Top 18 Critical Security Controls: CIS Solution
Today's IT security experts face a tremendous challenge in keeping up with the ever-evolving nature of threats. Technology is increasingly beneficial for companies, especially as more employees opt to conduct their duties outside of a traditional office setting, posing new risks. The CIS 18 CSC architecture is currently in widespread usage.

What is the Center for Internet Security?
The CIS is a nonprofit organization that creates its own Configuration Policy Benchmarks (CPB). Organizations can enhance their cybersecurity and compliance strategies and posture by following the CPB, which are essentially guidelines. The purpose of this project is to establish industry-standard security configuration baselines for widely adopted IT and security products. Additionally, it publishes a set of protocols known as CIS Controls, which are studied and updated on occasion via an ad hoc community procedure.
Objectives Of Security Controls
The controls are designed to enhance cybersecurity and assist businesses in managing their IT operations with as little risk as possible, as one might think from the name. Concerns like hacking, internet dangers, and data loss are mitigated by CIS security controls. In addition, it is an advice on best practices for both compliance and cyber security.
More precisely, the panels rationalize the employment of privacy processes for businesses and provide a robust framework to adhere to. To ensure maximum security against the most prevalent attacks, businesses need just apply all eighteen controls.
However, it can be intimidating for small firms in particular to figure all of this out on their own. Because of this, the CIS 18 controls’ recommendations are helpful because they provide a gradual implementation of the restrictions. With so many options available, every company, no matter how big or little, may take steps to improve their privacy.
To emphasize, the CIS controls are geared towards defending the internal security systems of a company rather than providing instruction on how to fend off specific, inclusive cyber-attacks. Therefore, the CIS restrictions are not 100% effective and comprehensive. Rather, they should be seen as a jumping off point for further cyber security development.
CIS Control V7 Vs V8
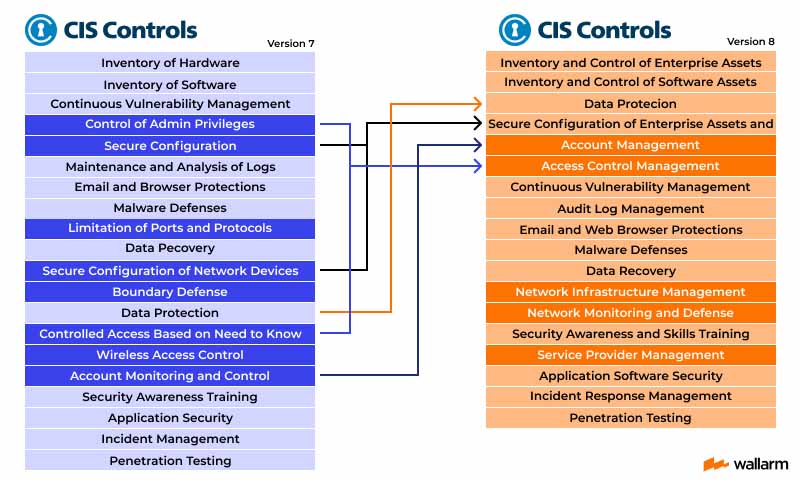
They are a set of finest practices for cybersecurity created by the Center for Internet Security (CIS). These controls Version 7 was released in 2018 and updated in 2020, while CIS Controls Version 8 was released in 2021.
The main differences between the two versions include:
- Version 8 has fewer controls than Version 7, but they are more focused and prioritized.
- Version 8 emphasizes the need for continuous cybersecurity, including the ability to adapt to evolving threats and technologies.
- Version 8 introduces new controls to address emerging security issues such as the use of cloud computing and the Internet of Things (IoT).
- Version 8 provides a more structured approach to risk management, taking into account the organization's goals, assets, and threat landscape.
Organizations of various sizes and types can be beneficial from the instructions provided by both versions 7 and 8. Choosing the ideal one depends on your business's requirements and risk forbearance.
CIS Critical Security Controls
Forget about who is in charge of policing your devices; CIS V8 expands the focus to include what they're doing. In today's permeable and interconnected digital world, fences, gadgets, and separate security mechanisms have less value. These considerations were taken into account when forming CIS V8's fundamental authorities.
CIS Control 1: Inventory and Control of Enterprise Assets
Active administration(commodities, tracking, and correction) of all company goods connected to the framework locally, privately, remotely, and in cloud domains is necessary for authentic knowledge of the full scope of corporate acquisitions that must be observed and protected. This will help search for acquisitions that are either undesirable or mismanaged and need to be fixed. This is an added feature.

