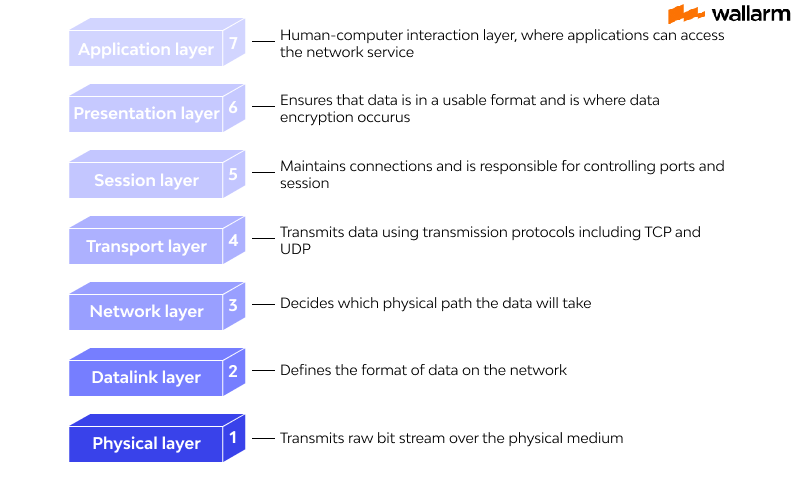
Explanation of the 7 Layers of OSI model
Explanation of OSI model layers
As an IT master, chances are you probably go over the articulation Please Do Not Throw Sausage Pizza Away while finding out about programs, network plan, and execution issues.
Isn't there something to be said about the phrase "Please Do Not Touch Steve's Pet Alligator"?
If you accept that these ring a bell, you're advancing pleasantly: These are useful memory aids associated with the OSI model's seven tiers. The crucial letter of each phrase assists in comprehending the OSI model's layer architecture and identifying the real layer.
However, before we dive into the subtleties, we should start for specific essentials about precisely what the OSI network model is.

What is the OSI Model?
The OSI model can assist you with seeing how information streams across and inside networks. After the consolidation of two models from the 1970s, it was received as a general norm in 1984.
Essential PC and telecom affiliations utilized this model to disconnect gadget to-contraption correspondence into seven layers. These seven layers go likely as a visual manual for understand what's happening in a structures association framework.
For IT experts then, at that point and now, the OSI model procedures focused in on looking at improved: rather than squandering hours deciphering issues, they can pinpoint issues related with unequivocal layers.
For network device traders, application fashioners, and connection plans, the model strategies abstracting away eccentricism from contraption to-device correspondence, by focusing in on dealing with each issue thus. Besides, the model was made to give standardized sorting everything out shows to avoid the use of contraptions that need customer and application-honesty.
History of OSI Model
Throughout the entire existence of the OSI model, the following significant achievements have happened:
- In the last piece of the 1970s, the ISO dispatched a mission to progress nonexclusive structure the board guidelines and practices.
- The United Kingdom's Experimental Packet Switched System recognized the need for additional high-level shows in 1973.
- In the year 1983, OSI model was from the beginning proposed to be a particular detail of certified interfaces.
- The OSI configuration was authoritatively gotten by ISO as a worldwide standard in 1984.
7 layers of the OSI model
- The application layer
Also, the foundational level of the OSI model is the application layer, which interfaces with an application software. The application layer is the OSI layer closest to the end-user. It supports OSI application layer licenses that allow clients to communicate with other programming applications.
Application layer partners with programming applications to finish a passing on bundle. The perception of information by the application program is dependably outside the level of the OSI model. Portrayal of the application layer is an application, for example, record move, email, far away login, and so forth.
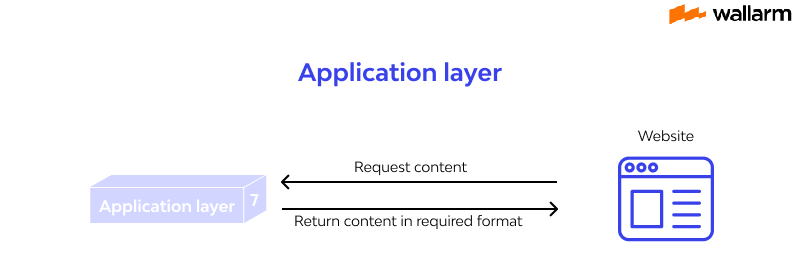
The Application Layers give the going with purposes:
- Application-layer helps you with seeing correspondence accomplices, picking resource straightforwardness, and synchronizing correspondence
- It licenses customers to sign on to a far away have
- This layer gives specific email affiliations
This software gives you access to important instructional file sources as well as information about numerous publications and organizations.
