how the cost of cyber prying was substantially less than the possible losses due to a data leak.
As a result of these measures, Company A agreed to have their web applications examined for weaknesses, realising its worth in safeguarding their business.
In summary, mitigating opposition to examining web applications for weaknesses involves tackling concerns through education, meticulous planning and showcasing worth. By doing so, organizations can ascertain they're making the right moves to shield their web applications from potential digital threats.
Employing Ethical Hacking in Penetration Testing
Bolstering Your Site's Protection through Responsible Cyber-security Checks
Amplifying the application of responsible cyber-security checks, performed by endorsed digital experts, allows you to reshape established standards to improve the durability of your web-based tool's defense mechanisms. Such experts strive to pinpoint and swiftly mend system glitches to forge a sturdy guard against online threats. This write-up highlights the integral role of responsible cyber-security checks in network screenings and delves into visionary tactics for their successful implementation.
Exploring the Association between Responsible Cyber-security Checks and Network Screenings
Responsible cyber-security checks and network screenings share a fundamental link, promoting a robust cyber defense, despite the varied tactics implemented. Combined, both methods assist in exposing system inadequacies. Cyber-security investigators apply versatile plans to unmask system shortcomings, while network screenings focus on precise areas to expose embedded hazards.
While safeguarding online tools, cyber-security investigators scrutinize the defensive structure, reveal weak spots, and grasp the tactics of likely hostile intruders. Thus, they can predict probable protection breaches and devise powerful countermeasures.
Organizational Advantages of Merging Responsible Cyber-security Checks with Network Screenings
- Initiative Defence Approach: Applying responsible cyber-security checks allows businesses to instantly spot and rectify security penetrations, thereby diminishing the risk of safety violations and data exposures.
- Regulatory Adherence: Some industries are obliged to comply with particular regulatory guidelines that demand routine network screenings. Incorporating responsible cyber-security checks within these assessments guarantees law abidance, averting unanticipated penalties.
- Boosting Trust and Credibility: A conspicuous dedication to system protection through aligned cyber-security checks cultivates confidence among customers and stakeholders, reinforcing the company's market position and paving the way for business growth.
Merging Responsible Cybersecurity Checks into Network Screenings for Web-Based Tools
Blending responsible cyber checks into web-based tool screenings involves a methodical procedure:
- Obtain Consent: Getting requisite authorizations beforehand is crucial to ensure lawful and ethical conformity before initiating security assessments.
- Define Limits: After obtaining consent, it’s mandatory to settle on the systems to be screened and the exact procedures to be employed.
- Conduct Screenings: Upon approval, cyber-security investigators use a mixture of automated sweeps with manual tactics to unearth system weak spots.
- Examine and Record: Once screenings are complete, results are assessed, and an extensive report is drawn up that lists unearthed weaknesses, potential outcomes, and advised fortifications.
- Put Suggestions Into Practice: After reviewing, the organization requires adjusting its approaches based on the suggested defense improvements.
Essential Tools for Cybersecurity Investigators during Network Screenings
Cybersecurity investigators exploit a variety of tools in online tool screenings:
- PacketSpy: An online protocol inspection tool that enables investigators to assess traffic routes to identify potential security frailties.
- BreachFramework: A multifaceted tool with a comprehensive database for tracking hostile activities.
- SourceIdentifier: A network detection tool that assists in identifying hosts and services.
- FlawScanner: Specifically crafted for security assessments, it is effective in detecting weaknesses in online tools.
Engaging cyber-security investigators for online tool security assessments equips organizations with solid and proactive defenses against digital transgressions. This forward-thinking approach offers businesses a strategic edge against possible threats, promising the secure functioning of their networks.
Subscribe for the latest news
