Protective Measures
- Establish a procedure to deal with illegal purchases on a fairly regular basis. The company can quarantine, remove, or block such buys from remotely connecting to the network.
- Identify the firm’s network purchases using an active discovery tool. Set up daily or more frequent execution.
- Utilize a passive finding technique to detect the industry’s network-related items. At least every week, or more frequently, review and use scans to update the enterprise's inventory.
CIS Control 2: Inventory and Control of Software Assets
Vigorously manage (products, track, and correct) all software (operating systems and apps) on the network so that only authorized software can be installed and can execute, and so that unauthorized and unmanaged software can be found and prevented from installation or execution. This will ensure that only authorized software is installed and can execute.
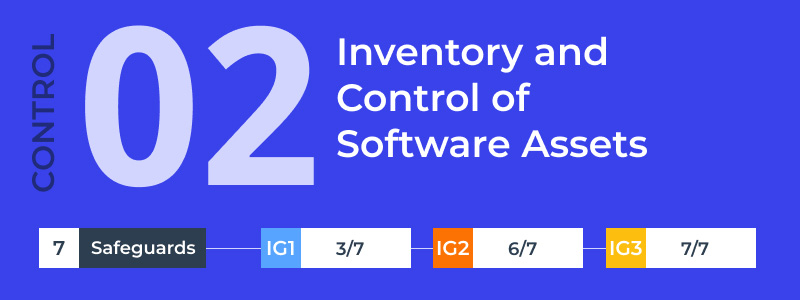
Protective Measures
- Create and regularly update a complete list of the enterprise's licensed software installations. Include the Uniform Resource Locator (URL), app store(s), version(s), deployment technique, and decommission date where applicable in the software inventory, as well as the title, publisher, initial install/use date, and business objective for each entry. The software stock should be checked and updated at least twice a year.
- It is imperative that any unapproved software being used on company property be either withdrawn or granted a written exemption. Either once a month or more often if necessary.
- When possible, businesses should make use of software inventory solutions to streamline the tracking of all their software.
CIS Control 3: Data Protection
Develop procedures and technical controls in order to recognize and classify data, as well as safely manage it, store it, and eventually dispose of it.

Protective Measures
- Create a system for managing your data and keep it updated. Take into account enterprise-wide standards for information vulnerability and withholding when making decisions about data ownership, processing, storage, and deletion. Once a year, or if a major change in the company could affect this protection, examine and revamp the documentation.
- Create and update all company’s data inventory using the company's internal data management system. Keep at least some private info in stock. The inventory should be reviewed and updated at least once a year, with special attention paid to any sensitive information.
- Set up information permit management lists according to what each user absolutely must see. Utilize data ACLs, or permission settings, for your local and cloud-based storage, databases, and software.
CIS Control 4: Secure Configuration of Enterprise Assets and Software
Corporation’s products (products aimed towards the final consumer; this includes handheld and smartphones; network devices; non-computing/IoT policies; and servers) and their corresponding software must be shaped securely from the start and kept that way (operational systems and programs).
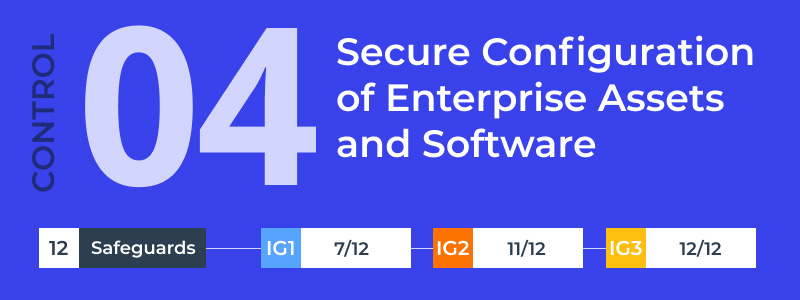
Protective Measures
- Securely configure enterprise resources and freeware. Update documentation annually or when substantial corporate changes potentially affect this safeguard.
- Configure network devices in a secure manner. Documentation should be updated on a yearly basis or if there are significant changes to the company that could potentially affect protection.
- Locking down enterprise assets after a predetermined period of inactivity is recommended. The maximum allowed boot time for general-purpose operating systems is 15 minutes. The maximum length of time for mobile end-user devices is two minutes.
CIS Control 5: Account Management
Make use of systems and resources to create and control access permissions for all types of user accounts, including administrative and service accounts, to all hardware and software used by the business.

