What is a Firewall and How does it Work?
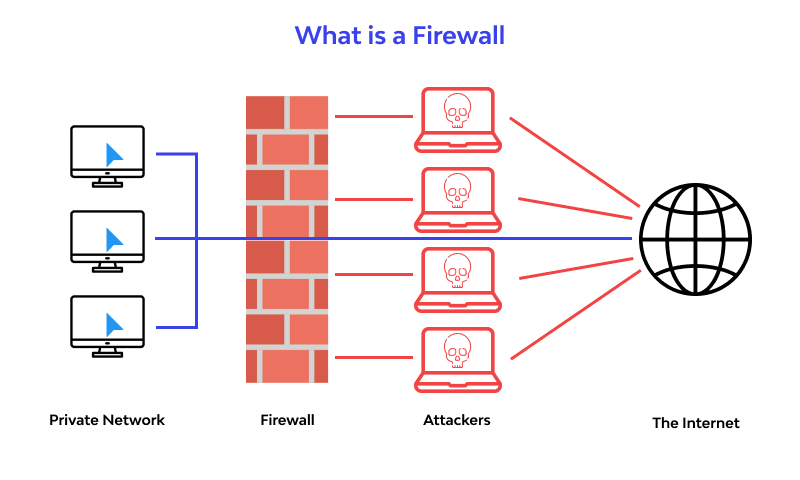
In the tech world, a firewall is a wellbeing network framework that screens and controls moving ever closer affiliation traffic dependent upon destined security rules. A firewall ordinarily draws up a line between a confided in affiliation and an untrusted affiliation, like the Internet.

What is a Firewall and How Does it Work?
In the modern cybersecurity landscape, a firewall is no longer just a "digital wall" but an intelligent gateway. As of 2025, the complexity of network threats has escalated, with the average cost of a data breach reaching $4.88 million (IBM Cost of a Data Breach Report 2024). A firewall serves as the first line of defense, monitoring and filtering every piece of data attempting to enter or leave your network.
Firewall Definition: What Is a Network Firewall?
A network firewall is a security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Its primary goal is to establish a barrier between a trusted internal network and untrusted external networks, such as the Internet.
In 2025, the definition has expanded to include Cloud-Native Firewalls and Hybrid Mesh Firewalls, which protect distributed environments where traditional perimeters no longer exist. The global firewall market is currently valued at over $15 billion, reflecting its status as a non-negotiable component of enterprise security.
How Firewalls Safeguard Your Network
Network security systems, often placed at pivotal gateways or within data centers, act as the first line of defense by filtering out potentially dangerous transmissions while ensuring legitimate data is allowed through. Stationed at these essential junctions, they evaluate and verify each unit of data in real time, measuring it against established safety benchmarks to detect potential hazards. Any data failing these checks is blocked from moving further.
These solutions oversee both incoming and outgoing data flows, safeguarding against:
- External threats: These encompass cyber risks such as malware, harmful software, ransomware, and DoS assaults. Security gateways oversee incoming data streams, blocking unauthorized access and diminishing the risk of network intrusions.
- Internal risks: Firewalls further secure the network by guarding against internal threats such as compromised employees or harmful software. They oversee the data exiting the network, enabling the detection of irregular behaviors, blocking improper data movements, and minimizing the risk of internal security breaches or information disclosures.
- Protocol Exploits: They can be configured to intercept traffic leveraging vulnerabilities in particular communication methods, strengthening defenses against advanced infiltration attempts.
- Traffic irregularities: Sophisticated firewalls are capable of identifying unusual traffic patterns, alerting system administrators to abnormal surges or atypical access attempts, which could signal an ongoing attack or security breach.
How does a firewall work?
A firewall develops a limit between an external association and the association it watches. It is installed inline across an association affiliation and evaluates all groups entering and leaving the observed organization. As it evaluates, it uses a lot of pre-planned rules to perceive innocuous and malevolent bundles.
The term 'packs' suggests pieces of data that are coordinated for web move. Packs contain the real data, similarly as information about the data, for instance, where it came from. Firewalls can use this pack information to choose if a given bundle follows the standard set. If it doesn't, the package will be expelled from entering the watched network.
Rule sets can be established on a couple of things showed by pack data, including:
- Their source.
- Their objective.
- Their substance.
