IOA vs IOC
In the perplexing universe of cybersecurity, you'll often come across the acronyms Indicators of Attack (IOA) and Indicators of Compromise (IOC). These elements serve as the frontline warriors in your battle against potential security breaches. However, understanding and differentiating them and realizing their cohesive role in fortifying your digital fortress might feel daunting. This chapter aims to untangle these multifaceted protection strands, providing an exhaustive comprehension of IOA and IOC interplay.

Unraveling the Secrets of Security Protocols: IOA vs IOC
We'll start by elucidating these terms:
- Indicators of Attack (IOA): These are investigative signs that a digital onslaught is under way. IOAs function proactively, zeroing in on indications of a potential attack before it comes to fruition. This architecture aids in identifying malicious endeavors in the early stages, facilitating immediate retaliation and deterrence.
- Indicators of Compromise (IOC): These are traces suggestive of a cyber assault that has already transpired. IOCs operate retrospectively, paying heed to the situation after the attack. This structure permits identification of prior violations or intrusions, assisting in managing the incident aftermath and system reestablishment.
Having dissected IOA and IOC, let's now present them side-by-side in a matrix for enhanced understanding:
The matrix underscores the unique operational methods of IOA and IOC while emphasizing their importance in establishing a sturdy cybersecurity structure. They represent dual facets of cybersecurity, each amplifying the other's efficiency to produce a comprehensive security solution.
In the upcoming chapters, we'll gain deeper insights into the peculiar characteristics, roles, and the best methods to incorporate IOA and IOC into your cybersecurity strategy. Stick around as we incessantly untangle various cyber-protection elements, IOA vs IOC.
Unravelling Cyberspace: Spotting Attack Signals (SAs) vs Revealing Breach Signs (RBSs)
Navigating the intricate universe of cybersecurity, we often encounter two terminologies of paramount importance in our battle against virtual dangers: Spotting Attack Signals (SAs) and Revealing Breach Signs (RBSs). Though they may appear akin in some aspects, they cater to different needs and are leveraged in dissimilar scenarios. Gaining familiarity with and discerning the subtle difference between SAs and RBSs is integral for anyone engaged in the field of cybersecurity.
Spotting Attack Signals (SAs) are empirical data that suggest a cyber attack is currently in progress. They function as immediate warnings indicating a persisting risk. SAs are formulated to uncover and intercept potential threats before they inflict considerable harm. They are forward-looking strategies focusing on recognizing the modus operandi employed by cyber culprits.
Conversely, Revealing Breach Signs (RBSs) are hints that signify an accomplished cyberincursion. These are strategies implemented in response to cyberattacks, assisting in uncovering and evaluating the repercussions of a security infringement. RBSs are predominantly applied in detective analysis to comprehend the means and results of a breach and to devise preventive measures for future similar occurrences.
To simplify, imagine your home represents your network. An SA would resemble a security monitor notifying you of a trespassing attempt. In contrast, an RBS would be akin to noticing a smashed window or missing belongings after a theft has transpired.
Here's a comparison graphic to help further differentiate:
Let's delve into the specifics of each.
Spotting Attack Signals (SAs)
SAs are configured to highlight illicit operations as they transpire. They concentrate on the perpetrator's behaviour rather than the qualities of the malware, a notable shift from traditional signature-based detection approaches that hinge on recognized malware specimens.
Let's look at a simple code snippet illustrating an SA:
In this instance, the function verify_threativity reviews if the consequential traffic contains a recognized harmful pattern. When it does, a warning is set off delineating a plausible attack.
Typical instances of SAs may encompass:
- Exceptional outbound network stream
- Anomalistic privileged user account operations
- Geographic inconsistencies
- Substantial data uploads or downloads
Revealing Breach Signs (RBSs)
RBSs, conversely, aid in spotting a victorious incursion. They are generally employed in electronic forensics and incident responses (EFIR) to ascertain the nature and scope of a breach.
Let's examine a simple code snippet demonstrating an RBS:
In this instance, the function examine_infiltration scrubs through system records for breach indicators. If it discovers one, it validates that an infiltration has transpired.
