Data Loss Prevention - What Is It?
The full meaning of DLP is Data Loss Prevention. It is an innovation intended to shield information from being presented to unapproved clients. For instance, some Microsoft Word reports contain essential data like Mastercard data and social ID. Dlp can be set to stamp records as containing delicate information, and you can decide to keep archives from being printed or messaged outside the organization.

How does Data Leakage Protection work?
DLP is essentially a compilation of regulations that characterize what information can be viewed as touchy and what activities can be performed on that information. Actually like the case test, there could be a guideline that dodges government managed retirement numbers from being informed outside of the organization. At the point when a standard is set off, the product makes the fitting move – for this situation, keeping the report from being messaged.
What is DLP good for?
DLP is one of those devices that can be extremely useful or it very well may be totally pointless – relying upon how you design it. For instance, on the off chance that you set up a standard that says Make sure that any record containing the word Social Security Number is hailed as delicate, you will label each report on the web, and you won't print messages or offer any archives that contain "federal retirement aide". That would be extremely irritating!
Where DLP can be exceptionally useful is in mix with other security innovations. It may be useful to utilize dlp in blend with other security advancements. To give an occurrence, on the off chance that you set dlp rules to check reports containing Visa numbers, and furthermore set standards to keep clients from downloading applications from the Internet, you can save a ton of time and inconvenience.
What is the usefulness of DLP?
For associations that have delicate information that should be secured, dlp is a decent apparatus. It is especially helpful in the event that you have a managed industry – for instance, a medical care association or a bank. A bank study uncovered that lion's share of associations with electronic documents and classified data had in any event one information break.
In any case, DLP is definitely not a substitute for information reinforcement. On the off chance that a programmer breaks into your organization and takes a record containing delicate data, the DLP can't help it. Moreover, dlp doesn't get against data that is taken care of in a data set or an application. To secure your data, you need to perform data reinforcement document level encryption and dlp.
What is the issue with DLP?
Dlp's significant issue isn't being idiot proof, for example you can arrange dlp to hail government backed retirement numbers and Mastercards. In the event that your document contains a government backed retirement number and a Visa number, dlp won't stamp it as containing delicate information, in light of the fact that dlp can possibly check the record or email when it distinguishes the particular information you need to secure. This is on the grounds that DLP can possibly hail documents or messages on the off chance that it recognizes the particular information you are attempting to ensure.
Also, DLP is just helpful in the event that it is empowered. For instance, numerous organizations don't empower DLP until a security break happens. Be that as it may, on the off chance that you stand by until after a security penetrate, it is past the point of no return – the harm has effectively been finished.
There are two techniques to guarantee private data encryption, while dlp encryption can keep data from being perused cautiously, yet dlp can keep data from being found. Both of these techniques are exceptionally essential.
DATA LOSS PREVENTION
As innovation continues to improve as the years progressed, a bunch of orders or guidelines should be made to shield hierarchical information from unapproved clients who need to get to delicate organization information. The measure of information that organizations create continues to increment hugely, as verified by the (IDC) International Data Corp, it was said that the all out number of information produced worldwide will clock 163 zettabytes constantly in 2025.
For simple pictorial arrangement, if those gigabytes that made up the zettabyte were in type of a block, it would be straightforwardly equivalent to 258 (200 and 58) Great Walls of china. Consequently, this makes it feasible for associations or foundations to create techniques to shield themselves from information misfortune – Data misfortune avoidance can distinguish and direct all information utilized by the association.
DLP is fundamentally an apparatus and cycle explicitly used to secure and guarantee that unapproved subjects won't be given to sensitive information. You can decide to characterize it as a bunch of rules or advances to guarantee that the touchy information of an association or establishment is effectively guided and not spilled to unapproved sources.

What Is Data Loss Prevention?
Data loss prevention (DLP) is the action of recognizing, checking, and ensuring information being used, running, and information in a capacity territory; on a work area, tablet, or cell phone. Forestalling information misfortune is completed by leading a far reaching content survey and inside and out relevant security minds all exchanges in the framework.
Be informed that the demonstration of forestalling information misfortune resembles an authority of information security or assurance approaches. DLP is a moderately old innovation (which has existed for as long as 15 years) that permits you to keep unapproved clients from getting to specific archives or information that have been set apart as delicate.