- The presentation layer
The data for the application layer is arranged in this layer. It shows how information ought to be encoded, mixed, and stuffed by two gadgets so that it is effectively gotten at the farthest edge. The showcase layer readies any information given by the application layer for transmission through the get-together layer.
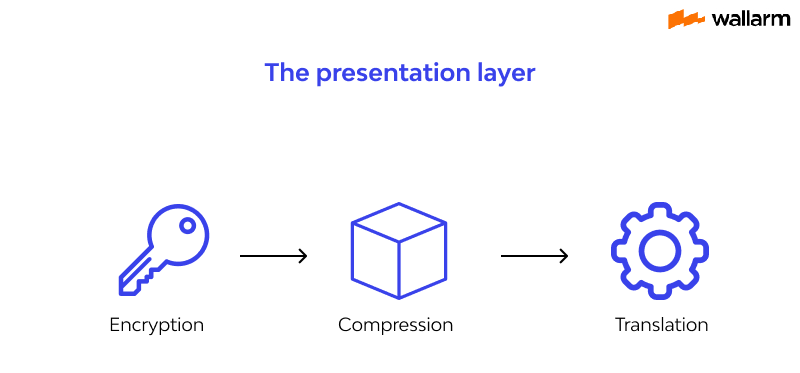
Presentation Layer's capabilities:
- Character code translation from ASCII to EBCDIC.
- Information pressure: Allows to diminish the proportion of pieces that ought to be sent on the alliance.
- Information encryption: Helps you to scramble data for security purposes — for example, secret key encryption.
- It goes with a UI, also as email and document move limits.
- The session layer
The discussion between PCs is overseen by this layer. It assists you with starting and finish the association between the space and the distant application.
This layer is liable for making a solid working relationship with the end client reliant upon their essentials. This layer handles all fundamental sign-on or secret key supporting. One of the affiliations offered by the social occasion layer is exchange discipline, which might be half-duplex or -duplex. It's an ordinary occasion in programs with a high number of technique calls.
Significant capacity of Session Layer:
- It creates, stays mindful of, and closes a social event
- Meeting layer empowers two designs to go into a discussion
- It's anything but's a collaboration to add a doled out spot to steam of information
- The transport layer
The affiliation layer is made by the layer responsible for transport, which licenses information to be bestowed from an interest on a source PC to a cycle on an objective machine. It is coordinated through a solitary a few affiliations, and it thinks about authoritative hindrances.
It picks how much information ought to be sent where and at what rate. This layer develops the message which are gotten from the application layer. It guarantees that information units are passed on screw up free and in arrangement.
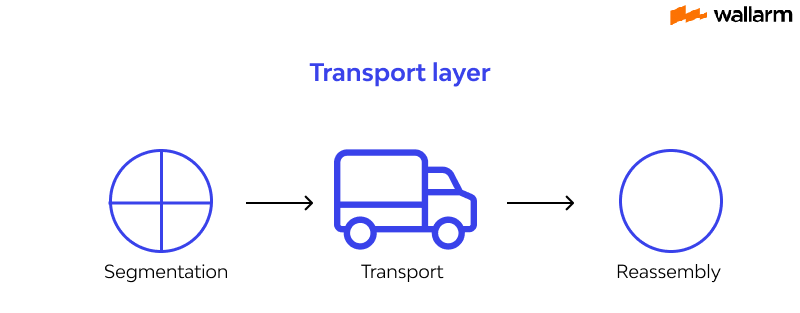
Through stream the board, wreck control, and division or desegmentation, the vehicle layer helps you with remaining mindful of the consistency of an affiliation.
On the off chance that no stumbles happen, the vehicle layer other than gives an insistence of the convincing information development and passes on the associated information. TCP is the most striking vehicle layer portrayal.
Significant capabilities of transport layers:
- It isolates the message got from the social event layer into portions and numbers them to make a get-together.
- Transport layer ensures that the message is given to the right coordinated effort on the objective machine.
- It likewise ensures that the whole message shows up with no mistake else it ought to be retransmitted.
- The network layer
Starting with one affiliation and moving to the next, this layer is in responsibility of information transmission planning and administration. It picks the most restricted possible way beginning with one host then onto the following on different associations.