Common examples of RBSs may involve:
- Discovery of malware signatures
- Unpredictable system file modifications
- Unexpected registry modifications
- Anomalous DNS requests
Summing up, both SAs and RBSs have vital roles in fortifying cybersecurity. SAs equip us in detecting and thwarting attacks in real-time, while RBSs facilitates in recognizing and appraising successful breaches. Being conversant with these two principles is critical whilst preserving an impregnable cybersecurity stance. Delving into the vast virtual ecosystem, it is crucial to discriminate between the dissimilar qualities and overlapping features of the 'Red Alert Signs' of Attacks (RSAs) and 'Red Alert Signs' of Compromise (RSCs). Both of these elements are vital cogs in the machinery of cybersecurity, each having its unique and varied usage and context.
Let's analyze the distinct characteristics of RSAs and RSCs:
- Time Frame: RSAs are akin to an oracle in the cybersecurity sphere, providing the ability to detect possible cyber threats even before they manifest. Conversely, RSCs have more of an investigative role, revealing threats that have already happened or are happening.
- Approach: RSAs focus on the modus operandi used by virtual felons, offering insights that help us understand the perpetrator's strategy and intent. In contrast, RSCs center around the digital footprints left behind after a breach, which offer transparency about the extent of harm caused.
- Purpose: RSAs function as scouts, helping in proactive threat detection and prevention, while RSCs serve more like cyber forensics professionals, helping in post-incident recovery and data dissection.
Despite their differences, RSAs and RSCs have various commonalities:
- Aim: Both RSAs and RSCs collectively strive to strengthen an organization's bulwarks against digital invaders. Their roles are critical in the identification, prevention, and response to cyber threats.
- Data Repositories: Both these paradigms rely on a range of data inputs like comprehensive log details, network traffic behavior, and system activities to achieve their objectives.
- Deployment: RSAs and RSCs are integrated into a myriad of security instruments and platforms for efficient threat anticipation and response.
To help visualize the dissimilarities and overlaps, picture RSAs as the smoke detector in your house that alerts you of a potential fire risk before it engulfs your property. On the other hand, think of RSCs as the fire alarms that sound when a fire is already consuming your home.
Here's a comparative table further outlining the differences and similarities:
In the sections that follow, we'll delve deeper into each feature, providing a thorough understanding of RSAs and a detailed examination of RSCs. Grasping these concepts is key to fortifying cybersecurity and maximizing the utility of RSA and RSC.
Deciphering IOA and IOC: The Dual Elements Shielding Your Digital Space
In the intricate world of cyberspace safety, Indicators of Attack (IOA) paired with Indicators of Compromise (IOC) function as the dual elements making your digital stronghold unassailable. These safeguards persistently scan the digital universe, identifying and circumventing potential perils before they can inflict substantial harm. Let's dig deeper to unveil how these two facets harmonize to protect your virtual turf.
Regard IOAs and IOCs as two faces of one medallion, each possessing distinct features, yet synchronizing to fulfill a mutual aspiration - cyberspace safety. IOAs primarily aim at forewarning potential threats, while IOCs are entirely around identifying the repercussions of a successful infiltration. In unison, they weave a total security net that's simultaneously forward-looking and responsive.
Think of it in this way: IOAs act like the surveillance cameras and burglar alarms at your residence aimed at deterring a robbery. They keep tabs on doubtful activities, alerting you before any illegal entry. Conversely, IOCs emulate the investigation team that rounds up after a robbery, gathering proof while pinning down the perpetrators.
Here's a straightforward comparison table to acquaint you with the stark contrasts and commonalities of IOA and IOC:
Now, let's picture a real-life instance. Suppose your network safety mechanism spots an abnormal surge in outgoing traffic from a specific server. This could potentially be an IOA, signalling a possible data smuggling trial. The system can then undertake precautionary steps like restricting the suspicious IP access or segregate the compromised server.
On the flip side, if your system discovers a recognized malware fingerprint on one of your servers, it's an IOC. It infers a successful infiltration calling the system to initiate responsive actions like malware extermination and closing the security loophole.
Here's a basic code snippet depicting how a digital safety system might utilize IOA and IOC:
To wrap things up, IOA and IOC serve as the dual elements safeguarding your virtual domain. With IOA focusing on pre-emption and IOC on identification and response, they offer a balanced tactic to digital safety. By combining the strengths of both, you can construct a sturdy safety structure that can outlast the ceaseless onslaught of cyber threats.