A come full circle representation is a record that contains outstandingly touchy information of people groups government backed retirement numbers, you're inside the situation to hail such chronicle as particularly or incredibly fragile, this grants you to dodge the record from being sent or printed outside your organization. The limit with regards to you to set guidelines and choose which data you regard as sensitive make the Data Loss Prevention incredibly significant within each high level association.
If it's not too much trouble, note that the deficiency of sensitive information and some other data can cause gigantic monetary misfortunes and harm the organization's standing or the character of the foundation. Presently, most organizations on the planet know about the way that they truly need to secure their information and data no matter what. Later in this article, we will give an extensive clarification of information misfortune anticipation.
Categorization Of Data Loss Prevention
The Data Loss prevention can be classified into:
- The Standard Measure
- The Advanced Measure
- The Designated System
The standard security such as anti-virus software, intrusion detection system, firewall. These products can guide computers against external threats or intrusions. By using a firewall, it can prevent strangers from entering the internal network, and the intrusion system will detect any form of intrusion attempts that strangers may make in the system. Antivirus programs that scan and detect any form of virus in the system can avoid internal intrusions.
The Advanced measure employs the machine learning, and calculations to identify irregular access to data. This makes a difference to distinguish an unusual mail trade inside the framework.
The Designated System helps to detect and quickly prevent any unauthorized attempts to send, share or copy sensitive company data either intentionally or unintentionally. This is mainly composed of those who have access to such sensitive information.
How Does Data Loss Prevention Works?
As referenced before, information misfortune anticipation is an innovation explicitly used to perform content reviews and setting keeps an eye on those information sent through any application or program. For instance, you can set up suitable principles to screen or impede the sending of government managed retirement numbers outside your organization.
Clearly, in the wake of initiating this standard, the introduced projects or programming will make a move by denying the sending of such records outside of you. Measures. The web. Information misfortune avoidance is partitioned into two classifications: endeavor information misfortune counteraction and incorporated information misfortune anticipation.
To completely comprehend the significance of "information misfortune avoidance" and how it works, it is important to comprehend those territories where content insight is not the same as setting investigation. A practically ideal approach to comprehend these two ideas and their disparities is to embrace this basic presumption that essentially accepts that the substance is as letters, and the setting is the envelope contained in the letters. Content mindfulness is the way toward wrapping an envelope and checking it to check the substance of the letter.
The setting covers the outer components that make up the letter, like the title, configuration, size, and dispersing. The rationale behind content mindfulness is the capacity to utilize setting to acquire significant data about the substance. Clearly, we need to try not to be restricted to one setting. Thus, when you open the envelope, you can see the substance of the envelope (content investigation). There are many substance investigation strategies that can be utilized to enact strategy infringement, including;
The Regular Expression
This is the most widely recognized investigation strategy in Data Loss Prevention. This strategy includes deliberate examination or assessment of a bunch of rules. An ideal model is the 16-digit number of government managed retirement numbers and charge cards. It could be said, this strategy or procedure is brilliant and simple to get to on the grounds that its standards can be effortlessly set up and dealt with, in contrast to other lumbering cycles.
Fingerprinting Database
This technique is likewise usually alluded to as precise information coordinating. The framework utilizes its own technique for finding precise matches from information base dumps or ongoing data sets. It ought to be noticed that data set moronic and ongoing information base associations ordinarily influence execution.
Record Matching
This technique doesn't examine the substance of the record, it takes the hash estimation of the document and contrasts it and the specific finger impression. It gives a low level of falsity. This strategy isn't appropriate for numerous indistinguishable yet unequaled variants.
Theoretical
This strategy utilizes a combination of word references and depictions. In the event that there are unstructured thoughts totally in opposition to customary or basic grouping, these techniques will sound a caution.
Slight Document Formatting
Fractional or slight report configurations will look for accurate matches or slight matches of explicit documents.
For instance, different renditions of structures rounded out by clients.
The Statistical Analysis
Measurable examination utilizes AI or some other factual methods, like Bayesian investigation, which can help initiate any infringement of strategy in secure substance. Filtering requires a great deal of information, the bigger the information, the better the information. If not, it will handily create erroneous positive and negative impacts. Subsequently, enormous measures of information are critical.
