NCSC's Cyber Assessment Framework (CAF) - Guide
CAF assesses how satisfactorily an organisation manages cyber threats to core functions. The outcomes of cyber-attacks vary widely, both in terms of the nature of the computer systems attacked and the goals of the attackers. Generally, very strong levels of cyber privacy and flexibility are required in cases where the potential effects of cyber disasters are highly significant or even, maybe, catastrophic. Since this is the case, the NCSC has compiled the Cyber Assessment Framework (CAF) for the institutions administrating the essential services and pursuits that are to the collective advantage of all of us.

What is NCSC?
It is the UK government's procedural specialty on data protection. It was established in 2016 as part of the government's five-year Data Protection Strategy. It operates as part of GCHQ, the UK's surveillance and intelligence gathering entity. It works closely with law enforcement agencies, state departments, and the personal sector to protect the UK's vital national wireframe and other essential systems.
It provides a wide range of data protection services and advice, including threat intelligence, incident management, vulnerability assessments, and counselling on best practice for cybersecurity. It also works to raise awareness of privacy risks and provides training and resources to help individuals and businesses advance their infosec practices.
In addition to the operational tasks it does, it is also responsible for establishing cybersecurity benchmarks, as well as producing guidelines and policy for matters related to cybercrime. It is a founding member of the Five Eyes intelligence partnership, along with the intelligence agencies of the United States of America, Canada, Australia, and New Zealand, and it collaborates with international partners to advance global data protection collaboration.

