Spyware - What is it and how to protect yourself from it?
Introduction
Spyware is a hurtful type of software that covertly gets private data determined to hurt you or your business.
Despite the way that "spyware" may seem like it has a place in a spy film, this shrewd program is everything except fun. The most pervasive peril on the web right currently is spyware. Because of its secret nature, it may be trying to recognize and penetrate your gadget very well.
This article contains spyware definition as well as spyware detection, removal and protection methods.

Spyware definition
Spyware is noxious software that penetrates a processing climate secretively and subtly accumulates individual information to adversely influence an individual or an association. It falls under the classification of malware or vindictive software put on a PC without the client's consent. It penetrates the gadget, assembles client information and web utilization information, and afterward sends it to questionable sponsors, information ranches, or other outsiders. On the off chance that the program was introduced without the client's authorization, it is named spyware. Spyware is hazardous because it can break an end client's protection and consider information double-dealing in any event when downloaded for what appear to be guiltless causes.
History of spyware
During the 1990s, the expression "spyware" first showed up in quite a while. However, it was only after the mid-2000s that network protection organizations started utilizing it to allude to undesirable software that observed client and PC conduct. Finally, in June 2000, the primary enemy of spyware programs was made accessible. After four years, checks by America Online and the National Cyber Security Alliance uncovered that spyware had tainted the frameworks of around 80% of web clients. Nonetheless, 95% of buyers had not approved its establishment, and 89% were uninformed that the software existed.
Spyware in action
To guilefully enter and taint gadgets, assailants astutely mask spyware. They achieve this by concealing the destructive documents among regular downloads and site pages, which entices customers to get to them — frequently unwittingly. Then, through coding blemishes or in uniquely made fake applications and sites, the contamination will exist together with respectable projects and sites.
Bundleware is one way utilized as often as possible to disseminate spyware. This variety of software applications combines efforts with different projects that a client has downloaded or set up. It will subsequently introduce without the client monitoring it. Other bundleware items urge the client to acknowledge the download of a total software pack without giving them any advance notice that their gadget has been contaminated intentionally. Similar strategies utilized by different kinds of software, for example, phishing messages and undermined or counterfeit sites, can likewise be utilized by spyware to taint a PC.
Three methodologies are as often as possible utilized by versatile spyware to go after cell phones:
- Working framework issues: Attackers can exploit versatile working framework shortcomings, frequently made accessible through openings in refreshes.
- Noxious applications are now and again hidden inside dependable ones that individuals download from sites instead of application stores.
- WiFi networks' open spaces, like air terminals and restaurants, are frequently free and simple to pursue, which makes them a critical security risk. In addition, aggressors can utilize these organizations to screen associated clients' exercises.
How does infection happen?
To introduce and run undetected, vindictive spyware should cautiously cover itself. Its techniques for contamination are subsequently typically concealed inside what have all the earmarks of being regular downloads or site pages. Using weakness takes advantage, this software might be tracked down in or close by reliable projects and sites, as well as on exceptionally made deceitful applications and sites.
Spyware is often circulated through bundleware, otherwise called packaged software items. In this case, the product joins an alternate program you deliberately download and introduce.
What problems does spyware cause?
If you have been tainted with spyware, it may be hazardous. Less than overwhelming burdens to long-haul monetary mischief are potential dangers. The following are a couple of these issues that are generally regular:
- Information ad identity fraud
Spyware can at first — and presumably above all — take private information that can be taken advantage of for character extortion. Pernicious software can accumulate a very sizable amount of data to mimic you if it approaches each piece of information on your machine. This incorporates perusing history, email locations, and passwords put something aside for informal communities, internet shopping, and banking.
- Harm to PCs
You will frequently experience the mischief that spyware can cause to your PC. Inadequately developed spyware can adversely affect framework execution. The memory, processor power, and web transfer speed utilized by your PC may be expanded if presentation improvement isn't executed. Accordingly, contaminated gadgets could slack and work gradually while on the web or exchanging between applications.
- Issues With Your Online Experience
Moreover, spyware can fudge web index results and power undesirable sites into your program, which might take you to vindictive or false sites. It might try and change a portion of your PC's settings and prompt your landing page to change. A similarly irritating issue that accompanies different spyware types is pop-up advertisements. In any event, when disconnected, ads might, in any case, appear, causing unavoidable irritations.