It is essential to take note of that there are numerous different strategies that can be utilized for content assessment. Information assurance is one of the fundamental worries of numerous associations. Information and data keep on moving through accomplices, clients, workers and other genuine people.
Numerous associations do not have the capacity to keep their information secure and to keep records and track how their information is communicated all over the place. One of the principal reasons is on the grounds that representatives utilize diverse stage channels to send and get information. This makes it hard for organizations or foundations to keep a standard method to follow the transmission of information inside the organization, which makes it muddled or hard to forestall or forestall information misfortune. The significant thing is to secure the information and not let it fall into some unacceptable hands.
Nobody needs unapproved people to get to their organization or workers and convey their data or information with them. These associations utilize numerous strategies and procedures to shield their organizations from any outer assaults or endeavor to obliterate their organization notoriety.
What is Data Loss Prevention good for?
It could be said, Data Loss Prevention might be useful in light of the fact that it can shield your information from falling under the control of the individuals who ought not be considered capable. However, practically, the main part of Data Loss Prevention is the manner by which to arrange the program, since it very well might be pointless on the off chance that it isn't as expected designed.
An ideal model is on the off chance that you build up a straightforward principle that says: ensure that any record containing a federal retirement aide number is set apart as stunning. This will consequently signal any organization that contains a government managed retirement number in the worker. The yield of this setting decides that nobody can send any record that contains a federal retirement aide number.
It would be unimaginable and terrifying to send any records containing stamped words. No printing, no mail or sharing. Since you have set the standards, this will be irritating and tiring. At the point when joined with certain security innovations, information misfortune avoidance can be exceptionally valuable.
Numerous businesses, organizations and government arrangements specify rules for the right treatment of different information. This information incorporates medical care data (HIPAA) or renowned Visa information (PCI DSS For Financial API). In the event that these guidelines are not met, they will be fined for penetrate of agreement. One of the significant parts of information misfortune avoidance is the capacity or cycle of picking a DLP arrangement, which will help distinguish the kind of information in such associations. Information misfortune avoidance arrangements will help screen or study the channels through which information streams – DLP arrangements can likewise examine information stores, (for example, workers and document offers), and afterward break down and order the substance.
An exceptionally dynamic information security relies upon the expert level of your IT staff. In this part, we coordinated a progression of motivations to clarify the significance of information misfortune avoidance for every association and friends.
Protection Of Information
The fundamental motivation behind information misfortune avoidance is to keep certain data from falling under the control of unapproved clients. The majority of the incredible associations on the planet have immense data sets loaded up with profoundly touchy data that might be identified with their purchasers, accomplices, or workers of the association.
In the event that piece of this data or information spills out of the framework, it might cause genuine damage in the event that it is given over to some unacceptable hands or individuals who need to utilize the organization. Guaranteeing the security of the information and data gave to your association is your first concern in light of the fact that a slight edge may make individuals follow through on a significant expense for it and harm the organization's standing.
Ability To Safeguard The Intellectual Property
It is normal for your organization to acquire a large amount of intellectual property rights, and these intellectual property rights need to be handled with extreme care and diligence. Therefore, you do not want such trade secrets to fall into the hands of competitors. Data loss prevention can help you protect your data. Imagine that your trade secrets have fallen into the hands of competitors. They will not only use it against you. It will be used to improve their business in the enterprise and place you below your peers, while destroying your company’s Reputation, it’s all because you choose not to protect your company from external and internal threats.
Your Data And Visibility
One of the cycles to forestall information misfortune is after you lock the information and keep it from spilling to the general population, you will know where the information is in the framework and how it is communicated in the association. DLP permits you to see your information framework. To put it plainly, this is an approach to screen and comprehend representatives who associate with delicate information inside your association.
A Plan For External Intruders Not Against Theft Or Accidental Disclosure
It is critical to take note that not all information misfortune is brought about by outer pernicious assaults. Misusing of exceptionally private data or information by workers is one of the manners in which that information misfortune happens. Because of the idea of this danger, it is hard to forestall this danger, so it is difficult to spot it before the harm is caused. Information misfortune anticipation can help recognize records containing secret data and keep them from leaving through your association's organization.