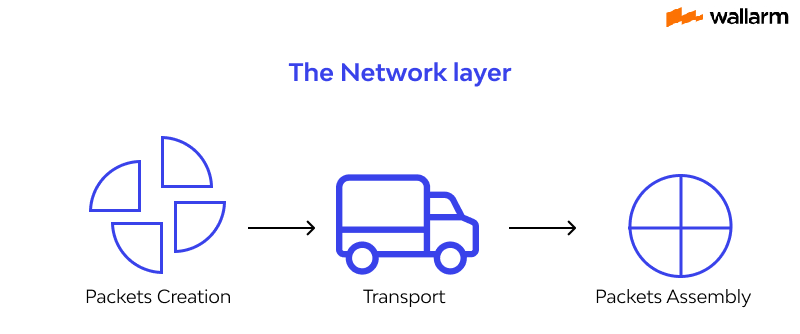
At the point when the package is gotten from the DLL, the organization layer recognizes whether the group is destined for the area have (in which case it's sent up to a higher layer), is headed for a substitute host on the close by association (wherein case is sent down to a lower layer), or is destined for a substitute association all around, and for the present circumstance it does the indispensable coordinating to the area contained in the packaging.
In the standard TCP/IP model, this is done by executing reasonable IP tending to and using switches for correspondence. Data going out are disengaged into bundles which are then reassembled at the not exactly alluring end.
Web Protocol Version 4 (IPv4), Version 6 (IPv6) of Internet Protocol, ICMP, and GRE are instances of Layer 3 standards.
- The data link layer
Errors in the real layer are corrected by the data link layer. You may use this layer to figure out how a connection between two network devices is formed and ended.
It's anything but an IP address sensible layer that guides in the recognizable proof of any endpoint by permitting you to portray predictable tending to. The layer further guides you in directing bundle controlling inside an association. It helps you in deciding the ideal strategy for getting data from the source to the objective.
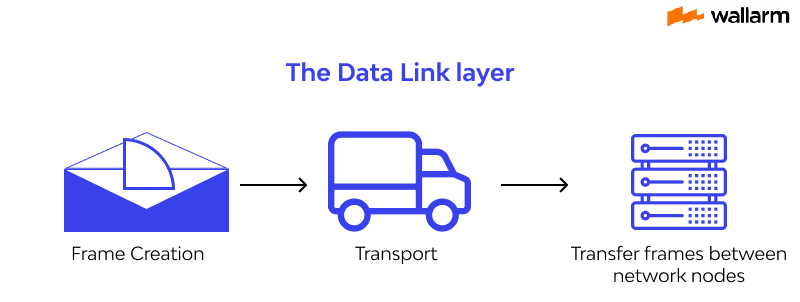
The information interface layer is partitioned into two sorts of sublayers:
- Media Access Control (MAC) layer-It is responsible for controlling how device in an association access medium and licenses to impart data.
- Consistent association control layer-This layer is responsible for character and exemplifying organization layer shows and allows you to find the goof.
Significant capabilities of Datalink Layer:
- Outlining what segments the data from Network layer into traces
- Permits you to add header to the edge to portray the real area of the source and the target machine
- Adds Logical areas of the sender and authorities
- It is furthermore at risk for the sourcing cycle to the target connection movement of the entire message.
- It's everything except a system for goof control wherein it recognizes retransmits mischief or lost edges.
- Datalink layer moreover gives a framework to send data over free associations which are associated together
- The physical layer
The actual layer, being the first layer in the OSI architecture, is responsible for establishing a physical cable or remote connection linking network hubs (gadgets). It characterizes the media, association, and sign sort (regardless of whether simple or advanced) to be utilized, and communicates that crude information as signs. All frameworks organization devices and specifics, similar to radio frequencies and hardware, are described at this layer. Occasions of parts at the real layer consolidate radio wires, network interface cards (NIC), cabling, connectors, and pins.
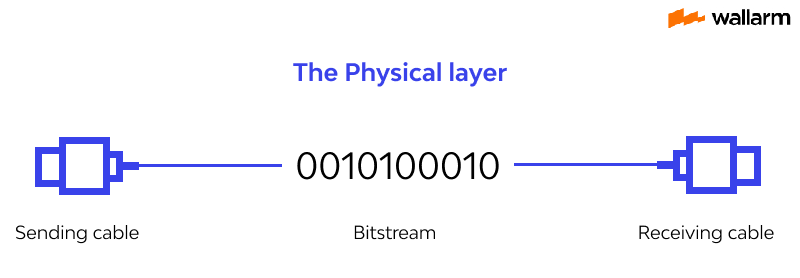
The fundamental services of this layer are:
- Touch rate control and synchronization
The quantity of pieces each second and spot synchronization are characterized.
- Actual topography
How the devices are planned inside the association, whether or not transport, star, ring, organization, etc.
- Transmission mode
Determinations that control data stream according to simplex, half-duplex, and full-duplex mode. Most, if not all, progressed wired associations use full-duplex transmission modes.
- Actual characteristic definition
Sort of connector, pin strategy, interface card, and so on.