A Comprehensive Examination of IOAs
In the expansive realm of digital security, Indicators of Attack (IOAs) have surfaced as a progressive method, enabling the identification and neutralization of cybersecurity risks. Marking a deviation from Indicators of Compromise (IOC), infamous for pinpointing symptoms of a sustained cyber invasion, IOAs pivot towards early detection of malicious undertakings, pre-empting potential damage. This section provides an in-depth exploration of IOAs, spotlighting their relevance, operational specifics, and their distinguishing aspects when juxtaposed with IOCs.
Deciphering IOAs
IOAs can be broadly construed as a series of data clues or recurring patterns indicating an ongoing cyber assault. These are frequently linked with standard modus operandi, techniques, and process chains employed by digital felons. IOAs can encompass anything from irregular digital traffic patterns, anomalous system responses, or aberrant user behavior.
Here, we illustrate a simple code example indicating how an IOA could potentially be detected:
In this hypothetical Python scenario, the identify_IOA function scrutinizes internet traffic for select unique patterns. If such a pattern is identified, it returns True, signaling a possible cyber assault.
IOA vs IOC: Juxtaposing the Two
As the comparative table showcases, IOAs and IOCs perform distinct roles within the digital security arena. While IOCs are key to comprehend the mechanics of a breach and to avert similar future occurrences, IOAs focus on timely detection and preclusion.
Significance of IOAs
- Prompt Identification: IOAs facilitate the recognition of cyber intrusions during preliminary stages, generally preventing any significant harm. This forward-looking approach can alleviate organizations' burden significantly concerning time and resources.
- Precautionary Measures: By deciphering the stratagems and techniques employed by cyber assailants, IOAs empower organizations to effect preventive actions to forestall digital offenses.
- Informative Threat Analysis: IOAs enrich threat analysis by revealing insights into the modus operandi of cyber felons. This valuable knowledge assists in amplify security protocols and design more potent protective strategies against cyber threats.
To sum up, IOAs constitute an integral element in a comprehensive digital security approach. By emphasizing prompt detection of cyberattacks, they afford organizations the capacity to deactivate threats prior to causing substantial damage. The upcoming chapter will concentrate on IOCs, explicating their vital part in the expansive landscape of digital security.
Unmasking IOC: A Detailed Examination
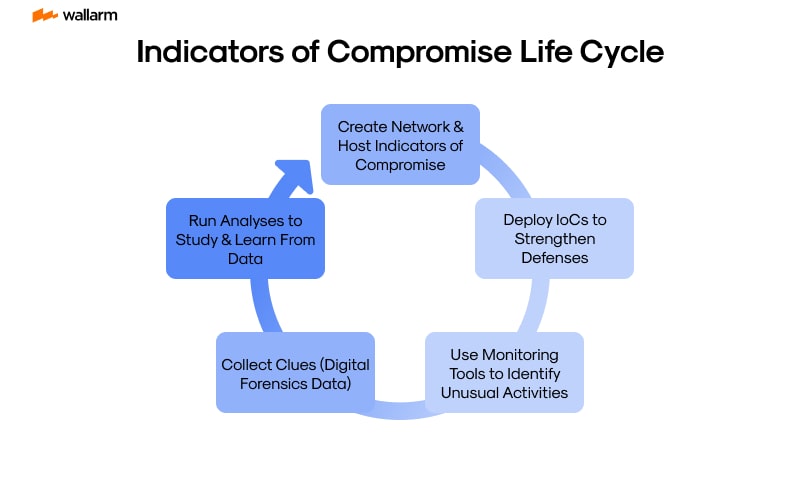
Indicators of Compromise (IOCs) are the forensic evidence of a cyber attack. They are the digital fingerprints left behind by cybercriminals during an intrusion. IOCs are used by cybersecurity professionals to detect and respond to cyber threats. They are the telltale signs that a security breach has occurred.
IOCs can be anything from IP addresses, domain names, URLs, email addresses, file hashes, or even specific patterns of behavior that indicate malicious activity. They are the bread crumbs that lead cybersecurity professionals back to the source of an attack.
