Booters, Stressers and DDoSers
What are booter administrations?
Booters, frequently known as booter administrations are mainstream DDoS (Distributed-Denial-of-Service) that are offered by brilliant hoodlums to assault and cut down sites and secure organizations. To lay it out plainly, booters are alluded to as ill-conceived approaches to utilize IP stressors.
Illicit utilization of IP stressors is embraced to darken the personality of the assailants using intermediary workers. The intermediary reroute's the association of the assailants while additionally concealing their IP address. It could make it hard to identify when or where the assault is going on.

Booters might be veiled as SaaS (Software-as-a-administration) with the utilization of email backing and YouTube instructional exercises. Some specialist co-ops may offer a one-time administration, various assaults for a predefined period, or may even be fit for lifetime access.
An overview of IP stresser
An IP stresser is an apparatus that is intended to test the organization or worker to decide how powerful it is. The manager of the framework may choose to run a pressure test to distinguish if the current assets (transmission capacity, CPU, etc) are adequate to deal with any extra burden that the framework needs to deal with. You wouldn't have any desire to run a framework that splits up at any slight expansion in load.
Setting aside time by and by test your organization or worker is an extraordinary method to utilize an IP stresser. On the off chance that you attempt to run it against another person's organization or worker, you cause a forswearing of administration for their real clients, which is an unlawful demonstration in numerous nations throughout the planet.
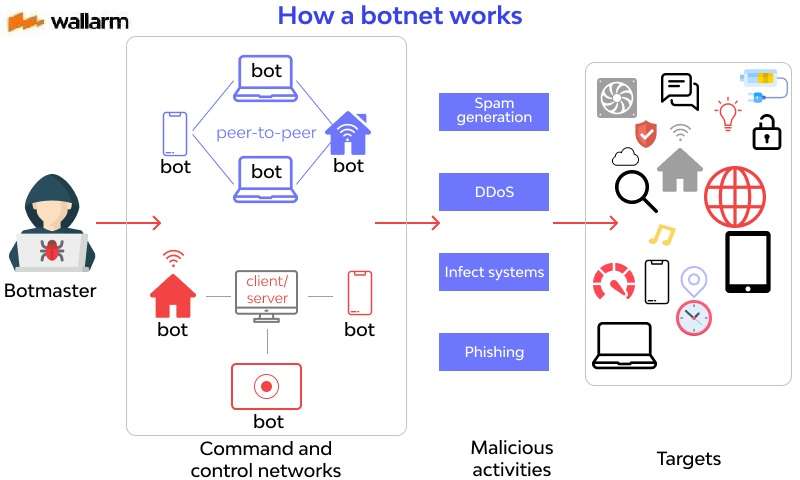
What is a botnet? DDoS for employ
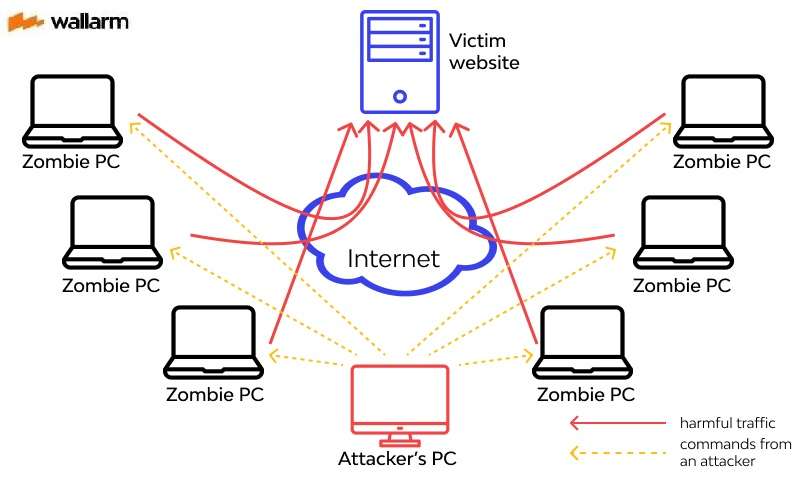
DDoS is a term that represents Distributed Denia of Service, which is a malignant endeavor to guarantee that a worker or an organization asset is inaccessible to its real clients. Digital assailants can do this by stacking the organization with bunches of phony traffic that keep clients from interfacing with their administration.
Ordinarily, DDoS assaults are utilized as an instrument by programmers and hacktivist gatherings. These kinds of assailants are viewed as crafted by just the expert hooligans who know precisely the thing they are doing.
As of late, we have had a surge of DDoS-for-enlist administrations (otherwise known as stressors or booters). This has further developed the passage access of programmers and now offers them the choice to assault any objective, for lesser than a hundred dollars. At the point when you consider how expansive programmers can get, you comprehend the danger of this turn of events.
The expanded passage access makes it urgent for associations to find ways to shield themselves from being breaks. As more individuals keep on utilizing the web, there will be more cybercrimes executed and masked as-a-administration items.
Opening Infected Systems
The most ideal approach to comprehend what DDoS for enlist implies is by investigating what the "item" signifies. To lay it out plainly, these DDoS administration items are typically offering admittance to DDoS botnets. These botnets are organizations of malware-tainted PCs that wind up being subleased to supporters of the item.
