WebSocket protocol
WebSocket allows us to create “real-time” applications which are faster and require less overhead than traditional API protocols. Sometimes referred to as a high-end computer communication protocol, WebSocket is needed to establish the client-server communication channel. In this post, we’ll dig into what WebSocket is, how it works, and some of the associated security issues which should be addressed.

How do WebSockets work ?
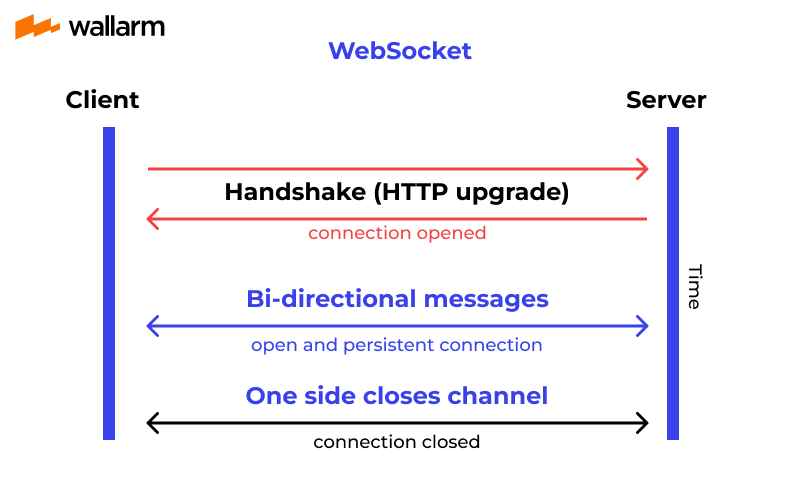
As per the conventional definition, WebSocket is a duplex protocol used mainly in the client-server communication channel. It’s bidirectional in nature which means communication happens to and fro between client-server.
The connection, developed using the WebSocket, lasts as long as any of the participating parties lays it off. Once one party breaks the connection, the second party won’t be able to communicate as the connection breaks automatically at its front.
WebSocket need support from HTTP to initiate the connection. Speaking of its utility, it’s the spine for modern web application development when seamless streaming of data and assorted unsynchronized traffic is concerned.
Why is a Web Socket Needed and When Should it be avoided?
WebSocket are an essential client-server communication tool and one needs to be fully aware of its utility and avoid scenarios to benefit from its utmost potential. It’s explained extensively in the next section.
Use WebSocket When You Are:
- Developing real-time web application
The most customary use of WebSocket is in real-time application development wherein it assists in a continual display of data at the client end. As the backend server sends back this data continuously, WebSocket allows uninterrupted pushing or transmitting this data in the already open connection. The use of WebSockets makes such data transmission quick and leverages the application's performance.
A real-life example of such WebSocket utility is in the bitcoin trading website. Here, WebSocket assist in data handling that is impelled by the deployed backend server to the client.
- Creating a chat application
Chat application developers call out WebSocket for help in operations like a one-time exchange and publishing/broadcasting the messages. As the same WebSocket connection is used for sending/receiving messages, communication becomes easy and quick.
- Working up on gaming application
While gaming application development is going on, it’s imperative that the server is unremittingly receiving the data, without asking for UI refresh. WebSocket accomplish this goal without disturbing the UI of the gaming app.
Now that it’s clear where WebSocket should be used, don’t forget to know the cases where it should be avoided and keep yourself away from tons of operational hassles.
WebSocket shouldn’t be taken on board when old data fetching is the need of the hour or need data only for one-time processing. In these cases, using HTTP protocols is a wise choice.
WebSocket vs HTTP
As both HTTP and WebSocket are employed for application communication, people often get confused and find it difficult to pick one out of these two. Have a look at the below-mentioned text and gain better clarity on HTTP and WebSocket.
As told previously, WebSocket is a framed and bidirectional protocol. On the contrary, to this, HTTP is a unidirectional protocol functioning above the TCP protocol.