What is CAF?
Organizations' ability to manage virtual risks to critical functions can be evaluated with the use of the NIS Cyber Assessment Framework (CAF), which offers a systematic and all-encompassing method for doing so. It can be employed by the organization in charge of consent or by an outside party, such as a controller or a appropriately competent association operating on the regulator's behalf.
It is based on the concepts of cybercrime and suppleness established by the NCSC CAF. Rather than being a laundry list of tasks, the 14 regulations are written regarding consequences or the precise objectives that must be attained. Next, we'll go into more depth on how the it takes the high-level directions and adds extra degrees of detail, such as a collection of structured sets of Indicators of Good Practice (IGPs).
The NCSC, in its capacity as the nation's technical authority on cyber security, created the CAF with the hope that it would be employed in part to facilitate efficient cyber regulation. The NCSC is not responsible for regulating anything, thus organizations who are regulated in the cyberspace should talk to their own regulators about whether or not they need to use the it.
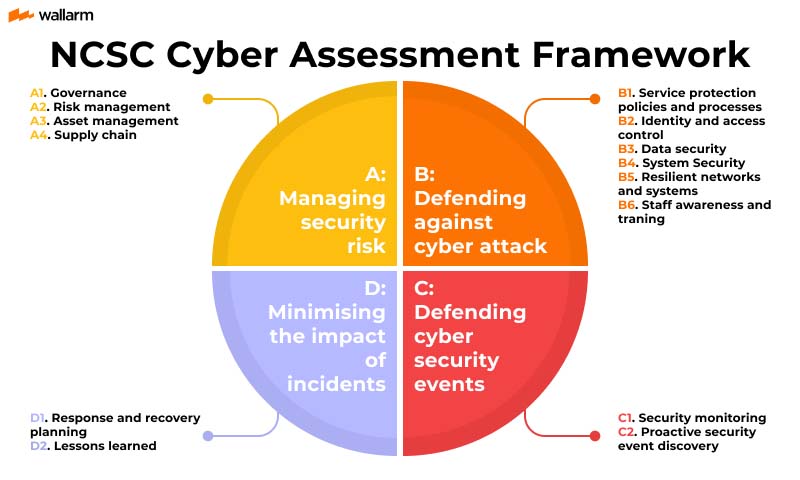
4 CAF goals and 14 regulations
NCSC's high-level CAF helps OESs and CAs capitulate with NIS Guidelines. It has four privacy purposes:
Goal A: Dealing protection threat.
The grid and info systems supporting key tasks have proper organizational structures, rules, and methods to analyze, evaluate, and supervise safety risks.
- A1. Government
Implementing your company's network and infosec rules.
- A2. Risk Management
Security risk assessment and comprehension. And a company-wide risk management strategy.
- A3. Asset Management
Identifying and understanding all systems and services needed for vital functions.
- A4. Logistics
Identifying and controlling external supplier-related network and information system threats.
Goal B: Protecting against cybercrime
Net and info structures supporting important tasks are protected from cyberattack by proportionate security measures.
- B1 Service protection policies and processes
Creating and disseminating organizational rules and processes to safeguard systems and data that support vital functions.
- B2. Identity and access control
Understanding, recording, and regulating access to important nets and info systems.
- B3 Data Security
Safeguarding stored or electronically transmitted data from activities that could harm critical functionality.
- B4. System security
Cybersecurity for vital networks and information systems.
- B5 Resilient networks and systems
Developing cyber-resilience.
- B6 Staff awareness and training
Supporting employees to progress vital function cyber security.
Goal C: Detecting cyber security events
Safety defenses and cyber protection events affecting vital functions are monitored.
- C1 Safety monitoring
Monitoring for security issues and security effectiveness.
- C2 Proactive security event discovery
Identifying anomalies in relevant net and data systems.
Goal D: Minimizing the repercussions of online privacy breaches
Cybercrime happenings can be mitigated and vital functions restored.
- D1. Response and recovery planning
Implementing incident management and mitigation procedures.
- D2. Lessons Learned
Learning from occurrences to strengthen important functions.
CAF Requirements
It was designed to meet the following prerequisites:
- Give online privacy breaches resilience evaluations a framework.
- Uphold the outcome-focused NCSC cybercrime and resilience principles and discourage tick-box evaluations.
- Concede with existing protection recommendations and standards.
- Identify effective online breaches and resilience enhancement activities.
- Sector-agnostic shared core version.
- Accommodate sector-specific components as needed.
- Enable organizations to define expressive targets that may represent regulator views of adequate and proportionate security.
- Be simple and affordable to implement.
Results and Related Outcomes
When it is used, it yields a total of 39 separate ratings, each of which is based on a subjective evaluation of how well a certain group of IGPs corresponds to the examined organization. It was created such that a result in which all 39 contributing outcomes were judged as "achieved" would imply a degree of cyber security far greater than the bare minimum "basic cyber hygiene" level.
The NCSC does not have the authority to issue mandates regarding what constitutes adequate and reasonable measures of cyber security and resilience. Specifically, the appropriate regulator must define any aim established for regulated organizations to achieve in terms of CAF results.
The NCSC is collaborating with other organizations with a cyber resilience oversight role to develop a method for interpreting its output based on determining which contributing outcomes are most critical for a given organization to realize in order to effectively manage security risks to their core operations. An initial perspective on what constitutes adequate and proportionate cyber security for that organization would align with the results that were prioritized. An example of a CAF profile would be the subset of contributing outcomes that was identified as most relevant in this method; this may be used as the foundation for defining a goal for regulated organizations to attain.
In practice, a CAF profile will have a mix of outcomes marked as accomplished, partially achieved, and maybe not applicable (indicating cyber security capabilities that aren't acceptable at the profile level).
Indicators of Good Practices (IGP) and CAF
The Indicators of Good Practice (IGP) are a set of statements developed by NCSC that describe what a good practice looks like in a particular area of cybersecurity. The IGP cover a range of cybersecurity practices across different categories, including governance, risk management, access control, network security, and incident management.
The IGP statements are meant to serve as a guide for companies to better understand what constitutes secure practices and how to implement them.
Use Of CAF IGP Tables
The following table provides a concise overview of the indicators found in the CAF IGP tables, including their primary goals and characteristics.
Use of CAF
It has dual purposes under the NIS Rules at present:
- It is used by OESs to satisfy legal requirements. They conduct an internal evaluation and report the findings and recommendations to their CA ("CAF returns"). The security of OESs must be evaluated in light of each possible consequence. They can justify the security measures they've taken as necessary and reasonable in light of the threats they face. They can use the IGP tables for that purpose. They are also able to justify their lack of action with regards to a given security measure.
- The results from the CAF and the road map for OES improvement are analyzed by the Competent Authorities. Their self-assessment, CAF profile, and potential on-site inspections will all be used to determine whether or not OESs implement adequate and balanced security measures.
Conclusion
The NIS Directive mandates OESs to self-assess their security using the outcome-based CAF. CAF security is flexible. It has 4 security objectives, 14 outcomes, and 39 contributing outcomes. It will become more user-friendly in the future.
FAQ
Subscribe for the latest news


%20by%20NcSC.jpg)