These credits may be tended to unmistakably at different levels of the association. As a package goes through the association, it is reformatted a couple of times to tell the show where to send it. Different sorts of firewalls exist to examine packs at different association levels.
Below is a closer look at how these security solutions function.
- Observing Data Transfers
Security gateways operate continuously to oversee all information entering and leaving the network. As data is exchanged in small segments called packets, the firewall systematically evaluates each one against a set of predefined safety standards.
- Fundamental Packet Screening
At a basic level, filtering involves assessing the origin and destination of each packet. Any packet failing to align with established security guidelines is immediately blocked from traversing the network boundary.
- Tracking Ongoing Connections
Modern firewall solutions move beyond simple packet checks by monitoring the status of active data exchanges. This added context helps distinguish legitimate packets involved in a current session from those that may signal malicious activity.
- Functioning as an Intermediary
In certain scenarios, the firewall acts as a go-between. When a user attempts to access a resource, such as a webpage, the firewall initiates the request on their behalf. After receiving a response, it evaluates the content’s safety before allowing it into the network. This measure protects the network’s internal structure from outside scrutiny.
- Elevated Packet Examination
Deep Packet Inspection (DPI) employs an extensive method to examine every component of a data packet, assessing the entire payload instead of limiting the focus to just the header information. Through this comprehensive inspection, advanced threats like malicious software or unauthorized intrusions can be uncovered where simpler methods might fail.
- Filtering Traffic by Application
Contemporary firewalls can also regulate data flow based on the specific software generating it, rather than relying solely on a packet’s source or destination. This feature enables the firewall to permit trusted programs, such as email clients, while blocking potentially harmful ones, like certain file-sharing tools.
- Spotting Irregular Network Conduct
Some high-level firewalls employ behavior analysis to detect unusual traffic trends that could indicate a security breach. By comparing current network activity with established norms, they can identify and counter suspicious behavior, possibly thwarting a cyberattack before it inflicts damage.
Why Firewalls are Essential: Importance and Significance
Firewalls form a crucial layer of defense by allowing only legitimate data to pass through. They stand as a primary safeguard against unauthorized intrusions, online assaults, and data compromises, ensuring that sensitive information remains protected and reliable.
Beyond simple blocking, firewalls provide critical business resilience:
- Preventing Ransomware: Firewalls block the Command-and-Control (C2) communication that ransomware needs to encrypt your files.
- Regulatory Compliance: Frameworks like PCI DSS 4.0 and GDPR mandate firewall protection for sensitive data.
- Visibility: Modern firewalls provide logs that give security teams a "bird's-eye view" of network activity, essential for forensic analysis after an incident.
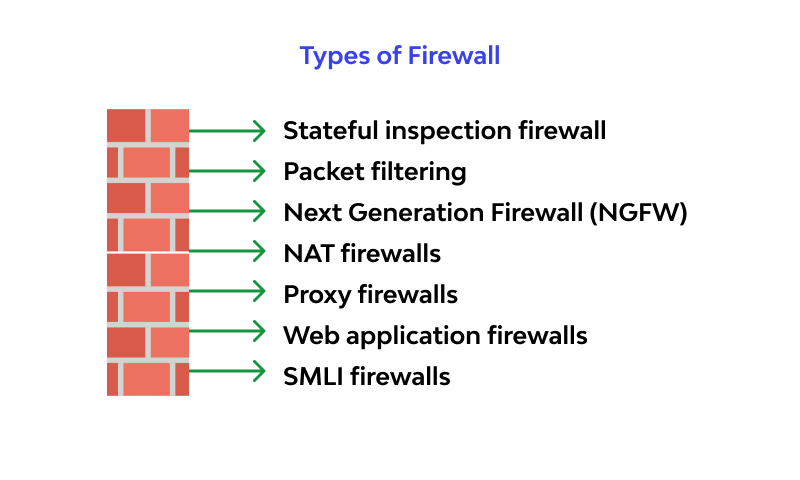
Essential Types of Firewalls
Stateful examination firewall
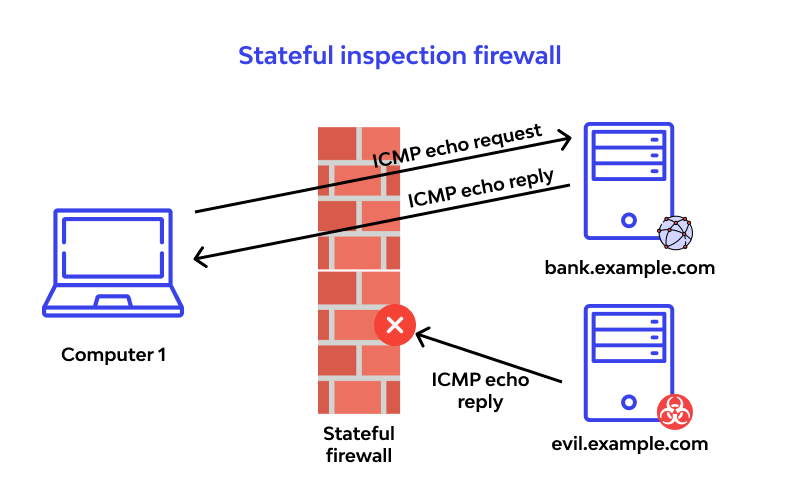
Stateful assessment firewalls – in any case called dynamic bundle sifting firewalls – screen correspondence groups as time goes on and take a gander at both drawing nearer and dynamic packages.