Let's delve deeper into the world of IOCs and how they function in the realm of cybersecurity:
1. Types of IOCs
IOCs are classified into three main categories:
- Atomic IOCs: These are the simplest form of IOCs and include data like IP addresses, domain names, or file hashes. They are easy to use and distribute but can be easily changed by attackers.
- Computational IOCs: These include artifacts that require some level of computation to identify, such as registry key modifications or the presence of a specific file.
- Behavioral IOCs: These are the most complex form of IOCs and include patterns of behavior that indicate malicious activity, such as a sudden spike in network traffic or unusual login activity.
2. IOC Detection
Detecting IOCs involves the use of various tools and techniques. These can range from simple log analysis to more complex machine learning algorithms. The goal is to identify patterns or anomalies that indicate a security breach.
For example, a sudden increase in network traffic from a particular IP address might indicate a DDoS attack. Similarly, multiple failed login attempts from the same location could suggest a brute force attack.
3. IOC Response
Once an IOC has been detected, the next step is to respond appropriately. This could involve blocking the offending IP address, resetting compromised user credentials, or even taking legal action against the attackers.
The key is to respond quickly and effectively to minimize the damage caused by the security breach.
4. Limitations of IOCs
While IOCs are a valuable tool in the fight against cybercrime, they are not without their limitations. For one, they are reactive in nature, meaning they can only be used to detect attacks that have already occurred.
Furthermore, IOCs are often specific to a particular attack or threat actor, making them less effective against new or unknown threats. Finally, IOCs can be easily manipulated or disguised by sophisticated attackers, making them harder to detect.
Despite these limitations, IOCs remain a crucial component of any comprehensive cybersecurity strategy. By providing tangible evidence of a security breach, they allow organizations to detect, respond to, and learn from cyber attacks.
In the next chapter, we will explore how IOCs can be used in conjunction with Indicators of Attack (IOAs) to create a more robust and proactive cybersecurity posture.
Boosting Cybersecurity: The Optimal Application of IOA and IOC
The dynamic domain of cybersecurity mandates the use of Signals of Attack (SOA) and Signs of Compromise (SOC), quintessential components of an impenetrable defense mechanism. Acting as the sensory organs of your cybersecurity framework, they inaugurate a security alert system for prospective threats and invasions. Nevertheless, the effectiveness of SOA and SOC is conditional on their accurate deployment. This chapter shall delve into the apt method to utilize SOA and SOC to reinforce your cybersecurity.
1. Comprehending SOA and SOC's Function
Before we address the aspect of their apt utilization, it's vital to comprehend their functions in the ambit of cybersecurity. SOA's act as preemptive actions, spotting risks even before they have a chance to inflict damage. Conversely, SOC's are responsive actions that identify invasions post their occurrence.
2. Integrating SOA and SOC
The initial stride in leveraging SOA and SOC efficiently is their integration into your cybersecurity framework. This implies incorporating them into your security architecture and tailoring them to supervise your network for potential hazards and invasions.
Here's an uncomplicated code fragment showcasing the method to integrate SOA and SOC into a cybersecurity infrastructure:
3. Surveying and Counteracting to SOA and SOC Alerts
Once SOA and SOC are embedded, the subsequent stride involves supervising their alerts and responding accordingly. This entails scrutinizing the alerts to gauge their intensity and executing required measures to alleviate the risks or invasions.
The subsequent comparison table represents the method to react to SOA and SOC alerts:
4. Renewing SOA and SOC
Cyber risks are ceaselessly advancing, thereby demanding a concurrent evolution of your SOA and SOC. Periodic renovation ensures their capability to identify the most recent threats and invasions, implying enhancements to their risk databases and elevation of their detection calculus.
5. Equilibrium between SOA and SOC
While both SOA and SOC are significant, attaining the right equilibrium is crucial. Overdependence on SOA may trigger false positives, while excessive reliance on SOC might render your system vulnerable to intrusions. The secret lies in harmonious integration, with both complementing each other.
To summarize, an efficient utilization of SOA and SOC involves understanding their functions, accurate integration, supervision and response to their alerts, frequent upgrading, and maintaining an equilibrium between them. This method can significantly fortify your cybersecurity and shield your infrastructure from cyber threats.
FAQ
References
Subscribe for the latest news