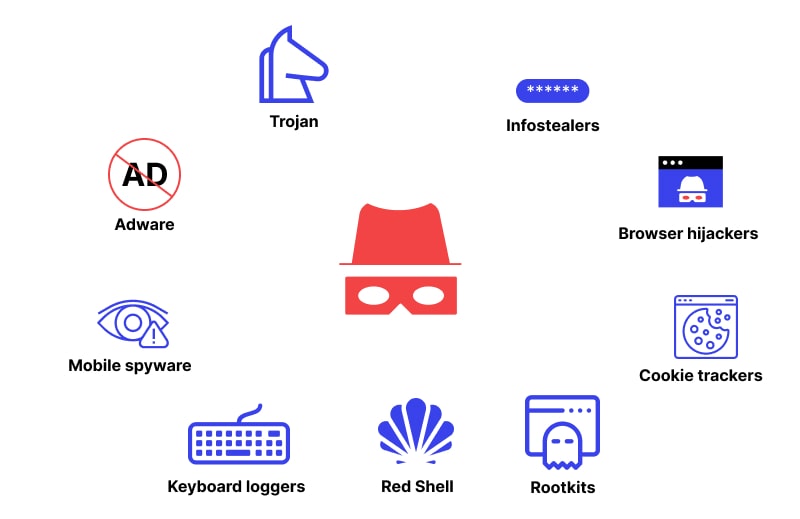
The main types of spyware
A destructive piece of software or malware that professes to be lawful yet can assume control over your gadget is known as a Trojan pony or a Trojan. A PC program known as a Trojan pony is made to harm, disrupt, take, or in any case, undermine your organization or data. A Trojan camouflages itself as a dependable application or record to deceive you.
- Adware
The words "software" and "promoting" were joined to make its name. Regardless of whether or not toxic, adware is generally any program that shows promotions on a PC. For example, legitimate applications might utilize adware to offer their administrations without charge. Notwithstanding, certain spyware can likewise work as adware.
- Mobile spyware
The expression "stalkerware" alludes to a gathering of innovations (applications, projects, and gadgets) that permit somebody to watch and track the activities of your telephone furtively. Mobile spyware can be exceptionally obtrusive and destructive for clients since it can follow various client movements on their cell phones, including screen captures and recordings taken, sites visited, instant messages, call logs, and GPS facilitates.
One kind of spyware that is trying to find is a keylogger. While you input essential data into your console in the conviction that nobody is watching, keylogging software attempts to catch all that you type.
- Red Shell
While an individual introduces specific PC games, this malware settles in on the gadget and starts observing their web-based movement. Most of the time, engineers use it to better their showcasing endeavors and games.
Programmers can access and control a PC through a rootkit, a kind of spyware. Despite the way that most of the rootkits focus on the framework and introduced programs, some can keep an eye on your framework while going after the firmware and design of your PC.
- Infostealers
Such malware runs behind the scenes and covertly assembles data about the machine, associated clients, and server logs. Its goal is to take login subtleties, personalities, passwords, and other private or secret information locally or on connected mists.
- Browser hijackers
Modem commandeering, which influences dial-up web associations through a telephone line, is the most seasoned kind of spyware. It is, as of now, not a severe gamble because most individuals never again have dial-up associations.
- Cookie trackers
A text record called a cookie tracker is added to a program while a client is perusing a page. This text gathers information about an individual's site utilization, search history, area, a penchant to make buys, and different things.
Examples of spyware
The accompanying rundown incorporates probably the most notorious spyware examples that have been found:
CWS: This spyware, known as CoolWebSearch, began around 2003. First, your program is shipped off another landing page, after which it routinely creates pop-up publicizing, often guiding clients to sketchy sites while modifying program settings so perilous sites are named as "safe."
Olympic Vision: Email crusades designated at workers of specific organizations assist with spreading Olympic Vision. Keystrokes are recorded, and clipboard data and other client accreditations are likewise taken.
HawkEye: This keylogger subtly records data like keystrokes, login certifications, and other profoundly touchy individual information.
How to identify spyware
How can one detect spyware? For Windows working frameworks, it was by and by a worry. However, that is, at this point, not stringently the case. Computers, Macs, iOS, and Android gadgets, including cell phones and tablets, can be generally influenced by spyware. Essentially, spyware might taint any gadget that can associate with the web.
These are a few strategies for spyware detection:
- Tolerating a pop-up or incite without first understanding it
- Software downloaded from a questionable source
- Opening connections in messages sent by obscure shippers
- Pilfering games, music, or different media
- Choosing a connection that prompts a malevolent site
- The creators of spyware could trick you with cunny techniques. The spyware might be incorporated with free software introduced as a supportive device or contained in an email connection that looks real.