Checking Your Employees Conduct
A laborer or worker who posts one of the organization's archives to their own email with the aim of showing up on Saturday or Sunday; during recreation. This might be the kindness of the staff, yet on the off chance that the information is private to the association, this may occur, representing a colossal danger to the association. Information misfortune avoidance gives all day, every day movement. With DLP, you can restrict the quantity of workers who can get to this classified data in your association.
DLP Should Not Come As An Afterthought
Indeed it is! Forestalling information misfortune ought not be an untimely idea, which shows how significant it ought to be for each brand that has client information, particularly those that gather individual insights concerning their clients or clients. In the present innovative world, it goes from cell phones to inserted frameworks to the board programs, that is, online media programs.
This makes an exceptionally borderless internet. There are numerous forthcoming assault vectors. To meet this worldwide innovative insurgency, brands need to change themselves to adjust to this space. They need to guarantee that all touchy information is shielded and shielded from any unapproved person who needs to obtain entrance. Accordingly, obviously it is fundamental that information misfortune avoidance is essential for the significant things you ought to consider while proposing a brand. Recollect that avoidance is superior to fix.
Avoidance Of Organization Data in Cloud
Today, the vast majority utilize the cloud. There is no spot to genuinely store information. Information misfortune anticipation can assist you with recognizing those touchy information that your association has set apart as exceptionally delicate, and keep them from entering the cloud without a legitimate encryption measure, and as a rule simply shipped off those affirmed cloud applications. During the time spent progressing information to the cloud, Data Loss Prevention can help recognize those touchy information and keep them from entering the distributed storage. With DLP, you can save!
The Inside Threat
This is the center piece of the danger that covers individuals inside the association. It is quite possibly the most hard to safeguard against on the grounds that it includes the support of individuals inside the association. A genuine illustration of insider danger is somebody purposely causing organization or brand harm, perhaps because of their own disdain towards the organization.
They frequently do this without anyone else or team up with somebody outside the association space to effectively play out this activity. Accept that they can as of now effectively access delicate information that may make critical mischief the organization; monetarily or reputationally savvy. This assault is quite possibly the most risky type of breech position.
On the off chance that the individual playing out this errand is one of the organization's senior authorities, at that point he will turn out to be increasingly frightening, and he can contact nearly anything he needs to enter the organization. This type of assault isn't not difficult to forestall. Advancements, for example, Data Loss Prevention can be utilized to tag or stamp any delicate information that may wish to enter outside the association's organization.
Help In Accidental Sharing
Information misfortune avoidance encourages coincidental sharing. Individuals inside the organization may accidentally hurt the organization or put the organization's information and data in danger, yet they may become survivors of information hoodlums. These aggressors are continually searching for approaches to refresh their extortion abilities.
They for the most part direct a far reaching investigation of the objective, and afterward when they at long last track down a slight drop or escape clause in the framework, they will propose a strategy to assault the objective, and they will rapidly utilize it. After appropriately investigating their objective (association), they moved to the hands of a representative who might be the person in question.
They will remember them for the malignancy plan without the casualty's assent. At long last, the casualty will be hesitant to uncover the organization's delicate information. Yet, when legitimate information misfortune anticipation measures can forestall or forestall any endeavor to send or share touchy data that the association considers to be exceptionally delicate, it can shield the association from numerous threats!
Bad Reputation
In the event that the organization or association doesn't have sufficient security methods to control them against outer and interior dangers, this will be the result that the organization or association will confront. On the off chance that your association is continually under rehashed assaults, this will put your image in a difficult situation among your counterparts.
This has brought a progression of results, for example, losing clients, accomplices, devotees, and losing contenders. To stay away from this pitiful and terrible story, it is extremely applicable to have progressed information security in your association. In the wake of causing hurt, it's more clear the idea and guide your image from capture by accomplishing something that is required.
Significantly, forestalling information misfortune is a region that each new and old undertaking should give unique consideration to while setting up an association. From the primary day of the organization's exercises, all new information utilized, made, shared, and saved ought to be profoundly cognizant on the grounds that they are touchy. A strong establishment will assist you with keeping up your association in the course of recent years!
How Might Data Loss Prevention Help?
For organizations that have a lot of touchy information to ensure, information misfortune avoidance is a decent apparatus. This is valuable in the event that you have a lawfully required organization (like a clinical establishment, banking association, or government association) to gather the individual subtleties of its individuals. A few examinations have shown that organizations that have electronic reports and data have encountered at any rate one harm to their hierarchical information. This demonstrates the way that most establishments, for example, banks and medical care are more defenseless against aggressors. Hence, it is important to confront and conquer the difficulties that these aggressors regularly post to your association.