This sort keeps a table that screens each open affiliation. Exactly when new packages appear, it takes a gander at information in the group header to the state table – its overview of real affiliations – and chooses if the bundle is fundamental for a set up affiliation. On the off chance that it is, the group is let through less any extra examination. In case the package doesn't facilitate with a current affiliation, it is evaluated by the standard set for new affiliations.
Yet stateful appraisal firewalls are exceptionally effective, they can be weak against renouncing of-organization (DoS) attacks. DoS attacks work by taking advantage of set up affiliations that this sort generally acknowledges that are secured.
Packet separating
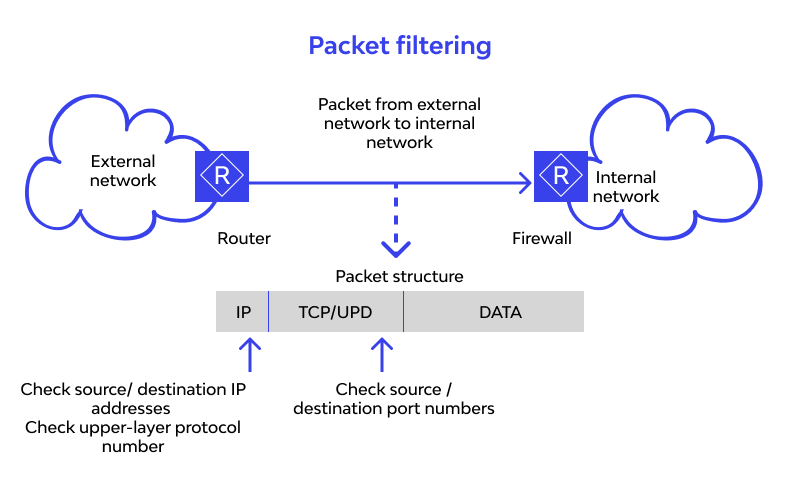
Exactly when a parcel goes through a bundle separating firewall, its source and target area, show and target port number are checked. The pack is dropped – which implies not shipped off its goal – if it doesn't adjust to the firewall's standard set. For example, if a firewall is orchestrated with a norm to block Telnet access, the firewall will drop packs destined for Transmission Control Protocol (TCP) port number 23, the port where a Telnet specialist application would tune in.
A bundle separating firewall works basically on the association layer of the OSI reference model, but the vehicle layer is used to get the source and target port numbers. It examines each group independently and doesn't understand whether any given parcel is fundamental for a current stream of traffic.