Protective Measures
- Compile a complete and up-to-date list of all company accounts. User accounts and admin accounts alike must be accounted for in the inventory. The inventory must contain the individual's name, username, start and end dates, and department at a minimum. On a quarterly basis, at the very least, but preferably more regularly, check to make sure all current accounts have been properly approved.
- Protect all company data with separate passwords. The recommended minimum length of a password for an account protected by multi-factor authentication is 14 characters, while the recommended minimum length for an account not threatened by multi-factor authentication is 8 characters.
- Remove or disable inactive accounts after 45 days, if possible.
CIS Control 6: Access Control Management
Create user, administrator, and service accounts for enterprise assets and software, as well as manage their permissions and access using the appropriate processes and tools.
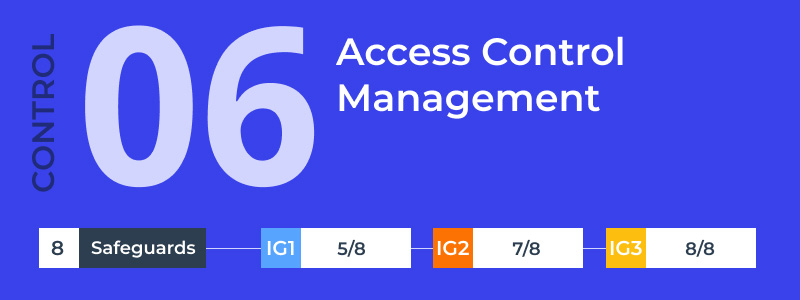
Protective Measures
- Create and adhere to a procedure, ideally automated, for providing users with access to business resources upon their onboarding, rights assignment, or role change.
- When an employee leaves, their access privileges are revoked, or their job changes, the company must have a procedure in place to ensure that their account is instantly disabled. Ideally, this procedure would be automated. In order to keep audit logs, it may be necessary to temporarily disable accounts instead of removing them.
- Incorporate MFA enforcement into all publicly accessible enterprise and third-party apps. This Safeguard may be implemented satisfactorily with the use of a directory service or SSO provider to enforce MFA.
CIS Control 7: Continuous Vulnerability Management
Establish a system to keep tabs on the security of all enterprise assets within the infrastructure, so that flaws can be fixed and the attack window may be reduced. Maintain vigilance over industry and government sources for fresh data on threats and vulnerabilities.

Protective Measures
- Create and uphold a well-documented procedure for managing corporate assets' vulnerabilities. Once a year, or if there is a major change in the company that could affect this Safeguard, review and update the documentation.
- A risk-based remediation strategy should be established and maintained, with reviews occurring regularly or more frequently.
- Monthly or more frequent operating system updates should be implemented on enterprise assets through automated patch management.
CIS Control 8: Audit Log Management
Audit logs of events that can be used to detect, comprehend, or recover from an attack should be collected, alerted on, reviewed, and kept for as long as necessary.