How to Remove Spyware
As well as being obtrusive, spyware slows down your PC, disrupts your experience, and accumulates information that could bring about massive damage. For example, spyware put on business frameworks or individual gadgets claimed by experts with dynamic authority might be unreasonably utilized by rivals. Therefore, you should be shielded from spyware and adware if you have introduced antivirus software. Notwithstanding, if you accidentally end up with a contaminated PC, adhere to these guidelines to remove spyware.
- Uninstall new applications: Uninstall any dubious applications by going to your telephone's settings and choosing "Applications."
- Examine for malware or antivirus software: You could, as of now, have an application introduced on your telephone, or you could have to download and set up a dependable application from the gadget's actual application store.
- Consider backing up your information and playing out an industrial facility reset on your telephone on the off chance that infection filtering and application uninstallation don't determine the issue.
How can I protect myself from spyware?
Any gadget connected to the web is continually in danger from malware like spyware. Getting a web security platform consolidates the defense against spyware virus. In addition, organizations like antispam channels, cloud-based discovery, and virtual scrambled consoles are helpful to lessen the chance of crime.
Some spyware varietys can likewise introduce projects and change framework settings on a client's gadget. Therefore, it follows that to keep up with the security of their characters and the current status of their gadgets, clients should likewise utilize secure passwords, forgoes utilizing the equivalent login data across various applications and sites, and systems like Multifactor Authentication (MFA).
To protect gadgets and frameworks, notwithstanding software, the following spyware protection procedures can be initiated:
- Treat consent: When a treat assent pop-up window shows up on almost every page a client visits, it very well may be essential for them to click "acknowledge." However, they should practice alertness while giving their consent each time and ought to permit treats from legitimate sites.
- Clients can likewise introduce against following additional program items to stop obtrusive web observing of their perusing propensities. The information of clients who visit the web is kept hidden by these augmentations, which can forestall action followed by both reliable sources and destructive entertainers.
- Security refreshes: Keeping software refreshed to the latest renditions is fundamental for avoiding contaminations like spyware. Working framework blemishes or code holes typically permit spyware to enter PCs and other electronic gadgets. Hence, it's essential to fix possible issues and weaknesses when they emerge.
- Please keep away from free software: While downloading free software might appear captivating, doing so can have costly impacts on customers and their organizations. The creator of the free software might profit from the clients' information, and the actual product might be shaky.
- Utilize secure organizations; programmers can undoubtedly access gadgets utilizing unreliable WiFi organizations. Cease associating with unstable, public WiFi organizations; utilize dependable organizations.
- The best way of practice: For spyware to be kept away, great network safety rehearses should be followed. Clients should be aware of the security dangers they are presented with, avoid opening messages or downloading files from senders whom they don't know, and foster the act of drifting over connections to decide their authenticity before tapping on them.
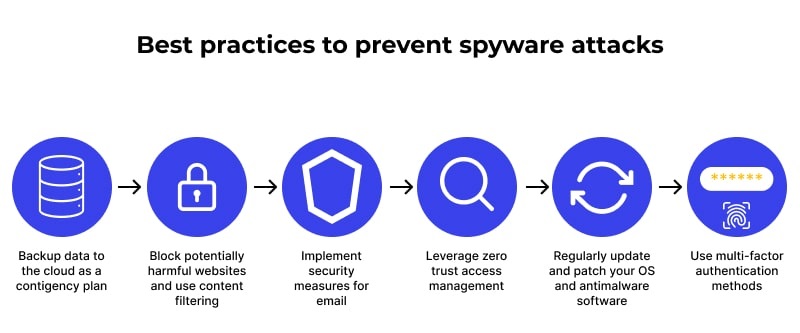
Clients of PCs and PCs can make specific moves to get their hardware. On their PCs, they can empower and download pop-up blockers, and they can likewise limit the projects and authorizations that are permitted. All clients should cease clicking or opening any connections tracked down in messages, even those professing to come from trustworthy sources. These activities are typical for spreading spyware and another hazardous software.
Moreover, activities should be possible to protect cell phones from spyware explicitly. These comprise:
- Download software from trustworthy distributors and the working framework's actual store, for example, the Google Play Store or the Apple App Store.
- Be careful while giving admittance to applications that track data or area and seize receivers or cameras.
- Email and SMS connections ought not to be clicked—instead, sort URLs into your program's location bar as another option.
- Be careful about strange advance notice messages, especially those the server can't affirm.
Subscribe for the latest news









%20Attack.jpg)