Next Generation Firewall (NGFW)
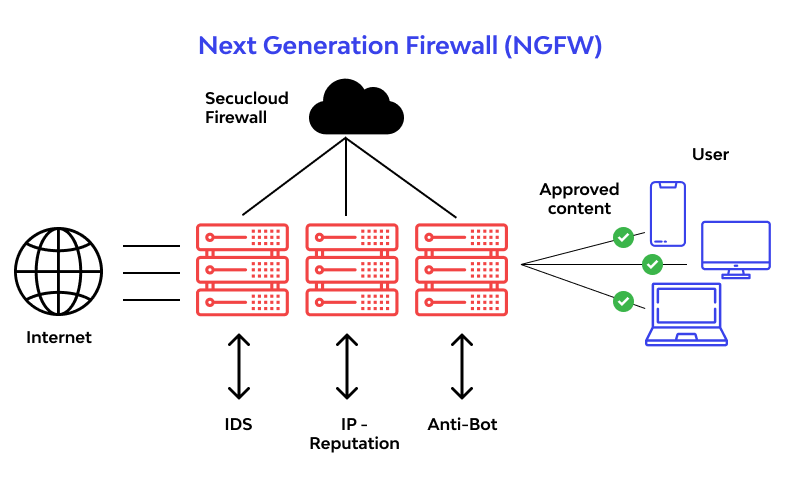
This sort is a mix of various types with additional security programming and devices bundled in. Each type has its own characteristics and inadequacies, some guarantee networks at different layers of the OSI model. The benefit of a NGFW is that it merges the characteristics of every sort cover each type's inadequacy. A NGFW is much of the time a pile of progressions under one name rather than a single part.
Current association edges have so many entry centers and different sorts of customers that more grounded permission control and security at the host are required. This prerequisite for a multi-layer approach has provoked the advancement of NGFWs.
A NGFW arranges three distinct advantages: ordinary firewall capacities, application care and an IPS. Like the colleague of stateful examination with unique firewalls, NGFWs convey additional setting to the firewall's dynamic cycle.
NGFWs join the limits of regular endeavor firewalls - including Network Address Translation (NAT), Uniform Resource Locator (URL) impeding and virtual private associations (VPNs) - with nature of organization (QoS) helpfulness and parts not by and large found in unique things. NGFWs support assumption based frameworks organization by including Secure Sockets Layer (SSL) and Secure Shell (SSH) assessment, and reputation based malware area. NGFWs also use significant pack survey (DPI) to truly check out the substance of packages and prevent malware.
Exactly when a NGFW, or any firewall is used identified with various contraptions, it is named bound brought together danger the executives (UTM).
NAT firewalls
Completely known as Network address interpretation, grants various contraptions with independent association areas to connect with the web using a singular IP address, keeping individual IP addresses stowed away. Therefore, aggressors looking at an association for IP addresses can't get express nuances, giving additional unmistakable assurance from attacks. NAT firewalls resemble go-between firewalls in that they go probably as an arbiter between a get-together of PCs and outside traffic.
Proxy firewalls
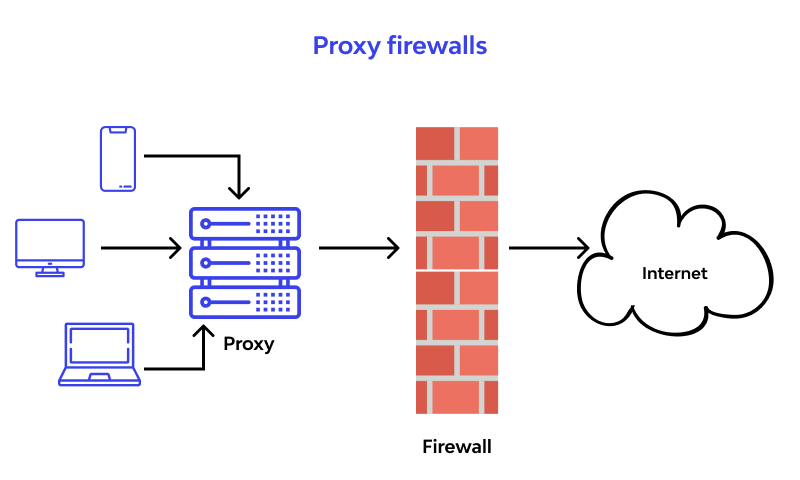
This sort may moreover be insinuated as a mediator based or reverse delegate firewall. They give application layer isolating and can assess the payload of a group to perceive authentic requesting from malicious code concealed as a considerable sales for data. As attacks against web laborers ended up being more ordinary, it became obvious that there was a prerequisite for firewalls to safeguard networks from attacks at the application layer. parcel sifting and stateful assessment firewalls can't do this at the application layer.
Since this sort dissects the payload's substance, it gives security plans more granular order over network traffic. For example, it can allow or deny a specific moving toward Telnet request from a particular customer, while various sorts can simply control general moving toward sales from a particular host.