Protective Measures
- Create and keep up with a system for managing audit logs that specifies the logging needs of your business. Take care of the bare minimum and deal with audit log collection, review, and storage for company assets. Once a year, or if there is a major change in the company that could affect this Safeguard, review and update the documentation.
- Acquire auditing records. Check that all enterprise assets are logged in accordance with the organization's audit log management methodology.
- Maintain sufficient storage at logging locations to meet enterprise audit log management requirements.
CIS Control 9: Email and Web Browser Protections
Protecting against and detecting threats via email and the web is crucial because these channels allow attackers to directly communicate with targets, changing their behavior.
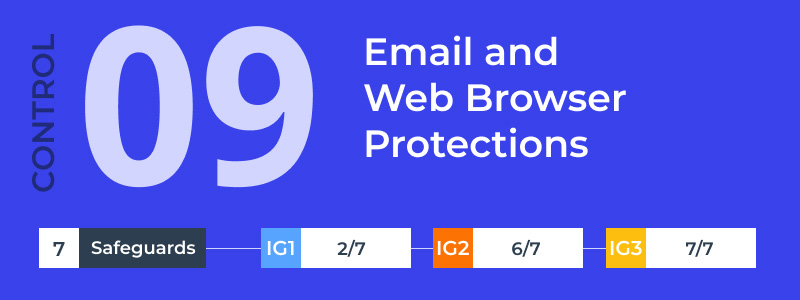
Protective Measures
- Be sure that only the most up-to-date versions of the browsers and email clients that the vendor officially supports are allowed to run within the company's infrastructure.
- Block access to hazardous websites by using a DNS filtering solution across the whole company network.
- Network administrators should implement and regularly update URL filters to prevent company assets from connecting to malware or otherwise unapproved websites. Category-based filtering, reputation-based filtering, and the use of block lists are all examples of practical applications. Apply security measures to everything in the company.
CIS Control 10: Malware Defenses
Keep harmful software from being installed on company computers and from running unchecked.

Protective Measures
- Install and regularly update anti malware protection on all company computers.
- Set up all company resources to get automatic updates to their anti-malware signature files.
- Turn off the playback and execution of removable media automatically.
CIS Control 11: Data Recovery
Build and keep up data recovery procedures that can reliably return in-scope enterprise assets to their safe, pre-attack state.
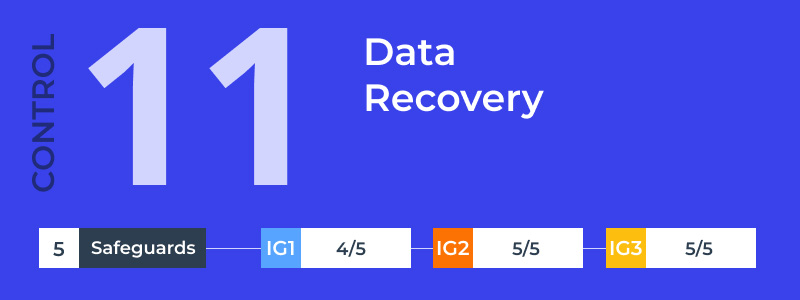
Protective Measures
- Initiate and maintain a data recovery procedure. In doing so, you should think about issues like the backup data's safety, the recovery's priority, and the extent of the data recovery actions. Once a year, or if there is a major change in the company that could affect this Safeguard, review and update the documentation.
- Automate backups of enterprise data that matters. Back up your data at least once every week, and preferably more often if it's especially important.
- Restored information should have the same level of security as the original. Make use of encrypted references or partition your data, depending on your needs.
CIS Control 12: Network Infrastructure Management
Set up and deploy network devices while actively managing (monitoring, reporting, and fixing) them to stop hackers from taking advantage of unprotected network services and access points.

Protective Measures
- Maintain a cutting-edge infrastructure in your network. Using the most recent stable software release and/or the most recent network-as-a-service (NaaS) offerings are two examples of such implementations. Verifying continued software support requires a monthly (or more regular) review of software versions.
- Create and keep up a safe system for your network. The principles of segmentation, least privilege, and availability are foundational to any secure network design.
- Supervise the network in a safe manner. Some examples of how this is put into practice include using encrypted transport protocols like SSH and HTTPS, and using version control for the underlying infrastructure.
CIS Control 13: Network Monitoring and Defense
Run procedures and software to set up and maintain a system of complete network monitoring and defense against security threats throughout the enterprise's network architecture and user population.

Protective Measures
- Reduce administrative overhead by consolidating industry-wide protection event attentiveness, log correlation, and analysis. The adoption of a SIEM, with its vendor-defined event, is essential for effectively implementing best practices. In addition, this Safeguard is met by a log analytics platform that features security-related correlation warnings.
- The best action is to deploy an endpoint breach monitoring system across an organization's resources.
- To protect company resources, install a system that can identify malicious network activity. NIDS and similar cloud service provider (CSP) services are two common examples of such implementations.
CIS Control 14: Security Awareness and Skills Training
Create and keep up safety awareness events to help employees become more security-minded and equipped, lowering the company's exposure to cyber threats.

