API Gateway: The Strategic Control Plane for Modern Architecture
In the era of microservices, APIs are the backbone of digital business. But as ecosystems scale, managing and securing thousands of endpoints becomes a critical challenge.
An API Gateway acts as the strategic control plane for this traffic. No longer just a "smart proxy," it is an essential layer for orchestration and defense. In this guide, we provide a clear API Gateway definition, explore must-have API Gateway features, and share real-world API Gateway examples. Most importantly, we examine why robust API Gateway security is your first line of defense in 2025.

API Gateway Definition: More Than a Reverse Proxy
In 2026, an API Gateway is no longer just a "front door." It is the central nervous system of a microservices ecosystem. While a reverse proxy simply forwards requests, a modern Gateway manages the entire lifecycle of a request, treating APIs as products rather than just endpoints.
The Concept at a Glance: The "Concierge" for Your Microservices
Gateway API’s idea is centered around a rule-oriented resource standard and enables multiple non-coordinating services to share a centralized communication ecosystem. It highlights the below-mentioned resource types:
- GatewayClass demonstrates the cluster’s load balancer.
- Gateway states how and where a load balancer lets the traffic communicate.
- HTTPRoute elucidates the protocol rules for API call routing via the internet.
2025 Market Insights:
- Growth: The API Management market is projected to hit $8.86 billion in 2025, with a CAGR of 16.8% through 2030 (Source: Mordor Intelligence).
- Adoption: 82% of organizations have now shifted to an "API-first" strategy, making the Gateway a non-negotiable infrastructure component (Source: Postman 2025 State of the API).
Why Use an API Gateway?
For a novice, it may seem like an ideal means to supervise API calls properly. But, it’s way more than this. Let’s explain API Gateway’s functions crisply below:
- Its features like authentication and rate-limiting help developers examine API abuse and overuse.
- Its inclusion permits developers to find out how APIs are used in different scenarios.
- For monetized solutions, it constructs a seamless relationship between backend processes and billing systems.
- It can concoct the specific requests for assorted applications if microservices deployment is concerned.
- It assists in obtaining all the needed resources for API maintenance, upgrades, and modernization, even when updates are happening.
- Multiple API handling is easy with API gateway as it will observe everything occurring to API.
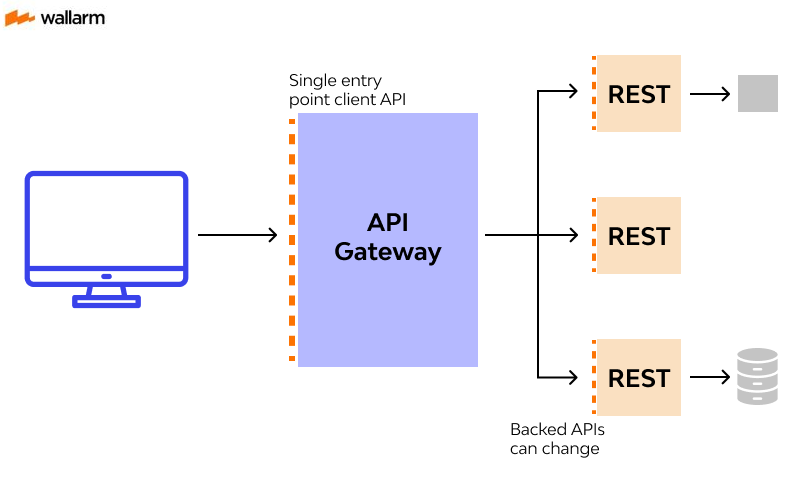
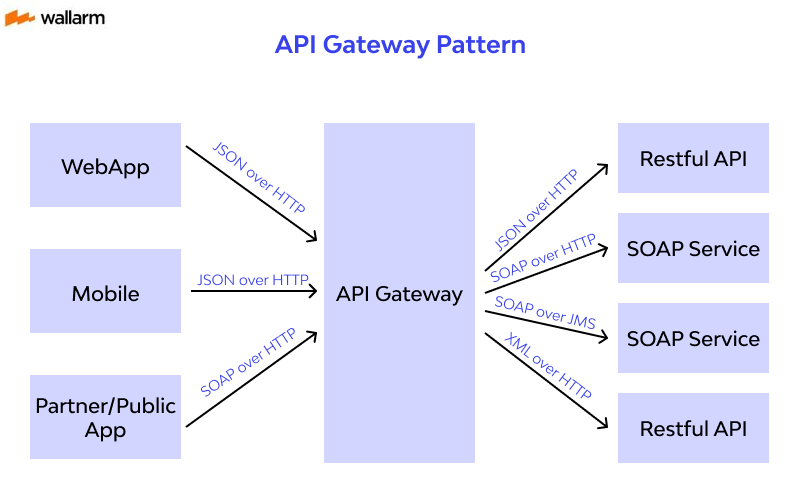
How API Gateway Work?