As WebSocket protocol is capable to support continual data transmission, it’s majorly used in real-time application development. HTTP is stateless and is used for the development of RESTful and SOAP applications. Soap can still use HTTP for implementation, but REST is widely spread and used.
In WebSocket, communication occurs at both ends, which makes it a faster protocol. In HTTP, the connection is built at one end, making it a bit sluggish than WebSocket.
WebSocket uses a unified TCP connection and needs one party to terminate the connection. Until it happens, the connection remains active. HTTP needs to build a distinct connection for separate requests. Once the request is completed, the connection breaks automatically.

How are WebSocket connections established?
The process starts with a WebSocket handshake that involves using a new scheme ws or wss. To understand quickly, you may consider them equivalent to HTTP and secure HTTP (HTTPS) respectively.
Using this scheme, servers and clients are expected to follow the standard WebSocket connection protocol. The WebSocket connection establishment begins with HTTP request upgrading that features a couple of headers such as Connection: Upgrade, Upgrade: WebSocket, Sec-WebSocket- Key, and so on.
Here is how this connection is established:
- The Request
Connection: Upgrade header denotes the WebSocket handshake while the Sec-WebSocket-Key features Base64-encoded random value. This value is arbitrarily generated during every WebSocket handshake. Besides the above, the key header is also a part of this request.
The above-listed headers, when combined, form an HTTP GET request. It will have similar data in it:
To clarify, Sec-WebSocket-Version, one can explain the WebSocket protocol version ready to use for the client.
- The Response
The response header, Sec-WebSocket-Accept, features the zest of value submitted in the Sec-WebSocket-Key request header. This is connected with a particular protocol specification and is used widely to keep misleading information at bay. In other words, it enhances the API security and stops ill-configured servers from creating blunders in the application development.
On the success of the previously-sent request, a response similar to the below-mentioned text sequence will be received:
WebSocket Protocol
WebSocket protocol is a type of framed protocol that involves various discrete chucks with each data. It also deploys a frame type, data portion, and payload length for proper functioning. To have a detailed understanding of WebSocket protocol, knowing its building block is crucial. The foremost bits are mentioned below.
- Fin Bit is the fundamental bit of the WebSocket. It will be automatically generated when one begins the connection.
- RSV1, RSV2, RSV3 Bits are bits reserved for further opportunities.
- Opcode is the part of every frame and explains the process of interpreting the payload data of a particular frame. Some of the common opcode values are 0x00, 0x0, 0x02, 0x0a, 0x08, and many more.
- Mask bit activates when one bit is set to 1.
WebSocket demands the use of a client-picked random key for all the payload data. Masking key, when combined with payload data, assists payload data sharing in an XOR operation. Doing so holds great importance from the application API security as masking keeps cache misinterpreting or cache poisoning at bay.
Let’s understand its crucial components in detail now:
Payload len
This is used for the total length encoding of the payload data in WebSocket. Payload len is displayed when the encoded data length is less than 126 bytes. Once the payload data length is exceeded from 126 bytes, additional fields are used for describing the payload length.
Masking-key
Every frame that the client sends to the server is masked with a 32-bit value. The masking key displays when the mask bit is 1. In the case of 0 as the mask bit, the masking key will be zero.
Payload data
All sorts of arbitrary application data and extension data are known as payload data. The client and servers use this data for negotiation and are used in the early WebSocket handshakes.
Conclusion
WebSocket enables two-way interactive communication sessions between client and server without having to poll the server for a reply, providing both speed improvements and real-capabilities over other protocols. But as with all applications, using WebSocket entails both careful programming practices and run-time protection to guard against a unique set of threats. This API defense-in-depth strategy will improve protection for both your users and your organization compared to traditional approaches.
And also don't forget about security, try the reliable solution from Wallarm - API Security Platform
FAQ
References
Subscribe for the latest news