Protective Measures
- Put in place and continually update a security education program. A security awareness program's goal is to train an organization's staff to handle its assets and data safely. Provide training to new hires and on an annual basis thereafter. It is recommended to review and update content annually, or whenever there are substantial enterprise changes that could affect this Safeguard.
- Employees should be taught to spot social engineering techniques like phishing, pretexting, and tailgating to avoid falling victim.
- Educate your staff on the best practices for authentication. Multi-factor authentication, password creation, and credential management are all good examples of such topics.
CIS Control 15: Service Provider Management
Design a method for assessing the security measures taken by third-party service providers handling sensitive information or managing mission-critical IT infrastructure on behalf of an organization.

Protective Measures
- Get a list of service providers together and keep it updated. Every service provider should be listed in the inventory, categorized, and assigned to a point of contact inside the company. The inventory should be reviewed and updated at least once a year, or if there are substantial changes to the business that potentially affect this Safeguard.
- Create and uphold a policy for managing your service providers. Make that the policy takes into account the identification, categorization, inventory, evaluation, monitoring, and eventual deactivation of service providers. At least once a year, or whenever there is a major change in the company that could affect this Safeguard, you should review and update the policy.
- Put service providers in a category. Data sensitivity, data volume, availability needs, applicable legislation, inherent risk, and mitigated risk may all play a role in the classification process. Classifications should be reviewed and updated once a year, or if there is a major change in the company that could affect this Safeguard.
CIS Control 16: Application Software Security
Take charge of the whole security life cycle of any software your company uses, whether it was built in-house, hosted internally, or was purchased externally, to ensure that any vulnerabilities are addressed before they can cause any damage.

Protective Measures
- Make sure your application development process is secure and keeps it that way. Take care of things like safe application design standards, secure coding techniques, developer training, vulnerability management, third-party code security, and application security testing procedures. Once a year, or if there is a major change in the company that could affect this Safeguard, review and update the documentation.
- Locate the underlying causes of security flaws. Root cause analysis is the process of digging deeper into the causes of vulnerabilities in order to help development teams solve more than just the most recent problems as they appear in the code.
- Make sure any external programs you use are up-to-date and reliable. When possible, go with tried-and-true frameworks and libraries that have already been shown to offer sufficient protection. Get these from reliable places, or check the program for security flaws, before you use it.
CIS Control 17: Incident Response Management
Prepare for, detect, and respond swiftly to an attack by establishing a program to build and maintain an incident response capacity (including policies, plans, processes, defined roles, training, and communications).