- Application testing and usage involve tons of data exchange operations. Such type of communication requires advanced arrangements. To sort the issue, the API gateway turns into a central platform for receiving assorted API requests.
- During the process, several API calls are clubbed, authenticated, and redirected to suitable APIs.
- In the microservices ecosystem, it formulates an opportune entrance for requests by specific microservices. It also establishes accessibility and conducting criteria.
- Besides, API gateways handle employment like service discovery, API protocol translation, business logic processing, cache management, network traffic assistance, and API monitoring.
Essential API Gateway Features for 2026
To compete with enterprise solutions like Kong or Azure, a gateway must support these core API Gateway features:
- Authentication & Authorization: Support for OAuth2, OIDC, and JWT validation.
- Rate Limiting & Quota Management: Preventing service exhaustion and enabling tiered monetization.
- Observability & Tracing: Native integration with OpenTelemetry for end-to-end distributed tracing.
- Caching: Reducing latency by serving repetitive GET requests from the edge.
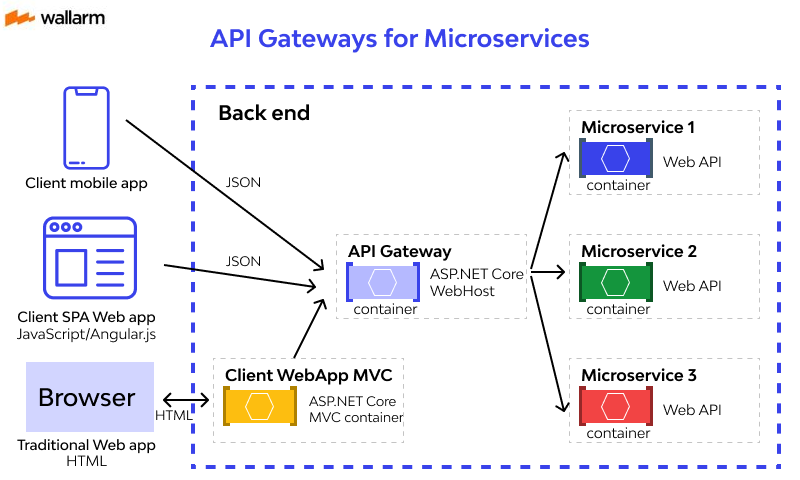
What is API Gateway for Microservices Architectures
A huge number of smaller components constitutes microservices. This approach helps developers enhance the user experience. However, not without an API gateway. After all, it works as a translator for these components, ensuring swift, less tedious, and error-free API implementation.
A typical gateway can process maximum client requests, keep all of them at a centralized place, and combine them. Doing so cuts down the time taken in the client-application communication. So, the cost of operations reduces too.
Cruciality of Gateway in Overall API Management
The Gateway is the "muscle," but it needs a "brain" (Management Layer).
- Monetization: 65% of organizations now generate direct revenue through APIs (Source: Postman 2025).
- Governance: Centralized policy management ensures that a security update in one place protects thousands of endpoints instantly.
Benefits and Real-World API Gateway Examples
Putting a gateway into place is good for end-user, applications, and API or solution developers as everything from API development to controlled operational cost is achieved in one shot.
- Effective API development
API gateway grants developers an ability to execute various versions of a particular API consequently and test, iterate and update APIs in the least possible efforts. API development becomes quick yet equally effective. As API gateway charges for only the API calls made and data transfer, there is no minimum commitment to fulfill.
- Productivity at any scale
API gateway helps developers operate with the least latency, helping them deliver a better experience for the end-users. Additionally, it allows traffic throttle and API request authorization. These two features assist the backend API development team to deal with any unnoticed/uninvited traffic spikes and ensure continual API performance.
- Easy monitoring
API gateway brings everything to a consolidated point and grants unified visibility to data like API calls information, error rates, and details related to latency. Having instant access to all these metrics allows developers to keep track of API performance at every stage and spot any hidden caveats.
- Reducing costs at any scale
API gateway comes with multiple subscriptions and grants freedom to choose the package as per the API requests made. In general, one can process million API requests at a mere cost of $ 0.90. With such flexible pricing, one can keep the API development costing under control.
Service Mesh vs. API Gateway
Unlike an API-specific Gateway which promotes centralization of the control, a service-mesh uses diverse microservices to perform distinct functions in an application. However, if you use an API gateway for mediating the exchange among microservices in the service-mesh, your digital solution will have a higher level of security and operation-execution speed.