Furthermore, it is vital that Data Loss Prevention can't supplant information reinforcement. For instance, if a programmer can get to your arrange and get at least one record containing exceptionally touchy information, Data Loss Prevention can't direct you against such dangers. Information Loss Prevention isn't modified to help direct the information in the data set in the application. To ensure your records, exceptionally progressed information reinforcement or extremely progressed document level encryption is required, and information misfortune avoidance ought to be effectively executed to completely withstand the trial of time.
As should be obvious, information misfortune counteraction addresses three objectives that are essential to various associations. These include: individual data insurance, IP security and information perceivability.
The Personal Info Protection–If an association gathers and stores the accompanying nitty gritty data: by and by recognizable data (PII), secured wellbeing data (PHI), and installment card data (PCI), it is probably going to conform to consistence guidelines in light of the fact that HIPAA is utilized for individual wellbeing data And agree with the GDPR of EU inhabitants' very own information, which requires you as a foundation or association to ensure your clients' impeccable information no matter what. Information misfortune avoidance can help your association or organization recognize, screen, characterize and give close consideration to any movement encompassing information. This will tell you the assurance and security of this information inside the association.
The IP Protection–This is another firmly related viewpoint that needs inside and out examination. In the event that your association has exceptionally classified licensed innovation, exchange or state privileged insights, and should not be spilled, since, in such a case that it is taken by unapproved people, the organization's monetary status and hierarchical picture might be compromised. The information misfortune anticipation arrangement is like a computerized defender. It utilizes a setting based index, can order protected innovation in organized and unstructured structures, and has a progression of systems and control measures. Can shield your organization from any spontaneous information spillage.
The Data Visibility–If your association or establishment is attempting to get familiar with information development. Information misfortune anticipation can undoubtedly help your organization view and screen information in endpoints, organizations, and mists. This permits you to effectively get to how various individuals in the association connect with the information. DLP can help forestall different other undermining exercises, including the most perilous exercises; insider dangers!
Forestalling information misfortune is vital, essential and fundamental. Loss of information can seriously harm the organization's general wellbeing. Cybercriminals can take information from your association and use it for misrepresentation or use it to cause extraordinary insidiousness. Hence, it is vital to direct all information into some unacceptable hands, as this can prompt genuine outcomes. Here are a few benefits you should think about forestalling information misfortune.
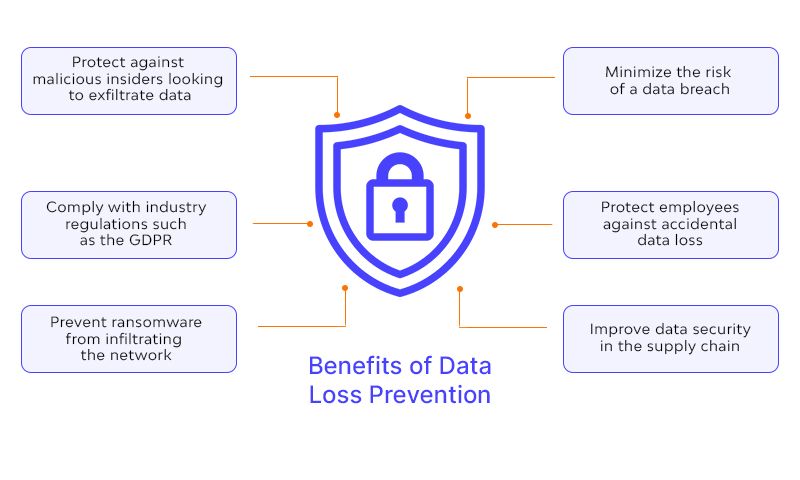
Advantages
Utilizing Data Loss Prevention innovation permits your association to screen the area and use of each information in the organization. This will tell you the information stream and who is collaborating with the information.
Information misfortune counteraction can likewise help forestall inadvertent revelation of delicate information. Inadvertently, the representative uncovered exceptionally delicate information unintentionally. Information misfortune counteraction will guarantee that such information won't be effectively erased from the organization. Then again, if representatives or association individuals who approach certain touchy information of the organization are observed by DLP, any endeavor to send such information will be hindered.