It's awful news that building a botnet is a genuinely straightforward interaction. The harm can be extensive when you consider that the assault is performed by a bunch of ruined PCs. If one degenerate PC is compelling, envision how they would proceed as a bunch.
To show you that it is so natural to fabricate a botnet, a basic web search by any bot-net designer would uncover a few prestigious botnet developer devices that accompany a total arrangement of guidelines or a functional manual.
These units are generally intended to contain bot payload and CnC (order and control) records. Utilizing these units, hopeful bot designers can start to convey and create malware that is equipped for contaminating gadgets by sending spam mail, degenerate weakness scanners, animal power assaults, etc.
With enough assets, for example, web associated gadgets, degenerate PCs, and cell phones and endeavors, another botnet would be made – prepared to assault, penetrate and accomplish somebody's messy work as long as they will pay for the help.
What precisely are Stressers and Booters utilized for?
There's no denying the way that botnet building packs are accessible all over and numerous programmers would barely need to invest an excessive amount of exertion to make botnet overnight.
DDoS assaults are unmistakably illicit, and offering admittance to these undermined PCs is similarly unlawful. This implies the leaser and leasor of a botnet are carrying out the wrongdoing. The present circumstance is typically trying for some DDoS-for-employ "specialist co-ops" who need to direct obscure demonstrations in the open with a wide admittance to an enormous number of individuals.
While trying to separate what they are utilized for, some DDoS-for-employ decide to call their items "stressers" – which are administrations that can be utilized to test how intense your worker is. Notwithstanding, stressers don't put a particular impediment on having the option to just test the strength of your worker. It very well may be to test various sorts of target workers. Stressors will permit you "stress test" essentially anybody or anything, supporting cybercrime, defacement, and different sorts of DDoS – related exercises.
In any case, there are those botnet proprietors and specialist organizations who like to depict the item precisely for what it's worth and allude to them as "sponsor" or "dose" administrations. The administrations offered by the two kinds of items are comparative and there are no approaches to separate between a booter, ddoser, and stresser.
By the day's end, that load of terms alludes to DDoS for enlisting, with some sellers misusing some lawful escape clauses to work undetected. It is impossible to decide the authenticity of the pressure tests performed by these items.
What are the necessities to lease a DDoS administration and what amount precisely do you need to complete it?
Truly you needn't bother with a ton to lease a botnet. All you need to do is get a PayPal account, a decided objective or targets, and the craving to carry out wrongdoing or overstep the law.
It might sound genuinely basic yet the legit truth is that in this day and age, anybody can utilize a stresser to absolutely upset an objective site for a little amount of cash. To find stresser sellers, you don't need to look into the profound corners of the dull web. It's just about as basic as a direct Google search.
Booters and Stressors have received a comparable SaaS (programming as a help) plan of action, that clients can buy-in for. Programmers can appreciate a staggering measure of inclusion from utilizing stressors and booters as long as they can keep up with their memberships. As per DDoS reports, a DDoS bundle would cost the client between $20 - $38 each month.
The Dangers of Booter Services
Asides from the conspicuous danger of expanded instances of cybercrime and information penetrate, a significant risk that the broad admittance to powerful DDoS administration will be the arrangement of another sort of crooks – those with just a little information however enough instruments to cause generous harm.
The peril brought about by having various botnets available for use, in this way, runs further than their capacity to mess up a framework paying little mind to how ruinous they end up being. If these DDoS-for-enlist administrations are permitted to work with no governing rules, they can be a threat to the whole online local area, particularly SaaS and internet business sites that depend on client trust, dependability, and accessibility.
Instructions to alleviate botnet assaults
DDoS assailants appear to assault the center foundations of the web, devastating youthful online firms that are not as equipped for fighting off DDoS dangers and are undeniably more presented to DDoS blackmail plans.
Cybercrime ought not to be seen as a sub-class of wrongdoing, overlooked in reality and just existing on the internet. All things being equal, it ought to be viewed as another type of crime that cuts across the line and can influence various web clients across the world on the double. Stressors and booter administrations can essentially be portrayed as a side-effect of another reality where administrations can undoubtedly be bought to assault businesses and associations. This implies that a few associations are allowed to work in a questionable hazy situation.
The truth of the matter is that stressors, booters, and other DDoS-for-recruit instruments are digital weapons that have become progressively well known, and their perpetual accessible requests quick reaction. Read in this article how to stop DDOS attack
FAQ
A: Booters, Stressers, and DDoSers are cyber attack tools that flood a website or network with traffic to overload and crash its servers, causing sites and services to become unavailable.
A: Booters, Stressers, and DDoSers work by overwhelming a target with more traffic than it can handle. They use botnets, networks of infected computers, to direct large amounts of traffic to the victim's site or network.
A: While Booters, Stressers, and DDoSers were initially developed for legitimate stress testing of websites and networks, they are predominantly used for malicious purposes.
A: Yes, using Booters, Stressers, and DDoSers for a DDoS attack is illegal in many countries and can result in criminal charges and penalties.
According to an article on TechRepublic, "DDoS attacks: A cheat sheet for professionals" by Brandon Vigliarolo, the use of Booters, Stressers, and DDoSers pose a significant threat to businesses and organizations, causing downtime, financial loss, and reputational damage. The article provides an overview of the different types of DDoS attacks and ways to mitigate them.
References
Subscribe for the latest news









%20Attack.jpg)