Comparison table
API Gateway vs Service Mesh Comparison Table
| Differentiating Factor | API Gateway | Service-Mesh |
|---|---|---|
| Aim | Routing the organizational, outsider and database calls or requests securely. | Boosting the platform-independence within an organizational network using microservices. |
| Functioning | Can interact with the outsider network and forward the requests to & fro the organizational network. | Acts within the organizational limits or a network. |
| Responsibility | Management & safety of the network’s APIs. | To boost a system/network’s performance and portability. APIs hide service meshes from outsiders and secure them. |
| Security Method | Allows the use of automation and policies | Requires manual implementation of security strategy. |
Service Mesh vs. Load Balancer
As you must have understood by now, an API gateway is the mediator for various services. It takes the network calls to and fro, ensuring that interaction remains secure and fast.
On the contrary, a load balancer has the work of diverting a server’s traffic but without any hard and fast rules. So, you can think of an API gateway as an authentication-based network traffic-balancer.
Comparison table
API Gateway vs Load Balancer Comparison Table
| Differentiating Factor | API Gateway | Load-balancer |
|---|---|---|
| Use | Routing the inner and outer network traffic, alongside the database request, securely in a system/network. | Reducing the load for a server by diverting the traffic. Its work is to pace up the server’s working speed. |
| Request Handling | It handles a request using an authentication method. Only the authorized users/requests can enter the network. | It checks the most suitable node for traffic diversion when a request arrives. This decision may be based on the location of the requesting user or on the fact that which resource/server is free. |
| Security | It may have automated or manually-implemented security controls to decide who should be authorized and who should not be. | There may be explicit security implementations but the load balancers itself do not take care of security. |
API Gateway Security: The First Line of Defense
If you read carefully yet, it must be clear that API gateway is not spared by online vulnerabilities and needs adequate API security practices to keep gateway issues at bay. The first step to being taken towards this direction is to ensure that HTTP is used for all sorts of communication. There should be no exception in this case.
Implementing a couple of user authentication methods keeps unwanted access to API calls. Both these practices keep duplication far away and maintain consistency in the application development.
Threats like DDoS, SQL injection, and brute force demand an added defense line to safeguard the API gateway. For instance, SQL injection attacks can be prevented by using user validation at both the server and client end before data is shared.
To prevent malicious code from attacking the gateway, it’s wise to do the regress API getaway check on the server end. It’s obvious to receive frequent API calls and rate-limiting, throttling, and request size ensures that API requests are managed at every stage.
Knowing the API data accessed is crucial as it allows developers to figure out the API utility. One of the most viable ways to get this done is to log the API gateway. It makes auditing the API calls and answers simpler.
Other than the above-mentioned standard procedures of gateway safety, here are a few more approaches to adopt:
- Define the usability and accessibility of each API gateway at the time of development only.
- Make sure the gateway is not exposing too much information and access filters are defined.
- Try applying a transformation reaction to the gateway while using the HTTP headers for RESTful API. This leads to an automatic share of only needed data.
- For an application with many use cases like IoT devices, mobile implementation, website, and integration, create a dedicated API gateway for each type. Don’t bring internal use endpoints into the public’s eye.
- Gateways for internal apps or networks should be accessed over a private network to prevent unwanted data access.
Lastly, track APIs at every stage. For effective API security, remove APIs or components that are no longer needed, outdated, and not defined by security standards. Continuing with such poor quality APIs will only exert more burden on you and can create a hole in the security approach.
Future Trends: AI and Edge Gateways
- AI-Native Security: Gateways are beginning to use ML to detect "behavioral anomalies" rather than just static rules.
- Edge Computing: Moving gateway logic to the edge (Cloudflare Workers, Fastly) to reduce latency to <10ms globally.
- Post-Quantum Cryptography: Preparing for the next generation of encryption standards within the gateway layer.
FAQ
An API gateway is a server that acts as an intermediary between a client and a backend service or application. It provides a set of features such as routing, authentication, and rate limiting.
API gateways can secure APIs by implementing security measures such as SSL/TLS encryption, OAuth 2.0 authentication, and API key management.
Benefits of using an API gateway include improved security, increased scalability, and a simplified architecture. It can also reduce latency by caching often-requested data.
A: Some of the most popular API gateway services are Amazon API Gateway, Google Cloud Endpoints, Kong, Apigee, Mulesoft and Azure API Management. These services provide a range of features such as authentication, rate limiting, caching, and analytics to help manage and secure APIs. Choosing the right API gateway service will depend on your specific business needs and requirements.
References
Subscribe for the latest news

