Forestalling information misfortune is helpful in keeping the organization from documenting a claim, which can extraordinarily improve the organization's picture and notoriety. This may bring about the deficiency of clients. With DLP, information can be kept from being sent to unapproved clients.
Help catch information security. It could be required during scientific investigation and to demonstrate awful conduct of representatives in the association. DLP assists with distinguishing information development inside the association.
Numerous organizations presently store their information in the cloud. Because of the presence of an enormous number of pernicious programming, these noxious programming keep on focusing on the information in the cloud, which brings incredible dangers. With encryption, this information won't be effectively open.
Information misfortune anticipation assists with encoding private information to maintain a strategic distance from information misfortune.
Each venture should think of an extremely forceful and standard information misfortune counteraction strategy. This will fill in as a proactive technique to help ensure your organization information and keep it from streaming under the control of the individuals who use it for misrepresentation or that are not helpful for the improvement of the organization. Despite colossal information misfortune, you ought not step up to the plate and create information misfortune assurance, so as not to make your organization or venture into inconvenience. Build up a solid information misfortune counteraction strategy and comprehend the tremendous benefits of securing organization information.
What Are The Problems With Data Loss Prevention?
There is no perfect thing. DLP also has its problems. One of the main problems with data loss prevention is that it cannot maintain its foolproof nature. If your file contains social security numbers and credit card numbers, Data Loss Prevention will not place them as containing sensitive data. The main reason for this is that Data Loss Prevention can only mark files or emails that only contain the exact data you want to protect. If Data Loss Prevention is enabled, you can only use this function, without enabling this technology, there is a risk of attack.
Over time, many companies have become accustomed to not enabling data loss prevention until violations occur. Waiting for the gunshot to happen before activating Data Loss Prevention is like someone waiting for a deadly disease and starting to find a cure. It can be said with certainty that this behavior is absurd, because the behavior has been completed and may seriously damage the growth of the company. There are two ways to prevent sensitive data. They include encryption and data loss prevention. Encryption helps prevent data from being read, and Data Loss Prevention can prevent data from being leaked. When dealing with data security, these two methods are very necessary.

It must be pointed out that some large companies in the world are still suffering from security breaches. This does not mean that they do not have proper data loss prevention security, but that they are still suffering from security breaches. Because of the many benefits it brings, it also brings some questions that should be understood correctly:
It requires Classification
Data loss prevention requires classification to actively monitor sensitive data or information on the network. Traditional data loss prevention requires knowing the exact location of such sensitive data, and then attaching such information to policies and labels. This is the so-called classification. Classification is a very critical aspect to prevent data loss. It is a very complicated process and very time-consuming. If the data is classified incorrectly, traditional data loss prevention will not know whether the organization’s sensitive data is leaking.
Data Loss Prevention Does Not Work With SaaS file Sharing
Well-known SaaS file sharing application; in Google Drive, Dropbox does not rely on data transmission between processing programs, but distributes by directly linking to the content itself. Traditional Data Loss Prevention cannot understand these peer-to-peer sharing, and therefore cannot fully access the data movement in the space. For example, when a person invites someone or adds someone to a Google document, it only gives a slight indication of the content in the document. Therefore, traditional Data Loss Prevention solutions cannot correctly understand the link.
Data Loss Prevention Cannot Give Awareness Into Shady Communications
Traditional data loss prevention cannot understand any suspicious interactions via email or any other messaging platform. Therefore, it is clear that if two employees unite to use the company’s sensitive data for fraud or sell it to a competitor, they decide to use email, which would not be detected by traditional Data Loss Prevention because it cannot do so.
The Incapacity To Impose The Data Use And Handling Policies
It is not enough to formulate policies without enforcing them. Data loss prevention can help you understand how employees move data and how they violate organizational security policies. It is important to formulate a policy and implement it at the same time.
As the number of people using Internet space continues to increase, from thousands to millions, the number of people in Internet space has reached billions. This clearly shows the need to prevent data. DLP is an important aspect of any organization. Strictly protecting the sensitive data of users or customers should become a top priority for every company. When you consider building an organization, the most important thing is to come up with "data loss prevention".
FAQ
References
Subscribe for the latest news