Automated Fingerprint Identification System - AFIS
What is AFIS?
The automated fingerprint identification system (AFIS) can be characterized as a biometric arrangement that is comprised of a full information base of fingerprints. The reason for the framework is to look through the information base and contrast it against known fingerprints inside the information base. AFIS needs to look over a huge number of information to arrive at a specific outcome. In this day and age, this kind of framework can look through near billions of fingerprints in as little as a second. These living beings are intended to have the option to look with 100% exactness.
The AFIS is a biometric framework that distinguishes various people with computerized imaging innovation. This innovation can be utilized to get, store and examine unique finger impression information. This extraordinary ID framework was at first taken on to be utilized by the Federal Bureau of Investigation (FBI) to close criminal cases. After some time, this recognizable proof framework was utilized for general ID and recognition of extortion in shut frameworks. Fingerprints are a dependable type of individual recognizable proof and it's a refined framework that has been utilized oftentimes and is even acknowledged by the legal arrangement of numerous nations. The AFIS has been in use for around 25 years now. In our cutting-edge society, there is a further developed type of AFIS that is alluded to as plain-impression live filtering. Various sellers produce AFIS-related hardware and valuable projects.

Automated Fingerprint Identification System History
The AFIS is a valuable framework that is progressively being taken on by various quarters throughout the planet. Yet, when was it made?
The principal AFIS was made by the Federal Bureau of Investigation (FBI) in 1974. The principal framework was intended to contain just alleged details or significant pieces of a unique finger impression since they considered it too costly to even think about putting away full pictures. This framework was not the quickest or most productive framework but rather with current upgrades, there have been helpful changes.
The principal framework was massive and comprised of various PCs that occupied the whole room. Notwithstanding, they made inquiry times more limited. It took the police division over a month to look at fingerprints and get a match in a paper information base. However, these PCs had the option to finish a comparative correlation in around 30 minutes. Utilizing the present frameworks, the whole inquiry should be possible inside the flicker of an eye or a couple of moments.
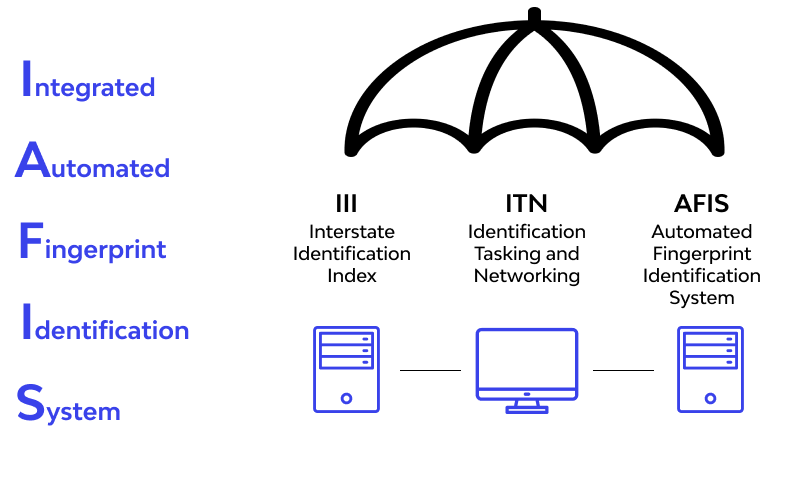
The FBI ABIS framework is as yet useful and the department alludes to it as an IAFIS (Integrated Automated Fingerprint Integration System). There are times when the AFIS and IAFIS are utilized instead of each other, yet there are slight contrasts between the two ideas. The primary Innovatrics AFIS was set up in 2009. The framework has been intended to perceive fingerprints, palmprints, and facial elements including irises. A framework that utilizes different pieces of the body to distinguish people is known as the Automated Biometric Identification framework.
What are AFIS Biometric Systems?
The AFIS is planned with a biometric framework that contains pictures of people's fingerprints, palmprints, and impressions. This framework may likewise contain different types of individual data that can be utilized to recognize a person. The data to be remembered for the information base might come from criminal examinations and other solid sources including biometric common registers.
The information base might be loaded up with layouts gotten from source pictures that permit speedy hunts to be directed through the data set. With these layouts, the AFIS can be utilized to coordinate with up-and-comers. When utilizing the right sort of hardware, it's feasible to get to the data that is contained on the information base through field PCs. This will make it simpler to recognize wrongdoing casualties or survivors of cataclysmic events that permit the speedy administration of help.
When managing explicit applications, the AFIS data set can be utilized to arrange a debacle recuperation stage. These stages might be intended to work for a specific timeframe and can be utilized to offer particular types of assistance, for example, during line control.
How AFIS is utilized in Cybersecurity?
The capacity of this unique system to look through different records inside the flicker of an eye helps the police officers when attempting to distinguish suspects, casualties, hoodlums, or individuals with no apparent method for ID. The AFIS can decide the nature of the match killing any potential blunders or errors.
While surveying a prime location, it's fundamental that the police can recognize the fingerprints of the typical tenants or clients of property and separate them from those of expected suspects. To do this, the AFIS is significant because it offers speedy outcomes within an exceptionally brief timeframe. This framework can likewise be utilized to order fingerprints from a bunch of people, decreasing the time it takes to look through the record. With the utilization of these classifications, searches are less mind-boggling. In specific cases, it just requires a couple of hours to recognize speculation and catch them.
AFIS vs. IAFIS
- AFIS
This system is utilized to portray a computerized framework that is utilized to sort, look at and trade advanced unique mark data. The AFIS is helpful where you need to deal with numerous unique finger impression records that would somehow or another set aside a great deal of effort to dissect. The AFIS information base might contain billions of known and obscure fingerprints. At the point when another unique finger impression is thought about against others, it might require hours relying upon the record it's being analyzed against. Biometric frameworks are utilized for business applications, while AFIS frameworks are used by law authorization and security offices. Unidentified fingerprints will be put away for future reference while connecting various episodes.
- IAFIS
The IAFIS is a fingerprint identification system that was made and constrained by the FBI. It was set up in 1999 and from that point forward has been utilized by the FBI and other security organizations. As indicated by the FBI, there is a huge assortment of fingerprints and criminal history inside the IAFIS. IAFIS can likewise be utilized to perform programmed unique finger impression looks check through advanced pictures, inert hunt, and trade accessible finger impression information. The IAFIS houses a huge number of criminal and psychological oppressor records including those of common subjects.
What you can do with Stolen Fingerprints?
Suppose a programmer was to break into the AFIS and take a huge number of fingerprints. What might be his next strategy?
Fingerprints, in contrast to different methods for recognizable proof, can't be changed or modified. Thus, there is a probability that such taken data would be used for spycraft rather than normally distinguish robbery. The information could be offered to unfamiliar state-run administrations or fear-monger associations. It could likewise be utilized to recognize covert law authorization specialists and make new bogus characters.
FAQ
References
Subscribe for the latest news