Protective Measures
- Identify a primary contact and a secondary contact to oversee the business' incident response. Management staff, which may include in-house workers, external suppliers, or a combination of the two, is responsible for coordinating and documenting incident reaction and recovery operations. Any work performed by an outside vendor should have at least one internal point of contact. Reevaluate once a year or if there is a major change in the business that could affect this Safeguard.
- Create and update a procedure for handling incidents that includes protocols for handling roles and responsibilities, meeting regulatory obligations, and sharing information. At least once a year, or whenever there is a major change in the business that could affect this Safeguard, do a review.
- Investigate the situation after it has occurred. Through the identification of lessons learned and subsequent action, post-incident evaluations can reduce the likelihood of a repeat of the occurrence.
CIS Control 18: Penetration Testing
By replicating an attacker's aims and behaviors and finding and exploiting susceptibilities in controls (people, procedures, and technology), penetration testing puts an organization's assets to the test for their efficacy and resilience.
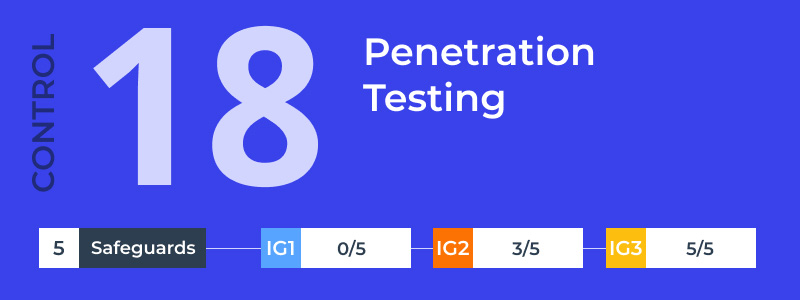
Protective Measures
- Put in place and regularly apprise an infiltration testing plan that takes into account your company's size, complexity, and level of development. Scope, which includes things like networks, web applications, APIs, hosted services, and even physical premise controls; frequency; limitations, like acceptable hours and excluded attack types; point of contact information; remediation, like how findings will be routed internally; and retrospective requirements are all features of a well-made penetration testing program.
- Apply the company's remediation policy to the findings of the penetration test, taking into account the severity of the issues and the order in which they should be fixed.
- When steering a penetration test, it is significant to validate the security measures taken following the test. Change detection rules and capabilities as desired to categorize testing procedures.
What are Implementation Groups?
The Center for Internet Security Critical Security Controls are widely acknowledged as an efficient, unified, and straightforward method of managing an organization's security improvement program because they combine expert insight into risks, business technology, and defensive solutions. These observations lead to believe, however, that businesses of all sizes and levels of complexity can always use additional assistance in getting off the ground and determining where to devote the majority of their efforts.
In order to achieve this, Implementation Groups (IGs) were formed. Implementation of the CIS Controls should be prioritized in accordance with IGs. IGs are split into three categories to better serve businesses of varying sizes. They take into account the enterprise's risk tolerance and the assets it possesses in order to carry out the CIS Controls. Each IG determines its own unique set of Safeguards (formerly CIS SubControls) to follow. CIS Controls v8 includes 153 Security Measures.
It is recommended that all businesses begin with IG1. IG1 provides expressive security benefits using commonly reachable technology and processes, while also laying the groundwork for more individualized and nuanced responses as necessary. It is expanded upon IG1 by determining a second set of Safeguards to help mitigate the risks faced by businesses with more personnel, knowledge, and capital. This is the IG2. The remaining Safeguards are grouped together in IG3, which is the final phase.
Using these IGs is a straightforward and easy approach for industries of all sizes to distillate their limited security resources while still benefiting from the CIS Controls program, community, and supplementary tools and working aids.
- Implementation Group 1
Every business should follow IGI's least standard of cyber hygiene, which it defines with 56 different precautions. Typically, IG1 organizations fall into the category of small to medium in size, have modest budgets for cybersecurity and IT, and handle facts with a low level of responsiveness.
- Implementation Group 2
IG2 is designed for organizations that have a moderate amount of sensitive data and more available resources. Its 74 protections expand on the 56 protections of IG1, making it easier for security teams to handle complex situations. When it comes to installing and configuring certain safeguards, only those with extensive technical knowledge and access to enterprise-level resources should be trusted. IG2 businesses can afford to hire staff specifically tasked with keeping an eye on, administering, and protecting their company's IT infrastructure and data. If data breaches occur, the public's trust in them will plummet because of the sensitive information they store and process about businesses and customers.
- Implementation Group 3
To be eligible for IG3, a company must be well-established and maintain extremely private information on both its employees and its customers. It has 23 extra safety measures. Compared to their IG2 peers, IG3 companies tend to be quite sizable. Consequently, they frequently hire information technology (IT) specialists skilled in many facets of cybersecurity, such as penetration testing, risk management, and application development. These businesses need the ability to avoid and mitigate complex assaults, as well as lessen the impact of zero-day exploits, because their IT assets store sensitive data and perform sensitive operations that are subject to compliance and regulatory supervision.
CIS Critical Security Controls and Other Standards
Organizations required to comply with regulations such as NIST 800-53, PCI DSS, FISMA, and HIPAA can employ the Center for Internet Security Controls to help them do so because they are compatible with and/or directly map to these and other compliance and security standards. Another powerful tool often used to improve an organization's security posture is the NIST Cybersecurity Framework, which uses the CIS CSC as the foundation for a number of its suggested best practices.
The CIS Critical Security Controls are a great starting point for enterprises wishing to strengthen their security posture and harden their defenses against the attack vectors they are most likely to encounter.
Subscribe for the latest news

