Exactly when this sort lives on a mediator laborer – making it a delegate firewall - it makes it harder for an assailant to discover where the association truly is and makes another layer of security. Both the client and the specialist are constrained to lead the gathering through a go-between - the mediator laborer that has an application layer firewall. Each time an external client requests a relationship with an internal specialist or the opposite way around, the client will open a relationship with the delegate in light of everything. If the affiliation request meets the actions in the firewall rule base, the middle person firewall will open a relationship with the referenced laborer.
WAF
While traditional firewalls help with protecting private associations from malevolent web applications, Web application firewalls help with safeguarding web applications from poisonous customers. A WAF gets web applications by separating and seeing HTTP traffic between a web application and the Internet. It commonly defends web applications from assaults like cross-site scripting (XSS), record joining, and SQL imbuement, among others.
By sending a WAF before a web application, a defend is set between the web application and the Internet. While a go-between based firewall gets a client machine's person by using a center individual, a WAF is a kind of chat mediator, protecting the specialist from receptiveness by having clients go through the WAF preceding showing up at the laborer.
SMLI firewalls
Stateful multi-layer review separate packages at the affiliation, transport, and application layers, separating them against known confided in gatherings. Like NGFW firewalls, SMLI additionally look at the whole bundle and conceivably permit them to pass in the event that they pass each layer freely. These firewalls survey packs to pick the condition of the correspondence (in this way the name) to guarantee all started correspondence is basically occurring with confided in sources.
Firewall vs. Antivirus: Understanding the Distinction
Many users confuse the two, but they serve different roles:
- Firewall: A perimeter defense. It stops threats before they enter the system.
- Antivirus (Endpoint Security): An internal defense. It identifies and removes threats (like viruses or malware) that have already landed on a device, often via encrypted email or USB drives.
Advanced Firewall Functions: NAT and VPN
Network Address Translation (NAT)
NAT allows a whole network of computers to share a single public IP address. This adds a layer of security because it hides the specific IP addresses of internal devices from the public internet.
Virtual Private Network (VPN) Integration
Most modern firewalls act as VPN gateways. This allows remote employees to create an encrypted "tunnel" into the corporate network, ensuring that sensitive data is not intercepted over public Wi-Fi.
Application Layer Gateways and API Traffic Management
Today’s traffic is increasingly driven by APIs. Traditional firewalls struggle with the "business logic" of an API call. Application Layer Gateways inspect the specific commands being sent to an application, ensuring that a user isn't just "allowed in" but is also "allowed to perform that specific action."
Best Practices for Firewall Configuration and Management
- Principle of Least Privilege: Start by blocking everything and only open the ports that are absolutely necessary.
- Regular Audits: Rulebases grow messy over time. Use automated tools to find and delete "shadow rules" or redundant policies.
- Patch Management: Firewalls are software too. In 2024, several major firewall vendors faced zero-day exploits; keeping firmware updated is a Tier-1 priority.
How Wallarm Elevates Firewall Security (WAAP)
Traditional firewalls and even NGFWs often fail at the Application Layer (Layer 7). Wallarm provides a Web Application and API Protection (WAAP) platform that integrates the best of firewall technology with modern AI.
- Automated Protection: Wallarm eliminates the need for manual "regex" rules, using AI to identify malicious intent.
- API Discovery: You cannot protect what you cannot see. Wallarm automatically maps your APIs and protects them from "Shadow API" threats.
- Low False Positives: While traditional firewalls often block legitimate users, Wallarm’s behavioral analysis ensures high-performance security without disrupting the user experience.
FAQ
- Packet filtering firewall
- Stateful firewall
- Next-generation firewall
A software firewall is installed on a single device and provides protection only to that device, while a hardware firewall is a standalone device that provides network-wide protection to all connected devices. To learn more about the differences, see this article
Yes. Both Windows and macOS come with a built-in firewall that provides basic protection. However, for better security and advanced features, it is recommended to use a third-party firewall software.
A firewall filters incoming and outgoing network traffic using predefined rules to allow or block traffic based on specific criteria such as IP addresses, ports, and protocols.
A firewall is a network security device that monitors and controls incoming and outgoing traffic to protect your network and devices from unauthorized access, malware, and cyber threats.
References
- IBM Security: Cost of a Data Breach Report 2024.
- Gartner: Magic Quadrant for Network Firewalls.
- Fortune Business Insights: Next-Generation Firewall Market Analysis 2025.
- Akamai: State of the Internet: Web Application and API Attack Trends 2024.
Subscribe for the latest news
