Pros and cons of OSI model
Pros:
- It assists you with normalizing switch, switch, motherboard, and other equipment
- Lessens intricacy and normalizes interfaces
- Works with measured designing
- Assists you with guaranteeing interoperable innovation
- Assists you with speeding up the development
- Conventions can be supplanted by new conventions when innovation changes
- Offer help for association situated administrations just as connectionless assistance
- It's anything but a standard model in PC networking
- Supports connectionless and association situated administrations
- Offers adaptability to adjust to different kinds of conventions
Cons:
- Fitting of conventions is a dreary assignment
- You can just utilize it's anything but a reference model
- Doesn't characterize a particular convention
- In the OSI network layer model, a few administrations are copied in numerous layers, for example, the vehicle and information interface layers
- Layers can't work in equal as each layer need to hold on to acquire information from the past layer
Why use the OSI model?
The OSI model aides clients and administrators of PC organizations:
- Decide the necessary equipment and programming to fabricate their organization.
- Comprehend and convey the cycle followed by segments imparting across an organization.
- Perform investigating, by distinguishing which organization layer is causing an issue and zeroing in endeavors on that layer.
The OSI model aides network gadget makers and systems administration programming merchants:
- Make gadgets and programming that can speak with items from some other seller, permitting open interoperability
- Characterize what parts of the organization their items should work with.
- Convey to clients at which organization layers their item works – for instance, just at the application layer, or across the stack.
With the OSI network model considered by some as obsolete and unreasonable, the inquiry that springs up is ordinarily: Why use it? Security and organization improvement are the primary reasons why keen IT specialists actually draw out the OSI model to investigate and impart complex organization challenges with each other:
- Investigating:
The OSI model permits IT experts to coherently separate complex organization challenges into reasonable errands, in this manner giving designated spots along the investigating venture. In the event that a client is having network execution issues, you can check the nature of the association at Layer 1, Layer 2, Layer 3, and so forth to limit the exhibition issue.
- Correspondence:
While most of IT experts know about the TCP/IP web model, there are other correspondence networks in nature. Having the OSI model permits IT experts to speak with each other conflicting and effectively unmistakable terms to decrease miscommunications.
OSI Model vs. TCP/IP
Notwithstanding the unpreventable data on the OSI network model, it's typical diverged from the 4-layer TCP/IP model. As an IT capable, it's huge that you appreciate the qualifications and similarities between these two models. Taking everything into account, they're not in challenge yet rather are associated.
In the TCP/IP model, the application layer plays out the limit of the three more huge level (5, 6, 7) layers of the OSI model. Moreover, an association access layer in the TCP/IP model joins the limit of two lower-level (1 and 2) layers in the OSI model and leaves sequencing and certification abilities to the vehicle layer.
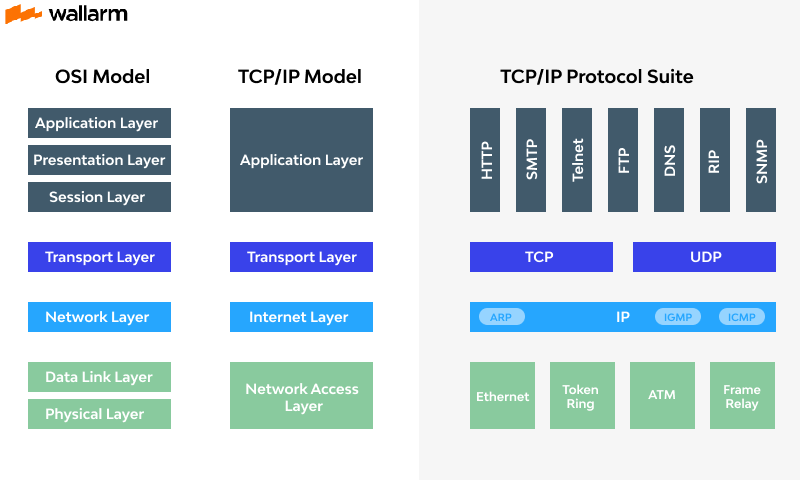
Why this critical difference? Essentially considering the way that the OSI model was portrayed after a huge piece of the TCP/IP model was set up. Perhaps than endeavor and structure the OSI model to the 4-layer TCP/IP model, a more adaptable 7-layer model was made.
Notwithstanding not getting on for the most part, the OSI model is at this point used today when insinuating organize plan, and still appears as an expected request on accreditation tests (and maybe your next imminent representative gathering?).
So make sure to remember Please Do Not Throw Sausage Pizza Away, so you can have a run of the mill frameworks organization language to attract with clients, dealers, and other association administrators.
Subscribe for the latest news

















